
These statistics are based on detection verdicts of Kaspersky products received from users who consented to provide statistical data.
Quarterly figures
According to Kaspersky Security Network, in Q1 2021:
- Kaspersky solutions blocked 2,023,556,082 attacks launched from online resources across the globe.
- 613,968,631 unique URLs were recognized as malicious by Web Anti-Virus components.
- Attempts to run malware designed to steal money via online access to bank accounts were stopped on the computers of 118,099 users.
- Ransomware attacks were defeated on the computers of 91,841 unique users.
- Our File Anti-Virus detected 77,415,192 unique malicious and potentially unwanted objects.
Financial threats
Financial threat statistics
At the end of last year, the number of users attacked by malware designed to steal money from bank accounts gradually decreased, a trend that continued in Q1 2021. This quarter, in total, Kaspersky solutions blocked the malware of such type on the computers of 118,099 unique users.
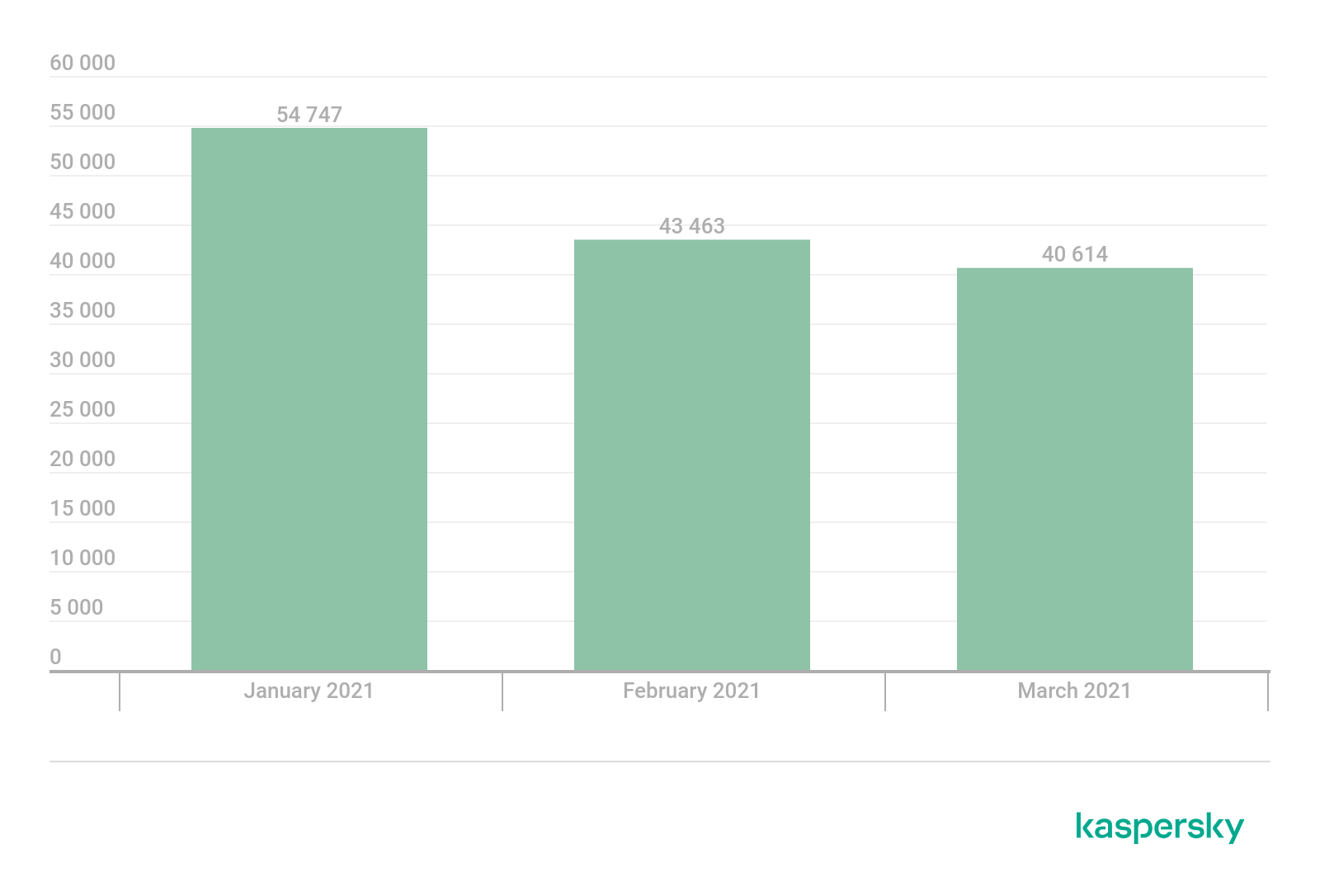
Number of unique users attacked by financial malware, Q1 2021 (download)
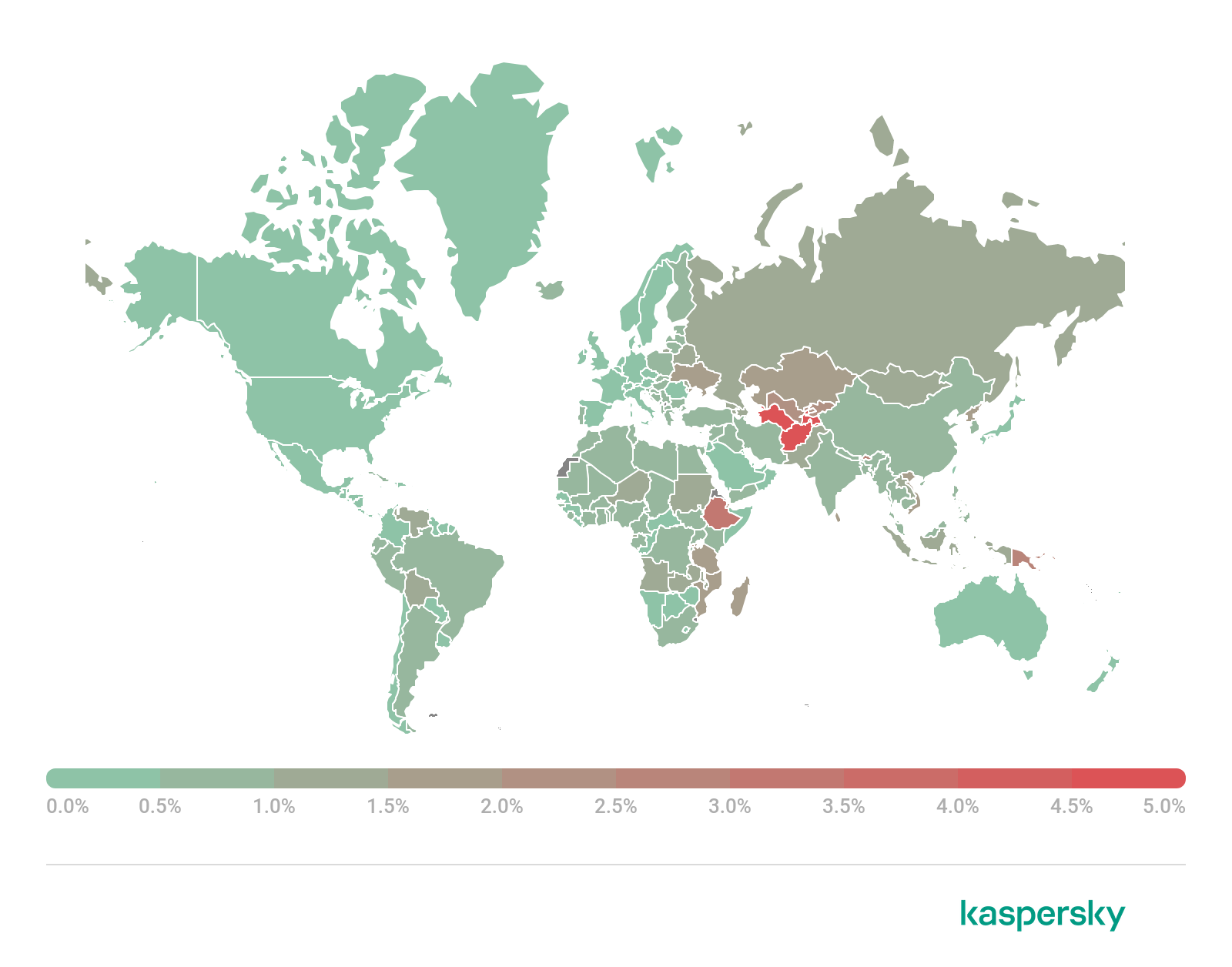
Attack geography
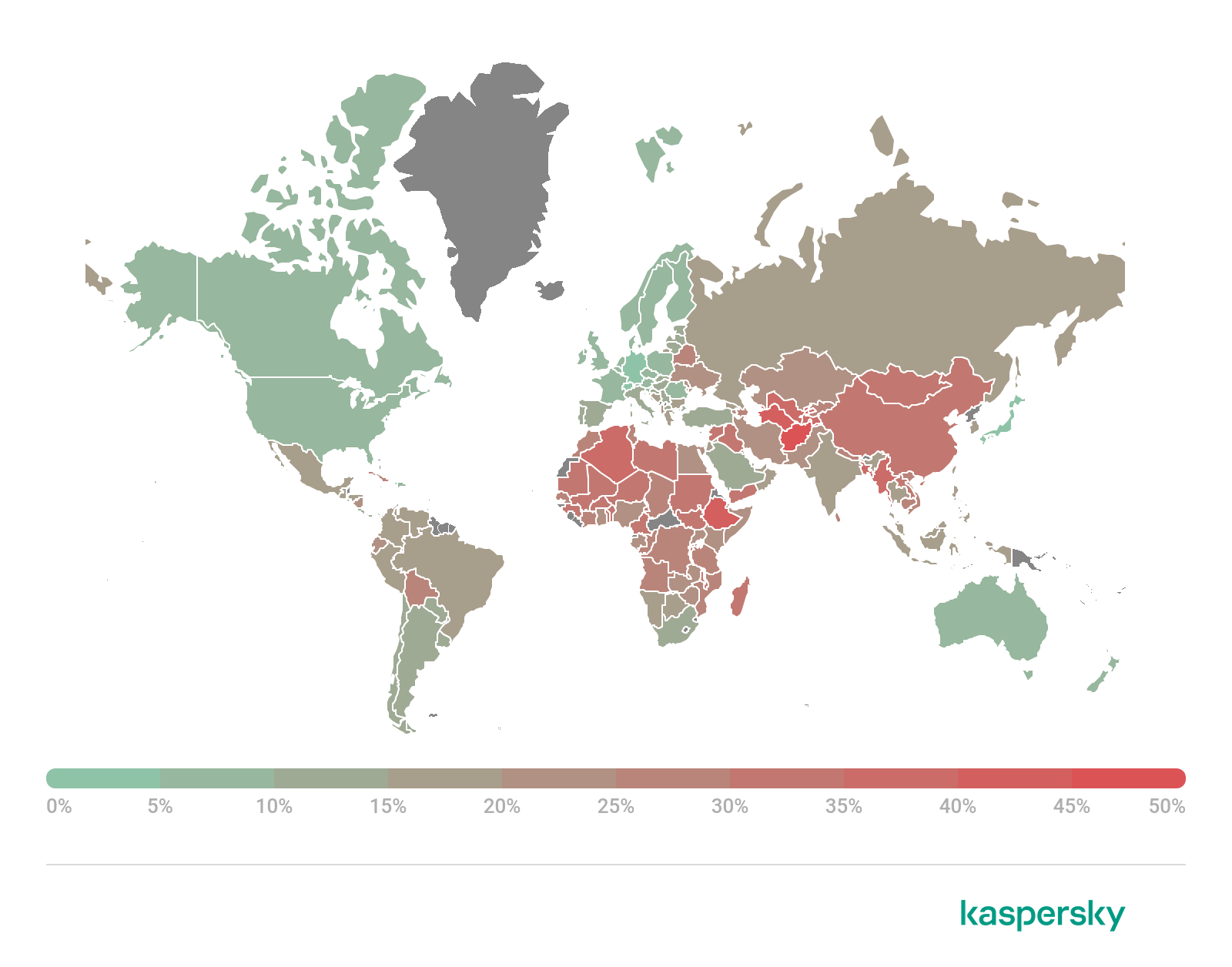
To evaluate and compare the risk of being infected by banking Trojans and ATM/POS malware worldwide, for each country we calculated the share of users of Kaspersky products who faced this threat during the reporting period as a percentage of all users of our products in that country.

Geography of financial malware attacks, Q1 2021 (download)
