
The situation with phishing runs targeted at Dutch banks has remained the same throughout 2006 – very quiet. I started noticing that the criminals were strategically planning their attacks by mostly using holidays to carry out their spam runs. By doing this they were hoping to increase the response time of the people involved in combatting these threats.
Just as I had expected there was a phishing run against the Dutch Postbank on Monday, the first day of Christmas. Although it was Christmas the overall response time from the parties involved didn’t really suffer. So that’s good.
We detected the phishing sample proactively as Trojan-Spy.HTML.Fraud.gen.
Today we noticed an interesting side effect of this phishing run.
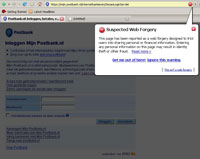
The link in the adress bar is the one spoofed in the phishing email. Firefox makes use of Google’s anti-phishing database. Seeing as the fraudulent site is also detected Google accidentily added both sites to the database.
We’ve reported this to Google. Let’s hope this gets fixed soon as quite a lot of Dutch people are worried about this.
Btw, there seems to be some bug in Firefox. For currently unknown reasons Firefox 2.0.0.1 only flags the site after switching tabs.





















Like clockwork