
Kaspersky Lab recently discovered a new ongoing spam campaign on Twitter. A Twitter account is actively sending tweets to random people with links to a video. Here’s one of the messages:
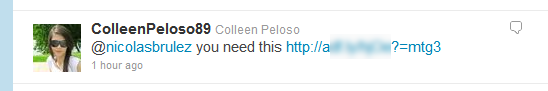
The spam campaign started roughly around 11:00 am GMT, mixing random tweets and direct links as you can see below:

The account spammed an average of 50 Tweets per hour, mixed with random sentences and tags to look less suspicious
Upon following such a link, users are directed to a website buffering a video that will never loads. The progress bar always stops at the same location:
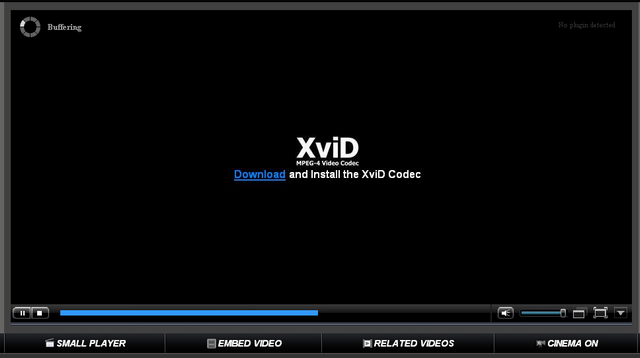
At the bottom of this you have a few options such as “Related Videos”. If you click any of those, you are prompted to download “Xvidsetup.exe”. As the capture below shows, it seems we are missing the XviD codecs.
During the installation of the XviD codecs, we get the following screen:
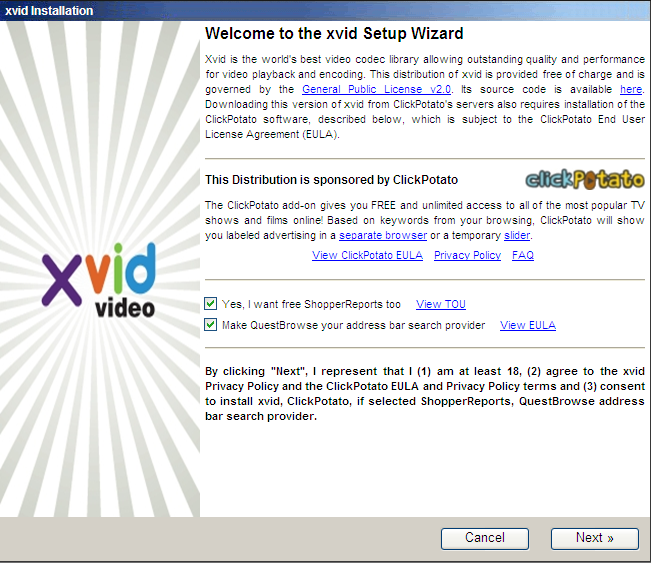
It’s a special bundle of XviD with ClickPotato embedded. If we just look at the strings inside of their clickpotato client, we find references to Zango, a known Adware maker:
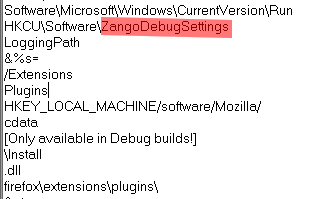
Kaspersky Lab customers are already protected from the installation of this Potentially Unwanted Software, as we detect this client as “not-a-virus:AdWare.Win32.HotBar.dh”
During installation, ClickPotato registers a Browser Helper Object in Internet Explorer. The Adware is then ready to display advertisements depending of your surfing habits. Adware authors are still aggressively marketing their creation, as we have seen with the spam campaign on Twitter.
Upon detection, Kaspersky Lab quickly contacted the Twitter security team regarding the spam campaign and they responded by disabling the account. They are actively working on deleting all fraudulent profiles.






















Spam Campaign on Twitter Leads to Adware