
On Wednesday 14th, TYPE O NEGATIVE frontman Peter Steele was rumored to have died of heart failure.
Fuse TV’s Mistress Juliya twitted that she spokes to a band member, adding credibility to the rumor.
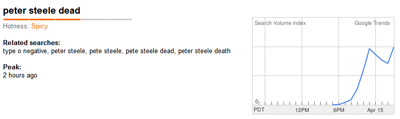
Google Trends shows that the first two “hot searches” are related to the rumor.
As you can see below there are a lot of active searches right now:
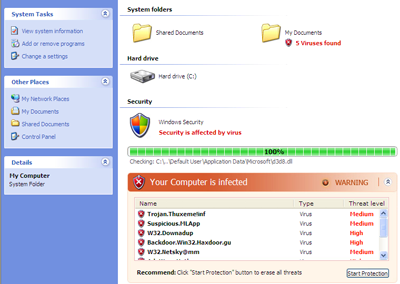
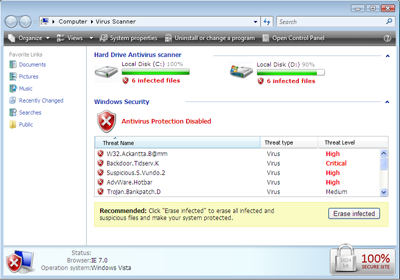
Black SEO is already being used and some of the results lead to web pages that look like this:
Depending on the links you follow, you may also end up here:
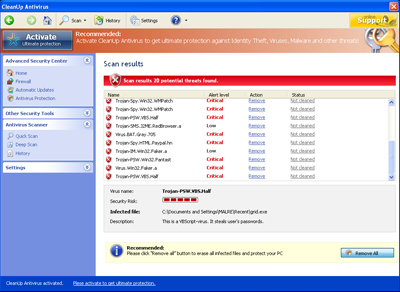
Both lead to the installation of the rogue CleanUp AntiVirus program (see the screenshot below):
Cybercriminals are using any sort of news, including rumors, to distribute their fake AV programs, and Black SEO is still being used extensively to spread them.
Unfortunately, later on the rumors of Steele’s death were confirmed. This will no doubt further increase the number of searches involving his name.






















Reports of TYPE O NEGATIVE frontman’s death unleash rogue AV