
Contents
- November in figures
- Spam in the spotlight
- Sources of spam by country and region
- Malicious attachments in email
- Phishing
- Conclusion
November in figures
- The share of spam in mail traffic continues to fall; in November it dropped by 5.1 percentage points and averaged 62.9%.
- The percentage of phishing emails in mail traffic halved from October and amounted to 0.015%.
- Malicious programs were detected in 3.27% of emails, up 0.02 percentage points from the previous month.
Spam in the spotlight
Holidays, natural disasters, and other pretexts for spam
Spammers and scammers always take advantage of holidays and hot news. As we approach the Christmas and New Year holidays, spammers now have more reasons and opportunities to advertise their goods and services in spam. Recent disasters were also used by scammers to extort money.
Compassionate scammers
Two tragic events took place in November: Hurricane Sandy in the US, which resulted in the loss of many lives, and flooding in the Dominican Republic. These events were used by phishers trying to get their hands on the personal data and cash of Internet users.
In the case of Hurricane Sandy, scammers asked for donations to rebuild roads, bridges, and restore the power supply. In the case of the floods, scammers reported that schools were flooded and required humanitarian aid. In both cases, the emails include links to websites where users are asked to enter their credit card details.
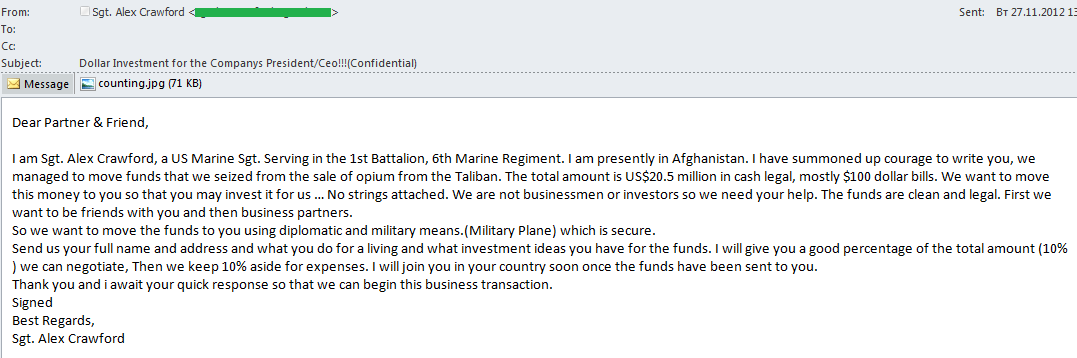
A new topic in Nigerian scam letters
So-called Nigerian scam letters represent one type of fraudulent spam. Typically, these spam emails contain requests for assistance in obtaining or transferring money for a fee in return, and generally refer to actual events, famous people, or large companies. Often, they tell a tale about the death of a wealthy relative or client who has bequeathed a large amount of money that needs to be taken out of the country. The scammers try to make the fabricated story sound as believable as possible.
Given the typical phishing pretexts, it was a bit unusual to see an email allegedly from an American serviceman who had managed to intercept Taliban funds generated from opium sales. The spammer proposed a joint investment of the “clean” money, since he had no experience in financial matters.
Users who set their sights on money from such a dubious source will more likely than not have to send funds to cover “organizational costs”.
Tis the season
Traditionally, as Christmas and New Year approach, we see a surge in the number of holiday-themed mailings. The most prevalent service advertised in spam ahead of the New Year is event management for corporate holiday parties, often promising a guest appearance from Santa Claus. It’s also common to see offers to prepare souvenirs with company branding (such as sweets or candies packaged with the company logo).
Some spam mailings are designed to look like holiday e-cards containing both holiday wishes and advertising. The most creative emails appear to be intricately decorated Christmas cards. The services advertised include the development of a variety of Internet and mobile apps, but do not necessarily have any connection whatsoever to Christmas or the New Year.
Readers may recall that many holiday-themed mailings in November used graphic spam, both in order to get recipients’ attention, and to bypass spam filters.
Can’t buy me love?
In November, an unusual mailing was addressed to companies and Internet users wishing to boost their popularity on Facebook by buying “likes”.
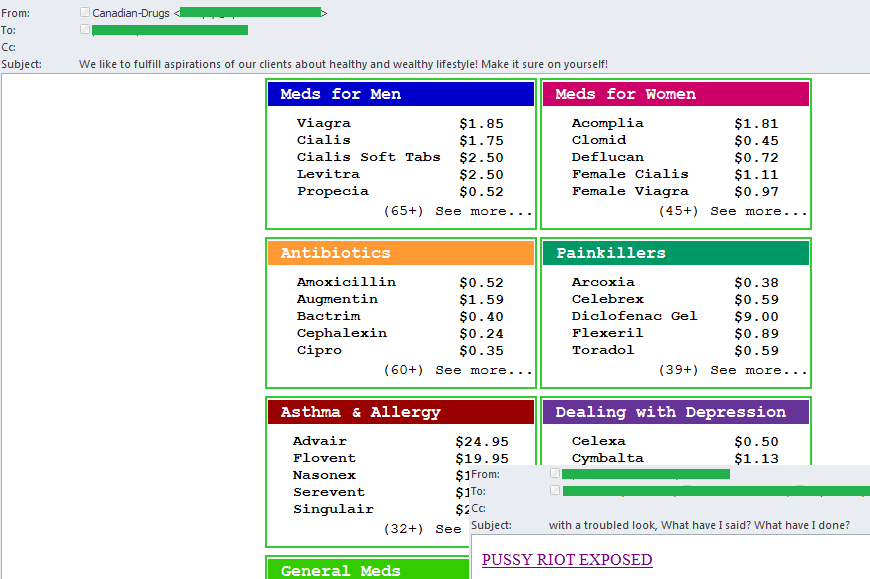
Pharmaceutical spam
The spammers who specialize in proliferating advertisements for various medications are resorting to new formats for their information. In November, medications were advertised in a table indicating the different purposes of each medicine.
