
Today we detected a new variant of IM-Worm.Win32.Kelvir – we detect it as Kelvir.k. As always Kelvir is accompanied with an IRCBot, which we detect as Backdoor.Win32.Rbot.gen.
This new Kelvir variant uses a new social engineering tactic to spread. Instead of hyperlinking to, for instance, a .pif or .scr file, Kelvir.k links to a .php file. The thing about links to .php files is that you can append extra data (letters and numbers) to them. This additional data will be sent to the server when the link is clicked. And that’s exactly what Kelvir.k does – it appends the IM user’s MSN address to the link.
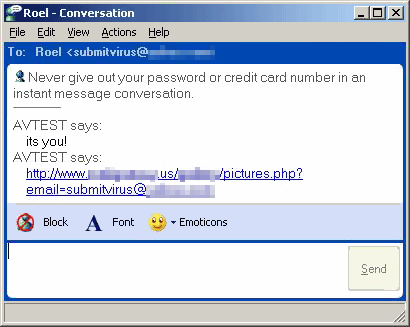
To make things a bit clearer, here’s an example.
IM user #1 has the email address some@thing.qqq
IM user #2 has the email address: other@thing.zzz
User #1 gets a link which looks like this: hxxp://www.[edited].us/[edited]/pictures.php?email=some@thing.qqq
User #2 gets a link which looks like this: hxxp://www.[edited].us/[edited]/pictures.php?email=other@thing.zzz.
When the link is clicked, the user is presented with a prompt to execute or save an MS-DOS application. By now, users will hopefully be suspicious and not run the application.
But as soon as the user clicks the link, their email address is harvested. So even if the user doesn’t run the MS-DOS application, the brains behind Kelvir get another address to spam.
So is this new tactic being used because of MSNM 7’s new ‘anti-malware’ features? I don’t think so. While I was writing this, we detected a repacked version of Kelvir.e. And Kelvir.e uses a hyperlink to a .scr file to spread, something which isn’t filtered by MSNM 7.
The use of new social engineering tactics leads me to believe that IM-users have learned to be more careful – ‘traditional’ IM-Worms don’t seem to be as effective as they used to be, and attackers are looking for new ways to install their malware on a large number of machines.





















Kelvir changes its approach