
- December in figures
- Spam in the spotligh
- The return of ‘Chain letters’
- Sources of spam by country and region
- Malicious attachments in email
- Phishing
- Conclusion
December in figures
- The percentage of spam in email traffic was up 3.1 percentage points from November and averaged 66%.
- The percentage of phishing emails more than halved compared to November, falling to 0.006%.
- In December, malicious files were found in 3.15% of all emails, a decrease of 0.12 percentage points.
Spam in the spotlight
The end of the world
December 21, 2012 was a date greeted with a mixture of irony and fear – it had been billed as the final day of the Mayan calendar. A variety of apocalyptic scenarios were put forward – from a meteorite impact to the emergence of a new world or a transition to a new era.
In early December we saw several spam mailings exploiting this theme.
One of the emails included an invitation to a business development conference for company owners and top managers. Nostradamus was identified as the sender and the theme of the email was “The end of the world is postponed, it’s time to improve business”. The spammers assumed that the end of the world was a topic destined to provoke interest, but added info about the contents of the lecture to reassure readers that this conference was indeed a business opportunity and not an outbreak of hocus-pocus.
The author of yet another email stated that the end of the world was the transition from the 3rd to the 4th dimension, causing the human consciousness to extend and making people look at the world through eyes full of love. The link in the end of the email led to a site where users could download a prayer that would help them to pass into the 4th dimension.
It seems likely that the senders of this email were looking for active email addresses…in any dimension.
New Year knocking at the door with new spam offers
As expected, in December the number of New Year mass mailings grew. Noticeably, “New Year spam” varies in different countries. In countries where small and medium-sized businesses use spam to advertise (for example, in Russia), offers of seasonal goods and New Year presents are commonplace. These messages promoted e-gadgets, homebrew kits, cards and calendar printing services. Not surprisingly, Santa Claus, in all his localized guises, is also a popular figure in December.
At the same time English-language spam sent to users in the US and Europe was fairly standard (Viagra, replicas of designer goods, lottery fraud, etc.). However, spammers managed to work in a Christmas or New Year theme to attract more attention.
Fraud in spam
In December, the percentage of fraudulent emails in mail traffic increased. The spammers expected the users to be less cautious in the run-up to the holidays. In order to gain access to personal data and banking accounts, the fraudsters sent emails with malicious attachments and used new tricks.
Phishing. Made in China
Generally, phishing emails are written in English. But in December, we got a typical phishing email in Chinese. The message said that the limit of the recipient’s email box had been exceeded and the user could not receive or send emails until he confirmed his email address by clicking a link. It goes without saying that the link led to a fake site where a user was asked to enter his email address and password, thus providing the fraudsters with access to his email account.
Other scams
The Russian sector of the Internet – RuNet – saw many emails asking recipients to top up a mobile phone or to send a text message to a short number. The fraudsters’ goal was to extort money from users.
Fraudsters frequently threaten to block email, Internet access or the OS if users do not follow the instructions in an email. It’s an old trick, but unfortunately users still respond to these threats and end up transferring money to the scammers.
To get money, spammers are continuing to tug on users’ heartstrings. An interesting “Nigerian Letter” was recently distributed on behalf of a Russian woman. It claimed that “Elena”, a single mother, had lost her job and could no longer pay to heat her home deep in the Russian provinces. She asked for help to buy a new stove in a message calculated to arouse the reader’s sympathy and elicit offers of financial support. We’ve been seeing this kind of message for several years now.
The return of ‘Chain letters’
Chain letters made a reappearance in December. These “chain letters” are emails which include a request to the recipient to forward an email to friends, family and contacts. While many of these are just harmless fun, they can be used to extort money or personal information from users.
Chain letters often contain warnings of a threat, encouraging users to distribute the email. This means the message spreads rapidly, and confuses spam filtering by using legitimate addresses.
Chain letters containing information about new viruses and other IT threats are mainly spread to provoke panic among users and persuade them to download some kind of ‘silver bullet’ program which will protect them from the unfolding catastrophe. The user, however, usually ends up downloading malware which the fraudsters then use to steal data or distribute spam.
The email below notifies recipients that Microsoft and Norton have allegedly issued a warning about a message headed “Mail Server Report”, distributed in mail traffic, which in fact contains a malicious program. The “virus” supposedly deletes all the information on the computer of anyone who opens the email. The fraudsters even provide dramatic details – the last thing one sees on the monitor is the message “It is too late now; your life is no longer beautiful”. The virus was allegedly created by a hacker who calls himself “the life owner”. The email ends with a call to spread the warning.
Considering the growth in the amount of malicious mass mailings and the appearance of new methods and tricks used to spread malicious attachments, chain letters should be treated with great caution.
Sources of spam by country and region
China (34.3%) and the US (15.7%) are still the leading sources of spam worldwide. The amount of spam sent from China increased by 1.6 percentage points, while the percentage of spam originating in the US fell by 8.2 points. Overall, these two countries produced roughly 49.9% of global spam in December which is 6.5 points less than in the previous month.
