
In the last few days, our anti-ransomware module has been detecting a new variant of malware – KeyPass ransomware. Others in the security community have also noticed that this ransomware began to actively spread in August:
Distribution model
According to our information, the malware is propagated by means of fake installers that download the ransomware module.
Description
The Trojan sample is written in C++ and compiled in MS Visual Studio. It was developed using the libraries MFC, Boost and Crypto++. The PE header contains a recent compilation date.
When started on the victim’s computer, the Trojan copies its executable to %LocalAppData% and launches it. It then deletes itself from the original location.
Following that, it spawns several copies of its own process, passing the encryption key and victim ID as command line arguments.
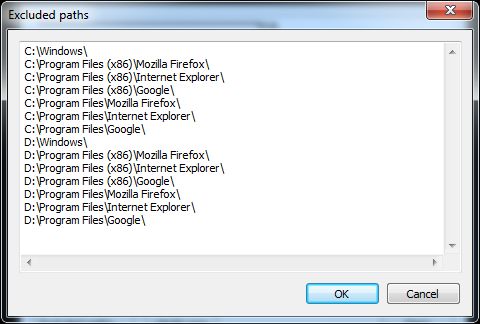
KeyPass enumerates local drives and network shares accessible from the infected machine and searches for all files, regardless of their extension. It skips files located in a number of directories, the paths to which are hardcoded into the sample.
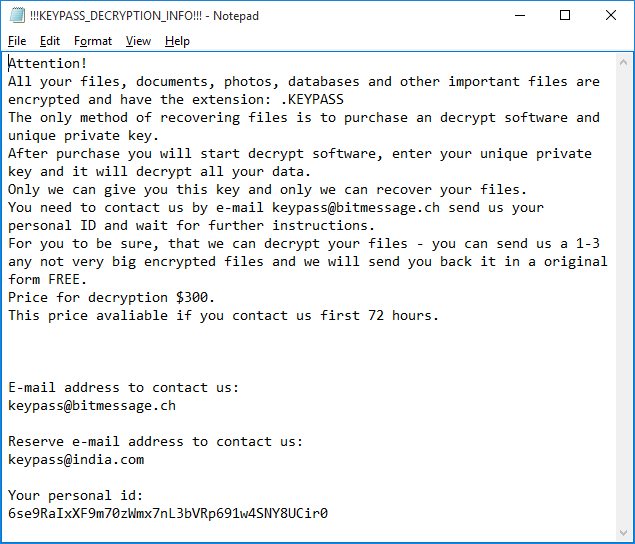
Every encrypted file gets an additional extension: “.KEYPASS” and ransom notes named “”!!!KEYPASS_DECRYPTION_INFO!!!.txt”” are saved in each processed directory.
Encryption scheme
The developers of this Trojan implemented a very simplistic scheme. The malware uses the symmetric algorithm AES-256 in CFB mode with zero IV and the same 32-byte key for all files. The Trojan encrypts a maximum of 0x500000 bytes (~5 MB) of data at the beginning of each file.
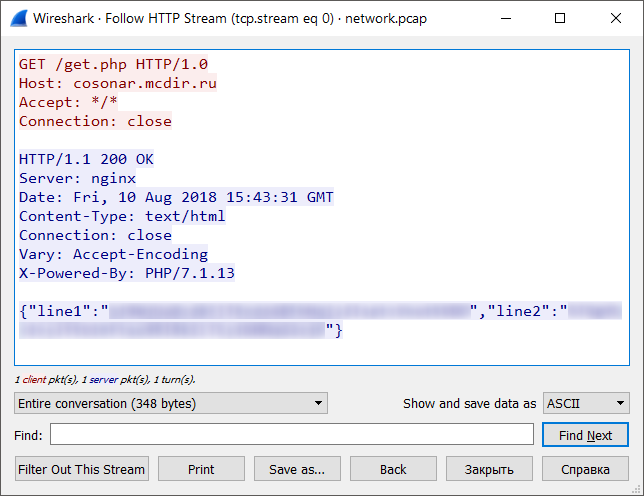
Soon after launch, KeyPass connects to its command and control (C&C) server and receives the encryption key and the infection ID for the current victim. The data is transferred over plain HTTP in the form of JSON.
If the C&C is inaccessible (e.g. if the infected machine is not connected to the internet or the server is down), the Trojan uses a hardcoded key and ID, which means that in the case of offline encryption the decryption of the victim’s files will be trivial.
GUI
From our point of view, the most interesting feature of the KeyPass Trojan is the ability to take ‘manual control’. The Trojan contains a form that is hidden by default, but which can be shown after pressing a special button on the keyboard. This capability might be an indication that the criminals behind the Trojan intend to use it in manual attacks.
This form allows the attacker to customize the encryption process by changing such parameters as:
- encryption key
- name of ransom note
- text of ransom note
- victim ID
- extension of the encrypted files
- list of paths to be excluded from the encryption
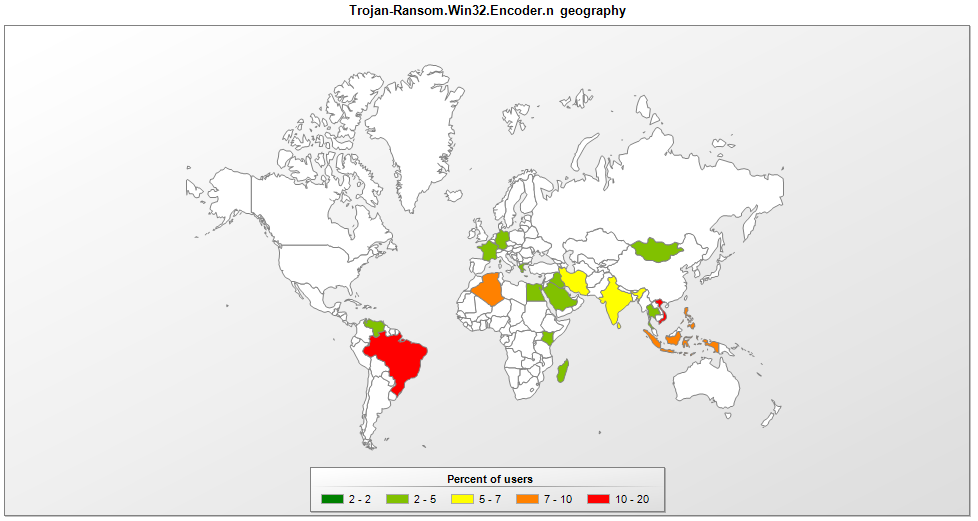
Geography
IOC
901d893f665c6f9741aa940e5f275952 – Trojan-Ransom.Win32.Encoder.n
hxxp://cosonar.mcdir.ru/get.php




























KeyPass ransomware