
Offers to work as a mystery shopper are a common trick used by fraudsters. They give you a chance to work in your free time, and if you agree, they send you a fake check with a huge sum of money, which is supposed to compensate the costs of goods and research. Any remaining money left over after the work is returned to the fraudsters. When the bank annuls the check as a fake, the secret shopper is left out of pocket.
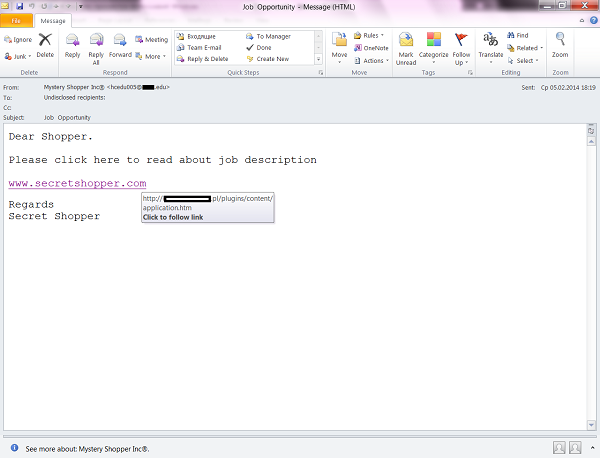
But as users become more aware of online dangers, scammers have had to resort to various types of tricks to achieve their goals, such as disguising scammer mailings as a mailing from a large company specializing in working with secret shoppers. The message, sent on behalf of Mystery Shopper Inc., prompted the user to look at a description of the vacancy, but the attached link led to another resource that also specializes in this type of market research.
The real address of the scammer’s page was revealed after clicking the attached link. Obviously, it had nothing to do with Mystery Shopper Inc. official resources.
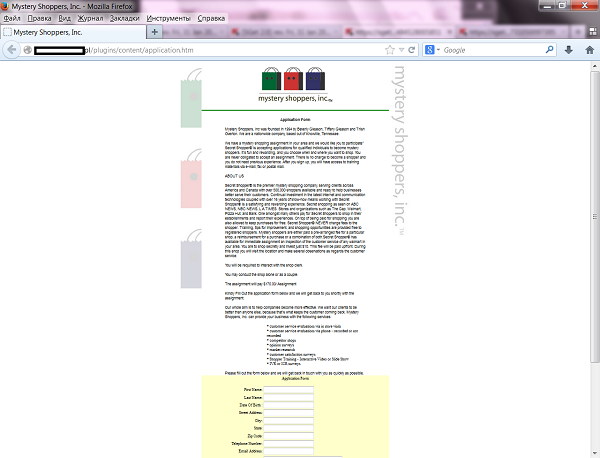
The fraudulent site described the benefits of working as a “mystery shopper”. To get the job the user was asked to fill in a form with personal data (full name, age, postal address and email).
I filled it in and in response received a message with a detailed guide about the research activity as a “mystery shopper”. The message ended with a promise that a check for all the costs would be sent to the stated address. The biggest giveaway that this was a fraud was the free mailbox stated in the contact information, and not the email of the company who had supposedly sent the message.
Avoid this sort of scam by following some simple rules: ignore letters from resources you’re not registered to, and carefully study the addresses in the attached links. If you do that there will be little temptation to pay lots of money for a fake check.
Mystery Shopper: Beware of Frauds






















kiraKiran
Why do they always say that you can collect so much of money who passed away and you can collect it by giving your bank details.
Although i sent them money so that they can alteast do some needful work.
After that they say that the big money will be sent to your Bank Account and you have to fill up your Ministry Form details.
I sincerely wouldn’t know if the Bank got so much personal details from my side from the person who has done all these foolish things.
I thought that i have done something really wrong in life itself for lending my money.
We never want so much of money from anybody’s side.
we can just ask money for Hospital work, insurance bills, work and for livelyhood work.
I look forward to your assistance
sincerely