Top 10 countries by share of attacked users
| Country* | %** | |
| 1 | Turkmenistan | 6.3 |
| 2 | Tajikistan | 5.3 |
| 3 | Afghanistan | 4.8 |
| 4 | Uzbekistan | 4.6 |
| 5 | Paraguay | 3.2 |
| 6 | Yemen | 2.1 |
| 7 | Costa Rica | 2.0 |
| 8 | Sudan | 2.0 |
| 9 | Syria | 1.5 |
| 10 | Venezuela | 1.4 |
* Excluded are countries with relatively few Kaspersky product users (under 10,000).
** Unique users whose computers were targeted by financial malware as a percentage of all unique users of Kaspersky products in the country.
As before, the most widespread family of bankers in Q1 was ZeuS/Zbot (30.8%). Second place was taken by the CliptoShuffler family (15.9%), and third by Trickster (7.5%). All in all, more than half of all attacked users encountered these families. The notorious banking Trojan Emotet (7.4%) was deprived of its infrastructure this quarter as a result of a joint operation by Europol, the FBI and other law enforcement agencies, and its share predictably collapsed.
Top 10 banking malware families
| Name | Verdicts | %* | |
| 1 | Zbot | Trojan.Win32.Zbot | 30.8 |
| 2 | CliptoShuffler | Trojan-Banker.Win32.CliptoShuffler | 15.9 |
| 3 | Trickster | Trojan.Win32.Trickster | 7.5 |
| 4 | Emotet | Backdoor.Win32.Emotet | 7.4 |
| 5 | RTM | Trojan-Banker.Win32.RTM | 6.6 |
| 6 | Nimnul | Virus.Win32.Nimnul | 5.1 |
| 7 | Nymaim | Trojan.Win32.Nymaim | 4.7 |
| 8 | SpyEye | Trojan-Spy.Win32.SpyEye | 3.8 |
| 9 | Danabot | Trojan-Banker.Win32.Danabot | 2.9 |
| 10 | Neurevt | Trojan.Win32.Neurevt | 2.2 |
