
This morning we saw a massive malware run in the Netherlands. The emails were purportedly sent by the Dutch ABN-AMRO bank.
Of course, as I’ve said before, phishing attacks on users of Dutch banks are relatively rare. Prior to this mailing, we’ve only seen basic phishing runs which try and persuade the user to clink on a link. But this morning gave us a first – an email in Dutch, claiming to be from a Dutch bank, and containing malware – Trojan-Spy.Win32.Banker.cmb, an online banking Trojan. Interestingly, although the Dutch isn’t perfect, it doesn’t contain the multiple errors which often characterize malicious mass mailings.
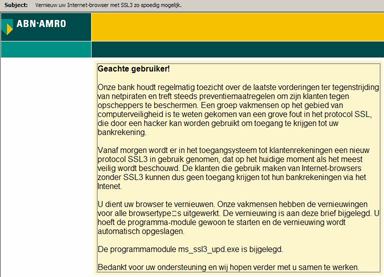
The email claims that a serious error in SSL has been found, that the bank will upgrade to SSL3 tomorrow and that users will need to install the attached patch if they still want to use the Bank’s online services.
Although there’s no hard evidence to support it, there is speculation that this bank was targeted because of a possible upcoming takeover/merger. This seems plausible – it certainly wouldn’t be the first time that cyber criminals exploited events publicized in the media for their own ends.
Overall, ABN-AMRO isn’t having a great time. There was a phishing run targeting the bank’s clients yesterday. The bank issued a statement saying it was believed the instigators had done this for attention, as no losses could be established.
However, this doesn’t seem quite right to me. Criminals who are financially motivated don’t want attention – it ruins their agenda, which is to make money from unsuspecting users. Yesterday’s phishing run will probably have dented any chance that today’s malware run had of succeeding.





















Massive malware run against ABN-AMRO customers