Sources of spam around the world by country
In December Russia entered the top five sources of spam (3%). Germany (2.3%) fell from 5th place to 7th, having distributed 1.48 points less spam compared to November.In December, the top three countries sending spam to Europe were the same as in November. China (+6.5 percentage points) strengthened its leading position. The numbers for the US and Italy dropped 1.3 and 0.2 percentage points respectively, although these countries remained in 2nd and 3rd place. Korea came 4th with an increase of 3.4 percentage points.

Sources of spam in Europe, by countryAsia remained the top regional source of spam (55.6%, or 3.7 percentage points higher than in November).
Sources of spam by region
As in November, North America and Western Europe are still among the top three regions.
Malicious attachments in email
In December, malicious attachments were detected in 3.15% of emails, a drop of 0.12 percentage points from November.
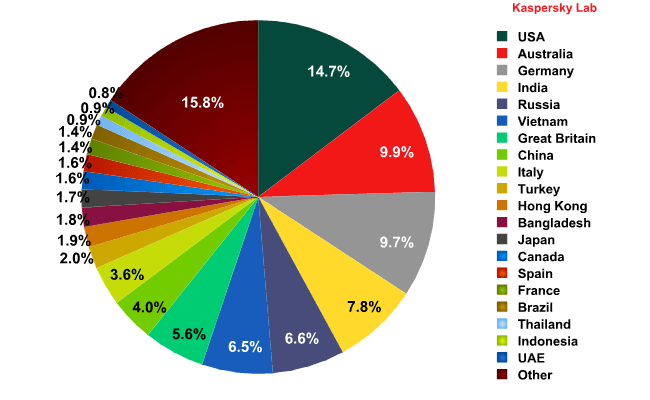
Distribution of email antivirus detections by country
The US (14.7%) topped the rating of countries that are most heavily targeted by malicious emails. Australia came second (9.9%) having doubled its score from November. It’s notable that the amount of malicious emails sent to Japan dropped by 4.7 percentage points, which moved this country down from 5th to 13th position.Top 10 malicious programs spread by email
In December, the mail worm Bagle topped the rating of the most widespread malicious programs carried by email. In addition to the main functionality of a mail worm, which is to self-proliferate to addresses in the victim’s address book, worms in the Bagle family can also download other malicious programs onto a user’s computer. Second place is occupied by another, simpler worm – Mydooom.
November’s leader Tepfer, a Trojan that steals user passwords, dropped two positions to 3rd place.
In December, Trojan-Spy.html.Fraud.gen, which was 2012’s “winner” in terms of the number of antivirus detections, re-entered the Top 5. In September, the amount of emails containing this malicious program decreased drastically and until December it was out of the Top 10. This Trojan program is also designed to steal passwords – and not just for online banking, but also for a broader range of online accounts.
Phishing
In December, the percentage of phishing emails in total email traffic halved and settled at 0.006%.
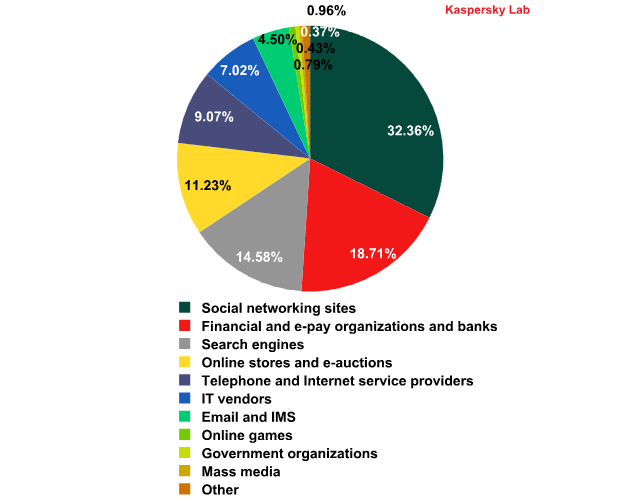
The distribution of the Top 100 organizations targeted by phishers, by category*
*This rating is based on Kaspersky Lab’s anti-phishing component detections, which are activated every time a user attempts to click on a phishing link, regardless of whether the link is in a spam email or on a web page.
In December, the number of phishing attacks against social networking sites increased by 2.45 percentage points, accounting for 32.36% and keeping this category on top of the charts. Facebook was still the number one target for phishers.
The share of phishing attacks targeting financial and e-payment organizations decreased by 1.2 percentage points in December, but this target remains in second place. Search engines regained 3rd place (+1.33 percentage points) in the rating.
Online stores came 4th (-2.3 percentage points) in December. The most popular ploy used by the phishers in this category was that of fake notifications from Amazon.
Conclusion
December is a time of pre-holiday excitement and festivities. As expected, the share of spam in mail traffic increased, and that included festive season spam. The bulk of festive mass mailings came in the form of image spam.
The fraudsters also tried to profit from the pre-holiday frenzy. They used both old favorites and new tricks to cheat their victims.
The share of phishing mailings decreased. However, December saw a number of fake notifications from Chinese email services which could be the start of a new trend. There was also a growing number of fake notifications from social networking sites.
In January, we expect a decline in spam levels, mainly due to the holiday lull of the first few days of the new year.





























Spam in December 2012