** Unique users who encountered this malware family as a percentage of all users attacked by financial malware.
Ransomware programs
Quarterly trends and highlights
New additions to the ransomware arsenal
Last year, the SunCrypt and RagnarLocker ransomware groups adopted new scare tactics. If the victim organization is slow to pay up, even though its files are encrypted and some of its confidential data has been stolen, the attackers additionally threaten to carry out a DDoS attack. In Q1 2021, these two groups were joined by a third, Avaddon. Besides publishing stolen data, the ransomware operators said on their website that the victim would be subjected to a DDoS attack until it reached out to them.
REvil (aka Sodinokibi) is another group looking to increase its extortion leverage. In addition to DDoS attacks, it has added spam and calls to clients and partners of the victim company to its toolbox.
Attacks on vulnerable Exchange servers
Serious vulnerabilities were recently discovered in the Microsoft Exchange mail server, allowing remote code execution. Ransomware distributors wasted no time in exploiting these vulnerabilities; to date, this infection vector was seen being used by the Black Kingdom and DearCry families.
Publication of keys
The developers of the Fonix (aka XINOF) ransomware ceased distributing their Trojan and posted the master key online for decrypting affected files. We took this key and created a decryptor that anyone can use. The developers of another strain of ransomware, Ziggy, not only published the keys for all victims, but also announced their intention to return the money to everyone who paid up.