Spammers also took advantage of the highly publicized Pussy Riot case in Russia. An English-language email contained a link that allegedly led to news about the punk rock group. However, when users clicked on the link, they were directed to a website advertising Viagra.
Sources of spam by country and region
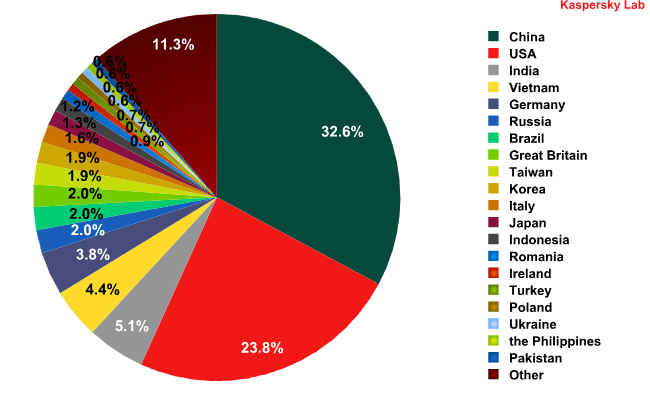
Among the sources of spam around the world, the leading countries are still China (32.7%) and the US (23.8%). The share of spam sent from China increased by 2 percentage points, while the percentage of spam originating in the US fell by 3.5 points. Overall, these two countries produced roughly 56% of global spam in the month of November.
Sources of spam around the world, by country
The top five sources of spam by country barely changed from October, with only Brazil falling from 5th place to 7th, allowing Germany to rise in the ratings (3.8%).
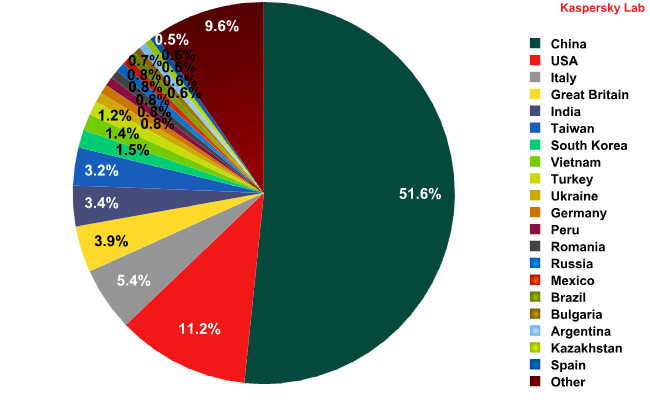
Sources of spam in Europe, by country
In November, the top three countries were the same as in October. Once again, China was in first place (51.63%, a drop of 1.67 percentage points compared to October). The numbers for the US and Italy also dropped 2.19 and 0.49 percentage points respectively. The UK took fourth place this month (up 0.71 percentage points), replacing India, which fell to 5th (+0.04 percentage points).
Asia remains among the top regional sources of spam (51.9%, or 1.4 percentage points higher than in October); North America and Western Europe are still among the top three regions.
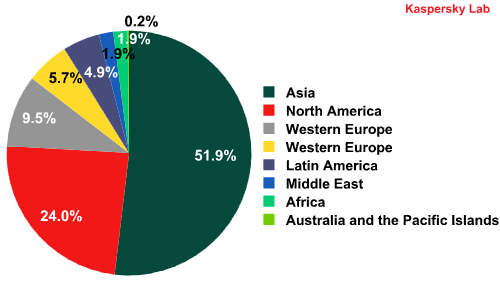
Sources of spam by region
Malicious attachments in email
In November, malicious attachments were detected in 3.27% of emails, up 0.02 percentage points from October.
