
Kaspersky Lab, a leading developer of secure content management solutions, presents its latest report on spam activity.
Spam in mail traffic averaged 78.9% in July 2008. A low of 66.2% was recorded on 16 July, while a high of 88.9% occurred on 11 July. The share of graphical spam was 9%.
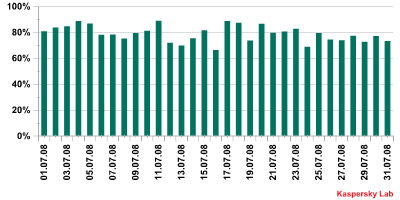
Spam in mail traffic in July 2008
The number of spam messages containing malicious attachments and links to phishing sites fell considerably in July. Messages with links to phishing sites accounted for just 0.58% of all mail traffic – half the previous month’s figure – while 0.27% of messages contained malicious files. Spammers tried to make up for this shortfall in the second half of the month by mass mailing messages that contained links to infected web sites. The messages contained sensational news headlines designed to tempt users into clicking on the links. A number of mailings also invited the recipient to download free antivirus software, although the program actually turned out to be a Trojan-Downloader program.
The top five leading spam categories remained unchanged in July with medications, health-related goods and services (18%) in first place, followed by travel and tourism (14%), adult content spam (12%), education (8%), and fake designer goods (7%).
Naturally, the increasing popularity of social networking sites attracts spammers and hackers who use the sites for their own purposes. Although spammers haven’t yet exploited the existence of such sites when advertising everyday goods and services, the topic of social networking frequently accompanies links to malicious programs and offers of hacking and spamming software. For example, spammers offered users of the popular Russian social networking site Odnoklassniki.ru (the Russian equivalent of Classmates/ Friends Reunited) a utility that would automatically enter the user’s login and password when s/he accessed his/ her personal page. This “useful” tool actually turned out to be Trojan-PSW.Win32.SocNet.a. This malicious program does enter the login details automatically, but also forwards the user’s personal data to the remote malicious user’s site. Fake notifications about messages received from Odnoklassniki.ru, which contained a link to an infected site, were also circulating in mid-July. The last few days of July brought a mass mailing inviting the recipient to register on the Friends portal – the messages were allegedly sent by a user on that network. The link in the message didn’t work, but presumably it was designed with the same goal as the spam imitating messages from Odnoklassniki.ru. Once again this case highlights the potential threat to users of invitations or offers sent from unknown addresses.
Spam which is not related to social networks is mostly criminal spam. This category includes negative PR targeting a range of organizations and resources, links to malicious programs or infected sites, advertising for fake and counterfeit goods, and offers of criminal services and software which can be used for hacking and spamming activity. All of this points to the on-going criminalization of spam.



















Spam report: July 2008