Law enforcement successes
Law enforcement agencies under the US Department of Justice seized dark web resources used by NetWalker (aka Mailto) ransomware affiliates, and also brought charges against one of the alleged actors.
French and Ukrainian law enforcers worked together to trace payments made through the Bitcoin ecosystem to Egregor ransomware distributors. The joint investigation resulted in the arrest of several alleged members of the Egregor gang.
In South Korea, a suspect in the GandCrab ransomware operation was arrested (this family ceased active distribution back in 2019).
Number of new modifications
In Q1 2021, we detected seven new ransomware families and 4,354 new modifications of this malware type.

Number of new ransomware modifications, Q1 2020 – Q1 2021 (download)
Number of users attacked by ransomware Trojans
In Q1 2021, Kaspersky products and technologies protected 91,841 users from ransomware attacks.

Number of unique users attacked by ransomware Trojans, Q1 2021 (download)
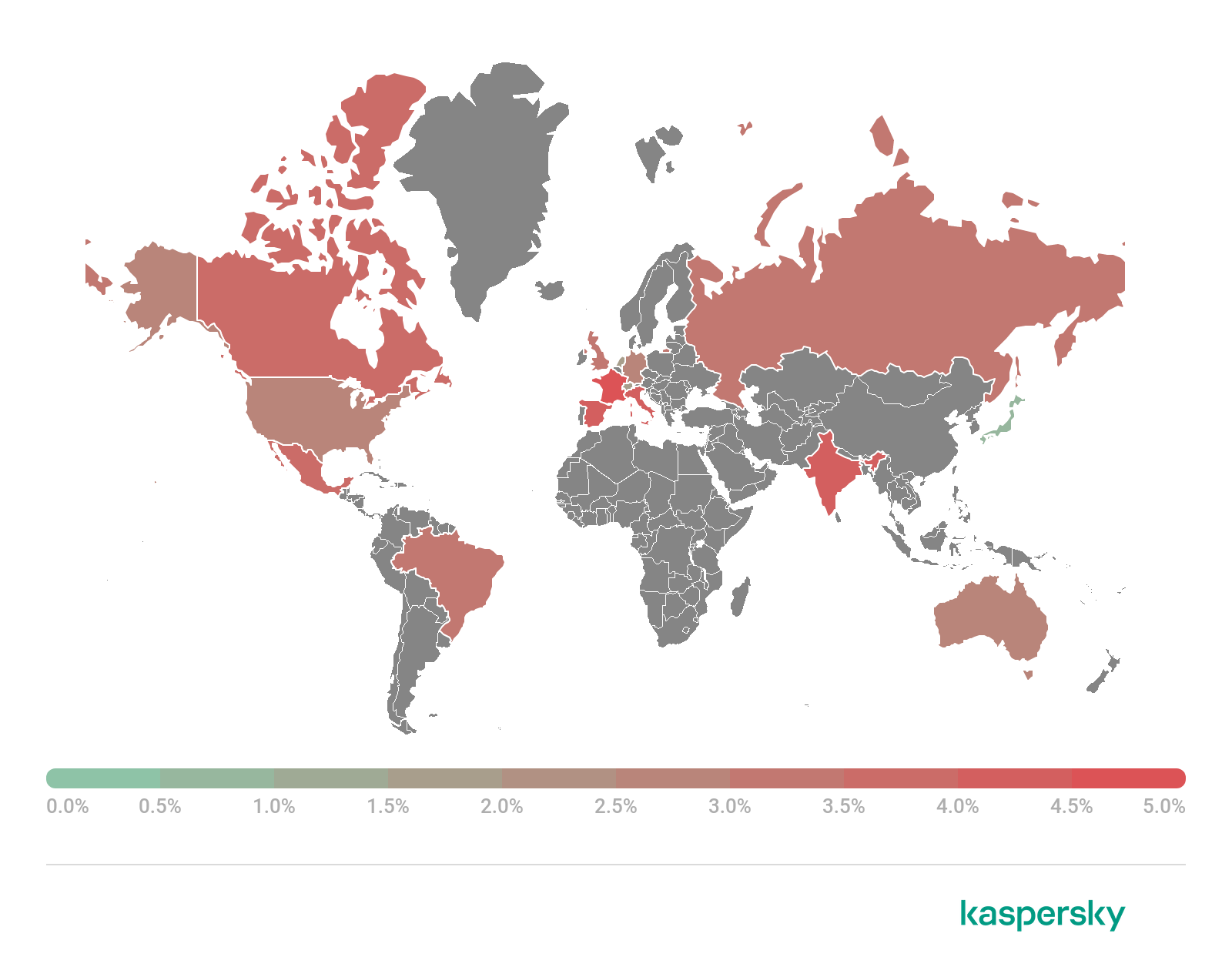
Attack geography

Geography of attacks by ransomware Trojans, Q1 2021 (download)
Top 10 countries attacked by ransomware Trojans
| Country* | %** | |
| 1 | Bangladesh | 2.31% |
| 2 | Ethiopia | 0.62% |
| 3 | Greece | 0.49% |
| 4 | Pakistan | 0.49% |
| 5 | China | 0.48% |
| 6 | Tunisia | 0.44% |
| 7 | Afghanistan | 0.42% |
| 8 | Indonesia | 0.38% |
| 9 | Taiwan, Province of China | 0.37% |
| 10 | Egypt | 0.28% |
* Excluded are countries with relatively few Kaspersky users (under 50,000).
