
Online antivirus services such as VirusTotal (www.virustotal.com) and VirusScan (http://virusscan.jotti.org) have been around for a few years now. Services like this mean that any user can scan a suspicious file for malicious code online. These services differ from the online scanners offered on antivirus vendor sites by scanning files with several antivirus products simultaneously. For instance, VirusTotal currently uses 32 antivirus products to check suspicious files!
But as so often happens, something that can be used for good – helping users check the integrity of their files – can also be used by virus writers. They quickly caught on to the fact that services like the ones mentioned above could be used to test how well their creations can evade popular antivirus solutions. If a new Trojan or worm can be detected by an antivirus, the author will deliberately modify it until it isn’t detected any more. The result? The heuristics used in the vast majority of antivirus products are helpless when confronted by such carefully prepared malicious programs.
By default, VirusScan, VirusTotal and other services send all suspicious files to antivirus companies. If a file is detected by, say, 10 antivirus products, and the other 22 don’t detect it, the file will be sent to the 22 relevant virus labs for analysis and to be added to the antivirus database. This significantly reduces the time taken by antivirus companies to react during epidemics and also increases the overall detection rate. If the user doesn’t want a file to be sent to the antivirus company, then s/he has to disable this option when scanning the file.
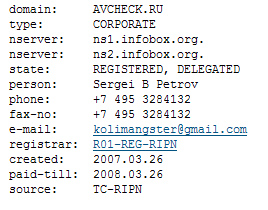
However, there’s a rumour in virus writing circles that all files are sent to virus labs, regardless of whether or not the option is enabled. Cyber criminals are now offering a solution for the tin-foil hat brigade – similar services designed expressly for virus writers. You have to pay to use the service, but there’s a guarantee that no file will be sent to an antivirus company.One example is AvCheck.ru. The creators of this site offer to scan files using 15 antivirus programs and ‘guarantee privacy for you and your files’. Of course they want money for it – a dollar per file.
We can only admire the entrepreneurial spirit behind this site. But we’re not going to wish them success. And after all, the site could be closed at any moment, and a court case could be raised against the creators of the site by the antivirus companies whose products are being used in clear violation of license agreements.
The darker side of online virus scanners























Mr.NoBody
Thanks..people need some education about this