
Like many others, I took advantage of Amazon.com’s sale and ordered a Kindle Fire HD last week. When I got around to exploring the Amazon App Store, it didn’t take long before running into malware.
While searching for a particular benchmarking app I was presented with some additional apps.
One of them immediately looked suspicious.

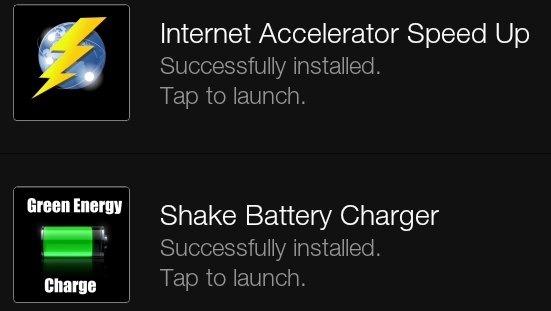
This app comes with the AirPush ad framework. That would potentially make this app AdWare. However, upon closer examination, it became clear the actual app doesn’t do much of anything. It was very obviously put together quickly to make a buck.
This ‘Internet Accelerator Speed Up’ does nothing to optimize your connection. This is basically the core functionality of the app:
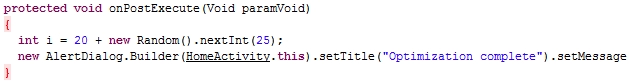
When run, before showing some other messages, it will tell you that your connection has been optimized by 20-45%. That’s it.
It’s not the only app uploaded by this developer. Shake Battery Charger is another one.
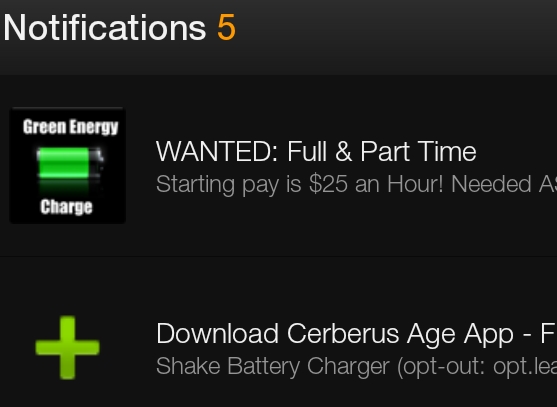
Examples ads shown by these apps on a Kindle Fire:
These apps were both signed by a Valkov Venelin. When we search online that leads us to this Twitter account:

References to “Bapplz” match with what we found in the code. That leads us to bapplz.com:
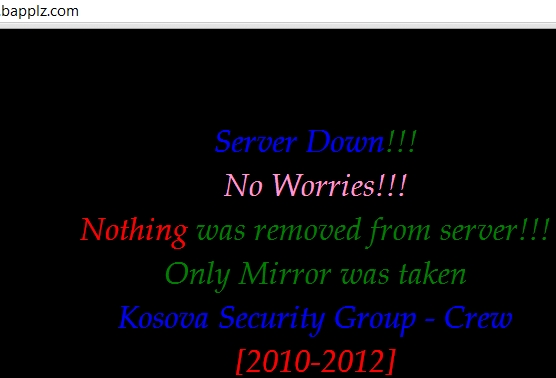
It’s been like that since August of this year. Clearly, the project seems abandoned even if it’s still making the author some money.
It should come as no surprise that there are malicious apps in the Amazon App Store. Amazon.com is incredibly popular and it’s a very trivial step to also upload an app into their store.
We detect these pieces of malware as HEUR:Hoax.AndroidOS.FakeBapp.a and have been in contact with Amazon.com about this. The apps were previously available in Google Play as well, but had been removed at an earlier time.
MD5s of the APKs:
1426a24894e186bc48a6359a4a791da5
69febc239486148bf9192a778cc9dbda





















Malware in the Amazon App Store