** Unique users attacked by ransomware Trojans as a percentage of all unique users of Kaspersky products in the country.
Top 10 most common families of ransomware Trojans
| Name | Verdicts | %* | |
| 1 | WannaCry | Trojan-Ransom.Win32.Wanna | 19.37% |
| 2 | (generic verdict) | Trojan-Ransom.Win32.Gen | 12.01% |
| 3 | (generic verdict) | Trojan-Ransom.Win32.Phny | 9.31% |
| 4 | (generic verdict) | Trojan-Ransom.Win32.Encoder | 8.45% |
| 5 | (generic verdict) | Trojan-Ransom.Win32.Agent | 7.36% |
| 6 | PolyRansom/VirLock | Trojan-Ransom.Win32.PolyRansom
Virus.Win32.PolyRansom |
3.78% |
| 7 | (generic verdict) | Trojan-Ransom.Win32.Crypren | 2.93% |
| 8 | Stop | Trojan-Ransom.Win32.Stop | 2.79% |
| 9 | (generic verdict) | Trojan-Ransom.Win32.Cryptor | 2.17% |
| 10 | REvil/Sodinokibi | Trojan-Ransom.Win32.Sodin | 1.85% |
* Unique Kaspersky users attacked by this family of ransomware Trojans as a percentage of all users attacked by such malware.
Miners
Number of new modifications
In Q1 2021, Kaspersky solutions detected 23,894 new modifications of miners. And though January and February passed off relatively calmly, March saw a sharp rise in the number of new modifications — more than fourfold compared to February.

Number of new miner modifications, Q1 2021 (download)
Number of users attacked by miners
In Q1, we detected attacks using miners on the computers of 432,171 unique users of Kaspersky products worldwide. Although this figure has been rising for three months, it is premature to talk about a reversal of last year’s trend, whereby the number of users attacked by miners actually fell. For now, we can tentatively assume that the growth in cryptocurrency prices, in particular bitcoin, has attracted the attention of cybercriminals and returned miners to their toolkit.

Number of unique users attacked by miners, Q1 2021 (download)
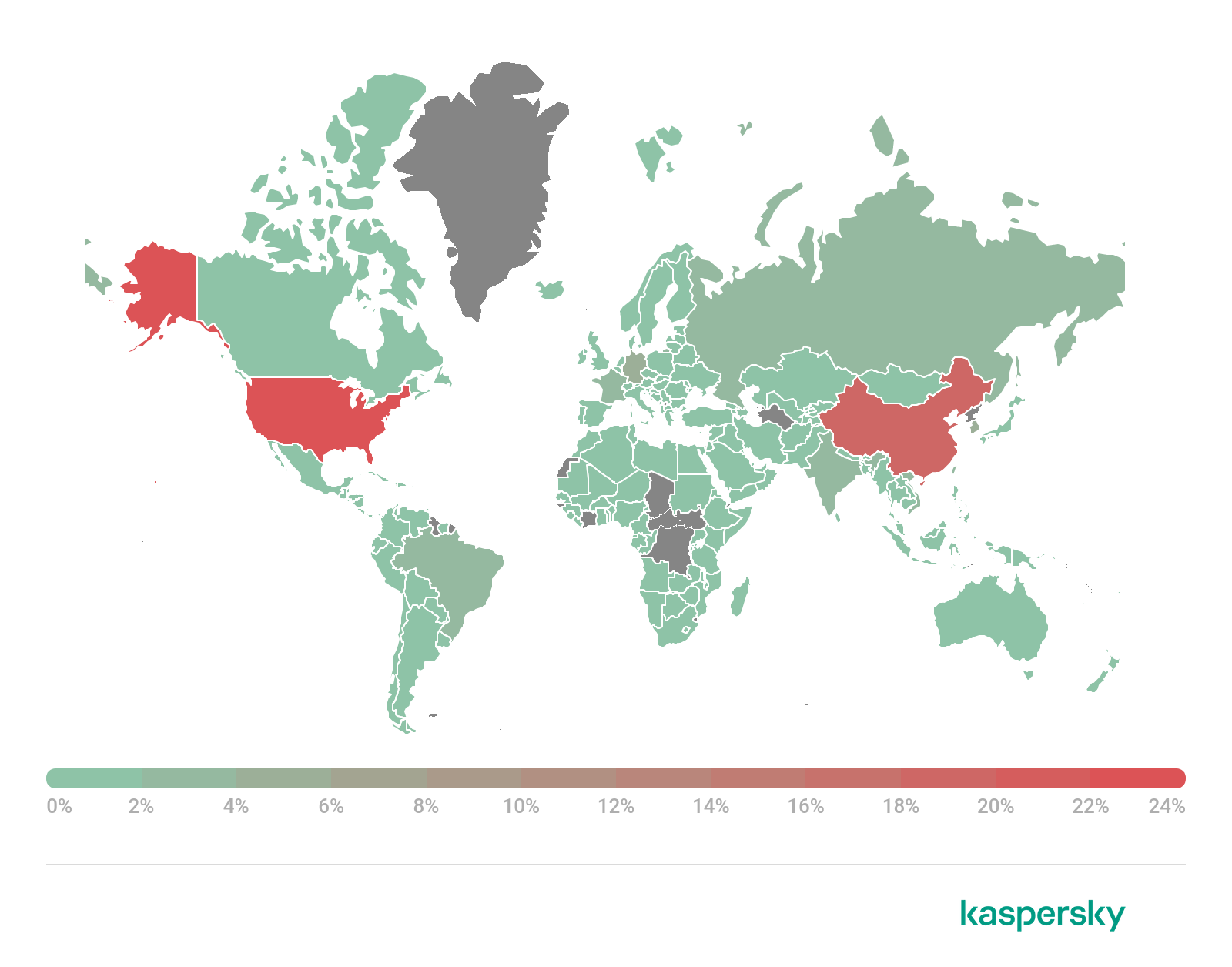
Attack geography
Geography of miner attacks, Q1 2021 (download)
Top 10 countries attacked by miners
| Country* | %** | |
| 1 | Afghanistan | 4.65 |
| 2 | Ethiopia | 3.00 |
| 3 | Rwanda | 2.37 |
| 4 | Uzbekistan | 2.23 |
| 5 | Kazakhstan | 1.81 |
| 6 | Sri Lanka | 1.78 |
| 7 | Ukraine | 1.59 |
| 8 | Vietnam | 1.48 |
| 9 | Mozambique | 1.46 |
| 10 | Tanzania | 1.45 |
* Excluded are countries with relatively few users of Kaspersky products (under 50,000).
