
So far in our series about Stuxnet we’ve focussed on the main issue: the threat posed by the zero-day vulnerability in the processing of LNK files, and the fact that cybercriminals have somehow got their hands on digital certificates. What we haven’t done in any detail is look at the worm’s functionality.
Anyone following the story has probably already read about how the worm, in addition to replicating, attempts to gain access to industrial systems running WinCC from Siemens.
I can’t remember which journalist or antivirus researcher first mentioned power plants (some of which certainly do run WinCC) in connection with Stuxnet. Since then, the whole story’s taken on the air of a Hollywood movie, with dark and repeated murmurings of ‘attacks on industry’ and ‘inter-government espionage’.
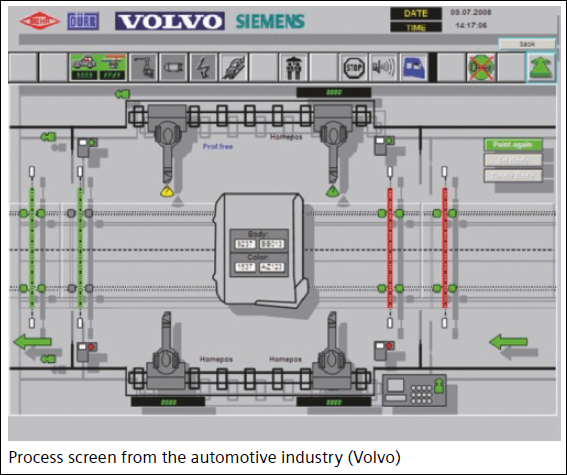
Stuxnet does attempt to connect to the WinCC SCADA visualization system using the default password from Siemens. Part of the worm is a very interesting component, a dll, which acts as a wrapper for the original Siemens dll. It’s this wrapper that tries to connect to WinCC, redirecting the majority of the functions to the original dll, while emulating the remaining functions itself.
The functions are:
s7db_open
s7blk_write
s7blk_findfirst
s7blk_findnext
s7blk_read
s7_event
s7ag_test
s7ag_read_szl
s7blk_delete
s7ag_link_in
s7db_close
s7ag_bub_cycl_read_create
s7ag_bub_read_var
s7ag_bub_write_var
s7ag_bub_read_var_seg
s7ag_bub_write_var_seg
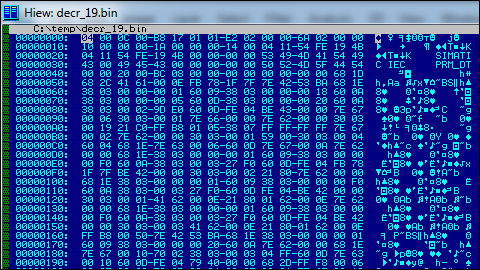
The module also contains several encrypted blocks of data – here’s an example of a decrypted block:
Siemens is currently conducting its own investigations and analysis of the malware. They’ve published official information about the incident, which reports one confirmed case of infection of a WinCC client in Germany.
From the report:
“Currently there is still only one known case where a customer’s WinCC computer has been infected. The virus infiltrated a purely engineering environment of a system integrator, but was quickly eliminated. A production plant has not been affected so far.”
“There is only one known case of infection in Germany. We are, at present, trying to find out whether the virus caused any damage.”
Siemens also confirms that the worm is able to transmit process and production data, and that it attempts to establish a connection with the cybercriminals’ servers. At the moment, however, the servers are apparently inactive.
P.S. Siemens has just issued an update:
“Currently we know of two cases worldwide where a WinCC computer has been infected. A production plant has so far not been affected.”





















Myrtus and Guava, Episode 5