
Today we detected a new potentially unwanted program for smartphones running Symbian S60 2nd edition – not-a-virus:Porn-Dialer.SymbOS.Pornidal.a
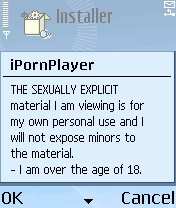
When a file called iPornPlayer.sis is launched, the user gets shown a standard EULA which mentions content of a pornographic nature, conditions of use etc. We detect this program as not-a-virus: Porn-Dialer and not as a Trojan-Dialer specifically because it’s got a EULA.
Most importantly, the EULA states that the app will call international premium rate numbers (listed below) in order to access content.
- +43820911995
- +43810522237
- +239980254
- +3598815400096
- +22650500089
- +6744449333
- +423662690232
- +227171020
- +41773111701
- +2284260203
The files below then get installed:
- с:systemappsSexyVideoSexyVideo.app
- с:systemappsSexyVideoSexyVideo.rsc
- c:systemprogramsFullLengthViewer.exe
- c:systemrecogsEZRECOG.MDL
The MDL file is used to autorun FullLengthViewer.exe and it’s this exe file that makes the calls to premium numbers.
This type of threat really highlights two points. One, most users read EULAs with one eye at best, which means they have no idea what the program might actually do (in this case, call premium numbers). Second, because it contains a EULA, what Pornidal does isn’t actually illegal. But this type of program can be modified by removing the EULA or changing it so it doesn’t mention premium rate calls – this would make the program malicious, and any profits it brings in would be clearly illegal.





















Porn dialers for smartphones