** Unique users attacked by miners as a percentage of all unique users of Kaspersky products in the country.
Vulnerable applications used by cybercriminals during cyber attacks
In Q1 2021, we noted a drop in the share of exploits for vulnerabilities in the Microsoft Office suite, but they still lead the pack with 59%. The most common vulnerability in the suite remains CVE-2017-11882, a stack buffer overflow that occurs when processing objects in the Equation Editor component. Exploits for CVE-2015-2523 — use-after-free vulnerabilities in Microsoft Excel — and CVE-2018-0802, which we’ve often written about, were also in demand. Note the age of these vulnerabilities — even the latest of them was discovered almost three years ago. So, once again, we remind you of the importance of regular updates.
The first quarter was rich not only in known exploits, but also new zero-day vulnerabilities. In particular, the interest of both infosec experts and cybercriminals was piqued by vulnerabilities in the popular Microsoft Exchange Server:
- CVE-2021-26855— a service-side request forgery vulnerability that allows remote code execution (RCE)
- CVE-2021-26857— an insecure deserialization vulnerability in the Unified Messaging service that can lead to code execution on the server
- CVE-2021-26858— a post-authorization arbitrary file write vulnerability in Microsoft Exchange, which could also lead to remote code execution
- CVE-2021-27065— as in the case of CVE-2021-26858, allows an authorized Microsoft Exchange user to write data to an arbitrary file in the system
Found in the wild, these vulnerabilities were used by APT groups, including as a springboard for ransomware distribution.
During the quarter, vulnerabilities were also identified in Windows itself. In particular, the CVE-2021-1732 vulnerability allowing privilege escalation was discovered in the Win32k subsystem. Two other vulnerabilities, CVE-2021-1647 and CVE-2021-24092, were found in the Microsoft Defender antivirus engine, allowing elevation of user privileges in the system and execution of potentially dangerous code.

Distribution of exploits used by cybercriminals, by type of attacked application, Q1 2021 (download)
The second most popular were exploits for browser vulnerabilities (26.12%); their share in Q1 grew by more than 12 p.p. Here, too, there was no doing without newcomers: for example, the Internet Explorer script engine was found to contain the CVE-2021-26411 vulnerability, which can lead to remote code execution on behalf of the current user through manipulations that corrupt the heap memory. This vulnerability was exploited by the Lazarus group to download malicious code and infect the system. Several vulnerabilities were discovered in Google Chrome:
- CVE-2021-21148— heap buffer overflow in the V8 script engine, leading to remote code execution
- CVE-2021-21166— overflow and unsafe reuse of an object in memory when processing audio data, also enabling remote code execution
- CVE-2021-21139— bypassing security restrictions when using an iframe.
Other interesting findings include a critical vulnerability in VMware vCenter Server, CVE-2021-21972, which allows remote code execution without any rights. Critical vulnerabilities in the popular SolarWinds Orion Platform — CVE-2021-25274, CVE-2021-25275 and CVE-2021-25276 — caused a major splash in the infosec environment. They gave attackers the ability to infect computers running this software, usually machines inside corporate networks and government institutions. Lastly, the CVE-2021-21017 vulnerability, discovered in Adobe Reader, caused a heap buffer overflow by means of a specially crafted document, giving an attacker the ability to execute code.
Analysis of network threats in Q1 2021 continued to show ongoing attempts to attack servers with a view to brute-force passwords for network services such as Microsoft SQL Server, RDP and SMB. Attacks using the popular EternalBlue, EternalRomance and other similar exploits were widespread. Among the most notable new vulnerabilities in this period were bugs in the Windows networking stack code related to handling the IPv4/IPv6 protocols: CVE-2021-24074, CVE-2021-24086 and CVE-2021-24094.
Attacks on macOS
Q1 2021 was also rich in macOS-related news. Center-stage were cybercriminals who took pains to modify their malware for the newly released MacBooks with M1 processors. Updated adware for the new Macs also immediately appeared, in particular the Pirrit family (whose members placed high in our Top 20 threats for macOS). In addition, we detected an interesting adware program written in the Rust language, and assigned it the verdict AdWare.OSX.Convuster.a.
