
Because sometimes you can't teach an old malware developer new tricks
There’s nothing new in Brazilian cybercriminals trying out new ways to stay under the radar. It’s just that this time around the bad guys have started using a method that was reported in the wild years ago.
Russian gangs used this technique to distribute malware capable of modifying the hosts file on Windows systems. Published by McAfee in 2013, the UTF-8 BOM (Byte Order Mark) additional bytes helped these malicious crews avoid detection.
Since these campaigns depended on spear phishing to increase the victim count, the challenge was to fool email scanners and use a seemingly corrupted file that lands in the victim’s inbox.
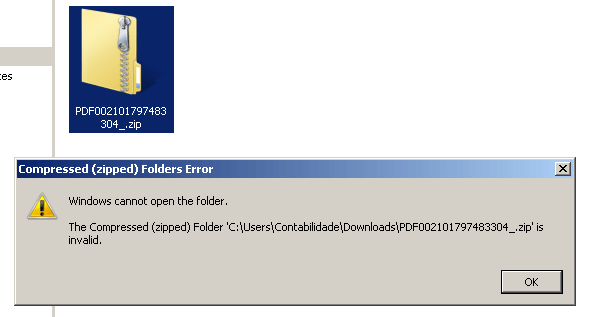
The first indicator appears when the user tries to open the ZIP file with the default file explorer and sees the following error:
The error message suggests the file is corrupt, but when we check its contents we see something strange in there.
Instead of having the normal ZIP header starting with the “PK” signature (0x504B), we have three extra bytes (0xEFBBBF) that represent the Byte Order Mark (BOM) usually found within UTF-8 text files. Some tools will not recognize this file as being a ZIP archive format, but will instead recognize it as an UTF-8 text file and fail to extract the malicious payload.
However, utilities such as WinRAR and 7-Zip ignore this data and extract the content correctly. Once the user extracts the file with any of these utilities they can execute it and infect the system.
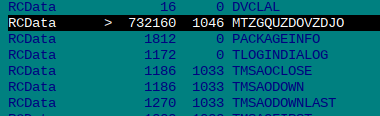
The malicious executable acts as a loader for the main payload which is embedded in the resource section.
The content stored inside the resource, encrypted with a XOR-based algorithm, is commonly seen in different malware samples from Brazil. The decrypted resource is a DLL that will load and execute the exported function “BICDAT”.
This library will then download a second stage payload which is a password-protected ZIP file and encrypted with the same function as the embedded payload. After extracting all the files, the loader will then launch the main executable.
The final payload that’s delivered is a variant of a Banking RAT malware, which is currently widespread in Brazil and Chile.
Kaspersky Lab products can extract and analyze compressed ZIP files containing the Byte Order Mark without any problem.
Indicators of compromise
087b2d745bc21cb1ab7feb6d3284637d
3f910715141a5bb01e082d7b940b3552
60ce805287c359d58e9afd90c308fcc8
c029b69a370e1f7b3145669f6e9399e5
The return of the BOM




























Shara
Help I think my computer is infected