
We’ve just received a new sample – a program called RedBrowser, a Trojan for mobile phones which can run Java applications (JME2). This means that it’s not just smartphones that are potentially infectable, but most modern handsets.
It presents itself as a program which will allow the user to visit WAP sites without a WAP connection. However, the Trojan actually sends SMSs, not to other users, but to premium rate numbers. The user gets charged $5 – $6 for each sms sent.
Happily, this Trojan can be easily deinstalled by the user using standard tools.
Although this is the first sample we’ve seen, there are probably other similar programs out there in the wild. It’s a sign that virus writers are widening their reach, and no longer only targeting smart phones.

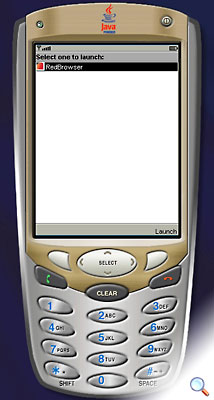





















Trojan for handsets which run Java applications