Top 20 threats for macOS
| Verdict | %* | |
| 1 | AdWare.OSX.Pirrit.ac | 18.01 |
| 2 | AdWare.OSX.Pirrit.j | 12.69 |
| 3 | AdWare.OSX.Pirrit.o | 8.42 |
| 4 | AdWare.OSX.Bnodlero.at | 8.36 |
| 5 | Monitor.OSX.HistGrabber.b | 8.06 |
| 6 | AdWare.OSX.Pirrit.gen | 7.95 |
| 7 | Trojan-Downloader.OSX.Shlayer.a | 7.90 |
| 8 | AdWare.OSX.Cimpli.m | 6.17 |
| 9 | AdWare.OSX.Pirrit.aa | 6.05 |
| 10 | Backdoor.OSX.Agent.z | 5.27 |
| 11 | Trojan-Downloader.OSX.Agent.h | 5.09 |
| 12 | AdWare.OSX.Bnodlero.bg | 4.60 |
| 13 | AdWare.OSX.Ketin.h | 4.02 |
| 14 | AdWare.OSX.Bnodlero.bc | 3.87 |
| 15 | AdWare.OSX.Bnodlero.t | 3.84 |
| 16 | AdWare.OSX.Cimpli.l | 3.75 |
| 17 | Trojan-Downloader.OSX.Lador.a | 3.61 |
| 18 | AdWare.OSX.Cimpli.k | 3.48 |
| 19 | AdWare.OSX.Ketin.m | 2.98 |
| 20 | AdWare.OSX.Bnodlero.ay | 2.94 |
* Unique users who encountered this malware as a percentage of all users of Kaspersky security solutions for macOS who were attacked.
Traditionally, most of the Top 20 threats for macOS are adware programs: 15 in Q1. In the list of malicious programs, Trojan-Downloader.OSX.Shlayer.a (7.90%) maintained its popularity. Incidentally, this Trojan’s task is to download adware from the Pirrit and Bnodlero families. But we also saw the reverse, when a member of the AdWare.OSX.Pirrit family dropped Backdoor.OSX.Agent.z into the system.
Threat geography
Geography of threats for macOS, Q1 2021 (download)
Top 10 countries by share of attacked users
| Country* | %** | |
| 1 | France | 4.62 |
| 2 | Spain | 4.43 |
| 3 | Italy | 4.36 |
| 4 | India | 4.11 |
| 5 | Canada | 3.59 |
| 6 | Mexico | 3.55 |
| 7 | Russia | 3.21 |
| 8 | Brazil | 3.18 |
| 9 | Great Britain | 2.96 |
| 10 | USA | 2.94 |
* Excluded from the rating are countries with relatively few users of Kaspersky security solutions for macOS (under 10,000)
** Unique users attacked as a percentage of all users of Kaspersky security solutions for macOS in the country.
In Q1 2021, Europe accounted for the Top 3 countries by share of attacked macOS users: France (4.62%), Spain (4.43%) and Italy (4.36%). The most common threats in all three were adware apps from the Pirrit family.
IoT attacks
IoT threat statistics
In Q1 2021, most of the devices that attacked Kaspersky traps did so using the Telnet protocol. A third of the attacking devices attempted to brute-force our SSH traps.
| Telnet | 69.48% |
| SSH | 30.52% |
Distribution of attacked services by number of unique IP addresses of devices that carried out attacks, Q1 2021
The statistics for cybercriminal working sessions with Kaspersky honeypots show similar Telnet dominance.
| Telnet | 77.81% |
| SSH | 22.19% |
Distribution of cybercriminal working sessions with Kaspersky traps, Q1 2021

Geography of IP addresses of devices from which attempts were made to attack Kaspersky Telnet traps, Q1 2021 (download)
Top 10 countries by location of devices from which attacks were carried out on Kaspersky Telnet traps
| Country | %* | |
| 1 | China | 33.40 |
| 2 | India | 13.65 |
| 3 | USA | 11.56 |
| 4 | Russia | 4.96 |
| 5 | Montenegro | 4.20 |
| 6 | Brazil | 4.19 |
| 7 | Taiwan, Province of China | 2.32 |
| 8 | Iran | 1.85 |
| 9 | Egypt | 1.84 |
| 10 | Vietnam | 1.73 |
* Devices from which attacks were carried out in the given country as a percentage of the total number of devices in that country.
SSH-based attacks
Geography of IP addresses of devices from which attempts were made to attack Kaspersky SSH traps, Q1 2021 (download)
Top 10 countries by location of devices from which attacks were made on Kaspersky SSH traps
| Country | %* | |
| 1 | USA | 24.09 |
| 2 | China | 19.89 |
| 3 | Hong Kong | 6.38 |
| 4 | South Korea | 4.37 |
| 5 | Germany | 4.06 |
| 6 | Brazil | 3.74 |
| 7 | Russia | 3.05 |
| 8 | Taiwan, Province of China | 2.80 |
| 9 | France | 2.59 |
| 10 | India | 2.36 |
* Devices from which attacks were carried out in the given country as a percentage of the total number of devices in that country.
Threats loaded into traps
| Verdict | %* | |
| 1 | Backdoor.Linux.Mirai.b | 50.50% |
| 2 | Trojan-Downloader.Linux.NyaDrop.b | 9.26% |
| 3 | Backdoor.Linux.Gafgyt.a | 3.01% |
| 4 | HEUR:Trojan-Downloader.Shell.Agent.bc | 2.72% |
| 5 | Backdoor.Linux.Mirai.a | 2.72% |
| 6 | Backdoor.Linux.Mirai.ba | 2.67% |
| 7 | Backdoor.Linux.Agent.bc | 2.37% |
| 8 | Trojan-Downloader.Shell.Agent.p | 1.37% |
| 9 | Backdoor.Linux.Gafgyt.bj | 0.78% |
| 10 | Trojan-Downloader.Linux.Mirai.d | 0.66% |
* Share of malware type in the total number of malicious programs downloaded to IoT devices following a successful attack.
