
After the publication of our whitepaper about the Gauss cyber-attack, we have been asked if there is an easy way for users to check their system for infection. Of course the most reliable way is to download and install our antivirus solution or use the free Kaspersky Virus Removal Tool.
If someone needs to double-check or for some reason cannot download full antivirus package, we offer a quick and easy way to check for the presence of Gauss component.
The idea of checking the system using a webpage comes from the wellknown Hungarian research lab, known as CrySyS. They have also introduced a web-based method to check your system for Palida Narrow. Their test webpage is currently available here: http://gauss.crysys.hu.
We used the same idea and tried to improve the detection method. Now it works without server interaction.
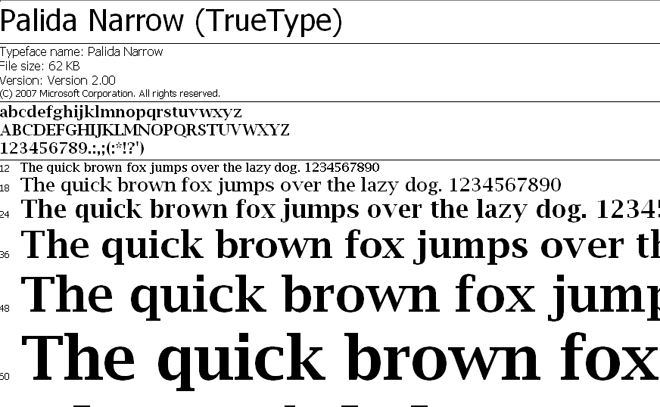
Below the current blogpost you will find an iframe window which has the results of a javascript code check to verify whether you have the mysterious Palida Narrow font installed. This font was used during the Gauss cyber-attack. Although we dont currently understand exactly why the attackers have installed this font, it could serve as an indicator of Gauss activity on your system. More details about the module which installs this font are available in our full article.
If you receive an alert warning you about the presence of Palida Narrow, we’d like you to e-mail us at theflame@kaspersky.com and we’ll try to assist you. Otherwise, you should install an antivirus solution and check your system immediately.
Result of Palida Narrow online detection:
PS: BTW, in case you are infected with Gauss, the free Kaspersky Virus Removal Tool can be used to clean it.






















Online detection of Gauss