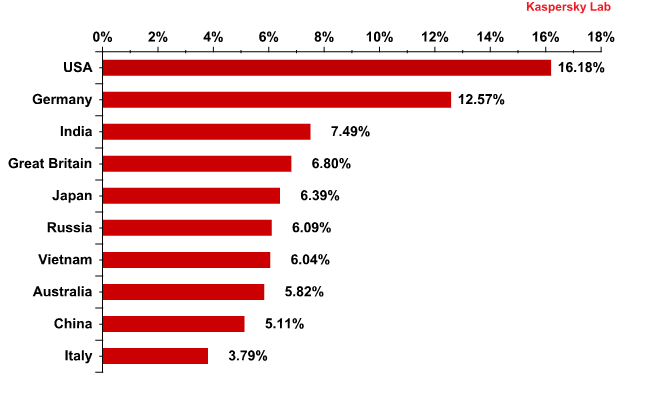
Distribution of email antivirus detections by country
The US (16.2%) and Germany (12.6%) remain among the countries that are targeted most by malicious emails. However, while Germany’s percentage did not change from October, America’s continued to rise (+3.6 percentage points), and in November the US became the number one country in terms of email antivirus detections. The percentages of the other countries in the Top 10 experienced little to no changes.
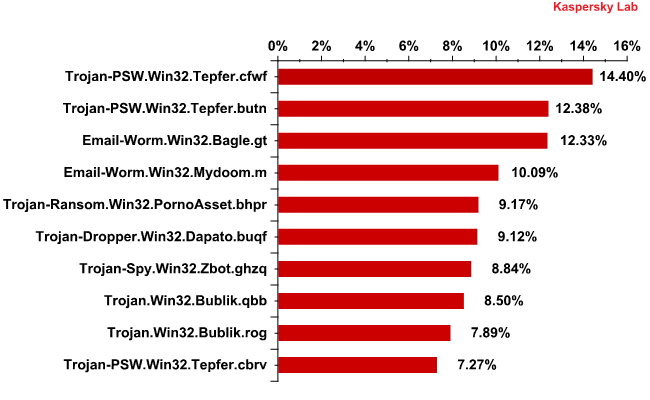
Top 10 malicious programs spread by email
The Top 10 malicious programs spread by email underwent some significant changes since October. Trojan-PSW.Win32.Tepfer.cfwf — a program that steals user passwords — took first place in November, and two other modifications within this family also made the Top 10.
Neither last month’s leader (Trojan-PSW.Win32.Tepfer.cfwf) nor the leader so far this year (Trojan-Spy.HTML.Fraud.gen) figured in this month’s Top 10. However, the Trojan-PSW family is also designed to steal user passwords — and not just for online banking accounts, but also for a broader range of online accounts. November’s Top 10 also featured Trojan-Spy.Win32.Zbot.ghzq, yet another modification of the Zbot/ZeuS Trojan.
Third and fourth place in November were taken by email worms, the main function of which is to self-proliferate to the addresses in the victim’s address book. Worms in the Bagle family can also download other malicious programs onto a user’s computer.
Phishing
In November, the percentage of phishing emails in total email traffic halved and settled at 0.015%.
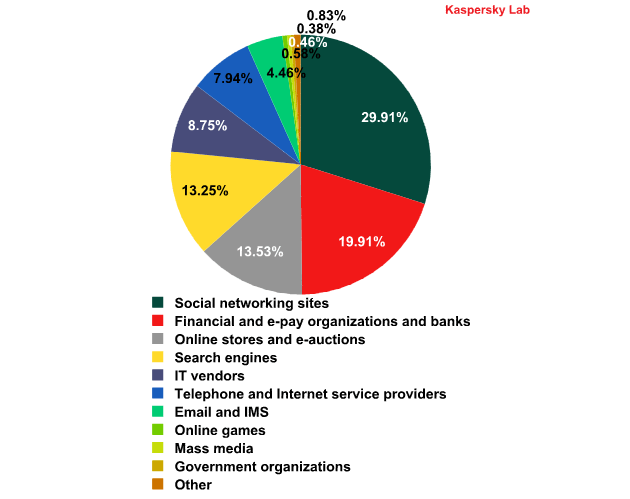
The distribution of the Top 100 organizations targeted by phishers, by category
*This rating is based on Kaspersky Lab’s anti-phishing component detections, which are activated every time a user attempts to click on a phishing link, regardless of whether the link is in a spam email or on a web page.
In November, Facebook was the number one target of phishers, with phishing attacks against the social networking site increasing 13.2 percentage points. While online stores were number one in October, they fell to third place (13.5%) this month. The share of phishing attacks targeting financial and e-payment organizations decreased by 3 percentage points in November, but this target remains firmly in second place.
Search engines are being targeted less frequently (-5.4 percentage points) and fell from being the number three target in October to number four in November. The search engines most frequently targeted by phishers are Google and Yahoo.
Conclusion
As expected, as we approach the winter holiday season, the amount of New Year- and Christmas-themed spam has surged. In December, advertisements for various goods and services related to the holidays will continue to increase. We may see more New Year and holiday subjects in a variety of mailings advertising goods and services that have nothing at all to do with the holidays, in addition to other mailings offering holiday discounts. The amount of image spam will also be on the rise.
During the holiday season, Internet users should be cautious about opening emails that allegedly contain notifications from various stores, banks, and other financial systems. Users are warned against opening suspicious attachments from unknown senders, clicking on links allegedly leading to banking websites, and especially against entering any personal information such as bank card numbers, passwords, or usernames for payment accounts.




















Spam in November 2012