Attacks via web resources
The statistics in this section are based on Web Anti-Virus, which protects users when malicious objects are downloaded from malicious/infected web pages. Cybercriminals create such sites on purpose; web resources with user-created content (for example, forums), as well as hacked legitimate resources, can be infected.
Countries that are sources of web-based attacks: Top 10
The following statistics show the distribution by country of the sources of Internet attacks blocked by Kaspersky products on user computers (web pages with redirects to exploits, sites containing exploits and other malicious programs, botnet C&C centers, etc.). Any unique host could be the source of one or more web-based attacks.
To determine the geographical source of web-based attacks, domain names are matched against their actual domain IP addresses, and then the geographical location of a specific IP address (GEOIP) is established.
In Q1 2021, Kaspersky solutions blocked 2,023,556,082 attacks launched from online resources located across the globe. 613,968,631 unique URLs were recognized as malicious by Web Anti-Virus.

Distribution of web attack sources by country, Q1 2021 (download)
Countries where users faced the greatest risk of online infection
To assess the risk of online infection faced by users in different countries, for each country we calculated the percentage of Kaspersky users on whose computers Web Anti-Virus was triggered during the quarter. The resulting data provides an indication of the aggressiveness of the environment in which computers operate in different countries.
This rating only includes attacks by malicious objects that fall under the Malware class; it does not include Web Anti-Virus detections of potentially dangerous or unwanted programs such as RiskTool or adware.
| Country* | % of attacked users** | |
| 1 | Belarus | 15.81 |
| 2 | Ukraine | 13.60 |
| 3 | Moldova | 13.16 |
| 4 | Kyrgyzstan | 11.78 |
| 5 | Latvia | 11.38 |
| 6 | Algeria | 11.16 |
| 7 | Russia | 11.11 |
| 8 | Mauritania | 11.08 |
| 9 | Kazakhstan | 10.62 |
| 10 | Tajikistan | 10.60 |
| 11 | Uzbekistan | 10.39 |
| 12 | Estonia | 10.20 |
| 13 | Armenia | 9.44 |
| 14 | Mongolia | 9.36 |
| 15 | France | 9.35 |
| 16 | Greece | 9.04 |
| 17 | Azerbaijan | 8.57 |
| 18 | Madagascar | 8.56 |
| 19 | Morocco | 8.55 |
| 20 | Lithuania | 8.53 |
* Excluded are countries with relatively few Kaspersky users (under 10,000).
** Unique users targeted by Malware-class attacks as a percentage of all unique users of Kaspersky products in the country.
These statistics are based on detection verdicts by the Web Anti-Virus module that were received from users of Kaspersky products who consented to provide statistical data.
On average, 7.67% of Internet user computers worldwide experienced at least one Malware-class attack.

Geography of web-based malware attacks, Q1 2021 (download)
Local threats
In this section, we analyze statistical data obtained from the OAS and ODS modules in Kaspersky products. It takes into account malicious programs that were found directly on users’ computers or removable media connected to them (flash drives, camera memory cards, phones, external hard drives), or which initially made their way onto the computer in non-open form (for example, programs in complex installers, encrypted files, etc.).
In Q1 2021, our File Anti-Virus detected 77,415,192 malicious and potentially unwanted objects.
Countries where users faced the highest risk of local infection
For each country, we calculated the percentage of Kaspersky product users on whose computers File Anti-Virus was triggered during the reporting period. These statistics reflect the level of personal computer infection in different countries.
Note that this rating only includes attacks by malicious programs that fall under the Malware class; it does not include File Anti-Virus triggers in response to potentially dangerous or unwanted programs, such as RiskTool or adware.
| Country* | % of attacked users** | |
| 1 | Afghanistan | 47.71 |
| 2 | Turkmenistan | 43.39 |
| 3 | Ethiopia | 41.03 |
| 4 | Tajikistan | 38.96 |
| 5 | Bangladesh | 36.21 |
| 6 | Algeria | 35.49 |
| 7 | Myanmar | 35.16 |
| 8 | Uzbekistan | 34.95 |
| 9 | South Sudan | 34.17 |
| 10 | Benin | 34.08 |
| 11 | China | 33.34 |
| 12 | Iraq | 33.14 |
| 13 | Laos | 32.84 |
| 14 | Burkina Faso | 32.61 |
| 15 | Mali | 32.42 |
| 16 | Guinea | 32.40 |
| 17 | Yemen | 32.32 |
| 18 | Mauritania | 32.22 |
| 19 | Burundi | 31.68 |
| 20 | Sudan | 31.61 |
* Excluded are countries with relatively few Kaspersky users (under 10,000).
** Unique users on whose computers Malware-class local threats were blocked, as a percentage of all unique users of Kaspersky products in the country.
Geography of local infection attempts, Q1 2021 (download)
Overall, 15.05% of user computers globally faced at least one Malware-class local threat during Q1.

















IT threat evolution Q1 2021. Non-mobile statistics