
Post was updated 19.03.2011 (see below)
In the last few days a malicious program has been discovered with a valid signature. The malware is a 32- or 64-bit dropper that is detected by Kaspersky Lab as Trojan-Dropper.Win32.Mediyes or Trojan-Dropper.Win64.Mediyes respectively.
Numerous dropper files have been identified that were signed on various dates between December 2011 and 7 March 2012. In all those cases a certificate was used that was issued for the Swiss company Conpavi AG. The company is known to work with Swiss government agencies such as municipalities and cantons.
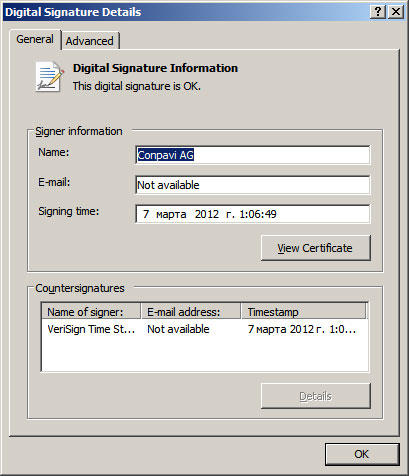
Information about the Trojan-Dropper.Win32.Mediyes digital signature
We don’t yet know the exact source of Trojan-Dropper.Win32/Win64.Mediyes, but there’s reason to believe that it is installed on computers with the help of exploits.
The 32-bit dropper stores its own 32-bit driver – whose name begins with ‘HID’ – to the system drivers directory. The dropper then deletes itself from the system. The driver itself is not signed, though this doesn’t prevent it from functioning properly on a 32-bit Windows operating system. The driver contains a DLL which is copied to a system folder beginning with the letters ‘PNG’. The main function of the driver is to inject a DLL into an Internet browser process. The driver also conceals the Mediyes components on the disk.
The 64-bit dropper does not contain a driver and injects a DLL directly into the browser.
The malicious DLL is detected by Kaspersky Lab as Trojan.Win32.Mediyes, and the driver is detected as Rootkit.Win32.Mediyes.
After the DLL is launched, it checks which browser it is running in and then starts intercepting browser requests sent to the Google, Yahoo! and Bing search engines. It duplicates all requests on the server of the malicious users which is located in Germany. The search queries are used by the criminals to earn money as part of the Search 123 partner program that works on a pay-per-click (PPC) basis. The server responds to the users’ requests with links from the Search123 system that are clicked without the user knowing about it. This results in the bad guys making money from fake clicks.
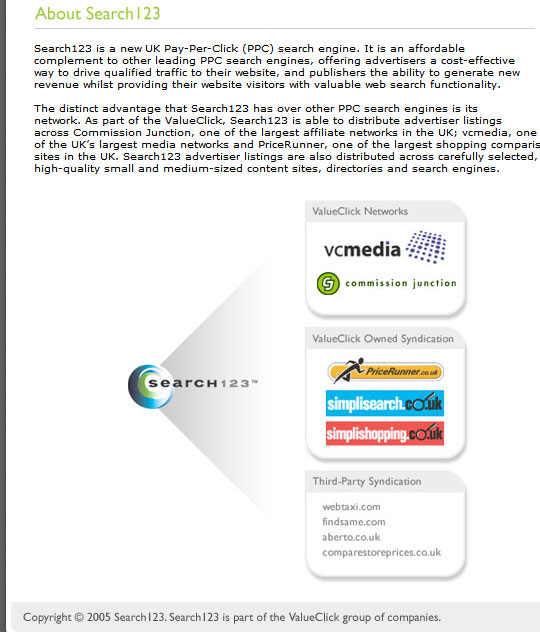
Description of the Search123 partner program
According to KSN data, the malicious DLL Trojan.Win32.Mediyes was detected on the computers of approximately 5,000 unique users, primarily in Western Europe – Germany, Switzerland, Sweden, France and Italy.
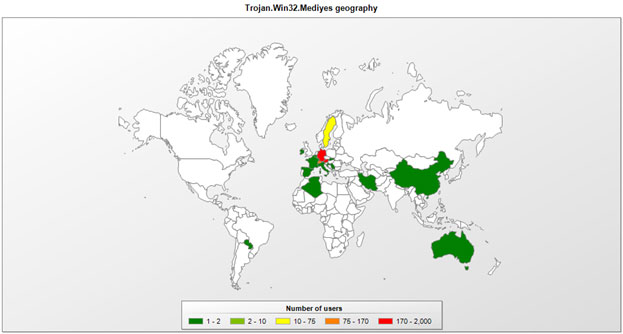
Geographical distribution of Trojan.Win32.Mediyes
The malware is clearly aimed at users in Western Europe. This is backed up by other evidence – the certificate from a Swiss company, the server in Germany, and only the requests made on major international search engines being intercepted.
We have informed VeriSign about the threat and have asked them to revoke the compromised certificates.
UPD: Symantec revoked compromised certificates.






















Mediyes – the dropper with a valid signature