
Yanluowang is a type of targeted ransomware discovered by the Symantec Threat Hunter team as they were investigating an incident on a large corporate network. Kaspersky experts have found a vulnerability in the Yanluowang encryption algorithm and created a free decryptor to help victims of this ransomware with recovering their files.
Yanluowang description
The ransomware is relatively recent, its name a reference to the Chinese deity Yanluo Wang, one of the Ten Kings of Hell. Unfortunately, we do not know much about the victims. According to Kaspersky Security Network data, attacks have been carried out in the United States, Brazil, Turkey and a few other countries. The low number of infections is due to the targeted nature of the ransomware: threat actors prepare and implement attacks on specific companies only.

Geography of the Yanluowang attacks, December 4th, 2021 – April 8th, 2022 (download)
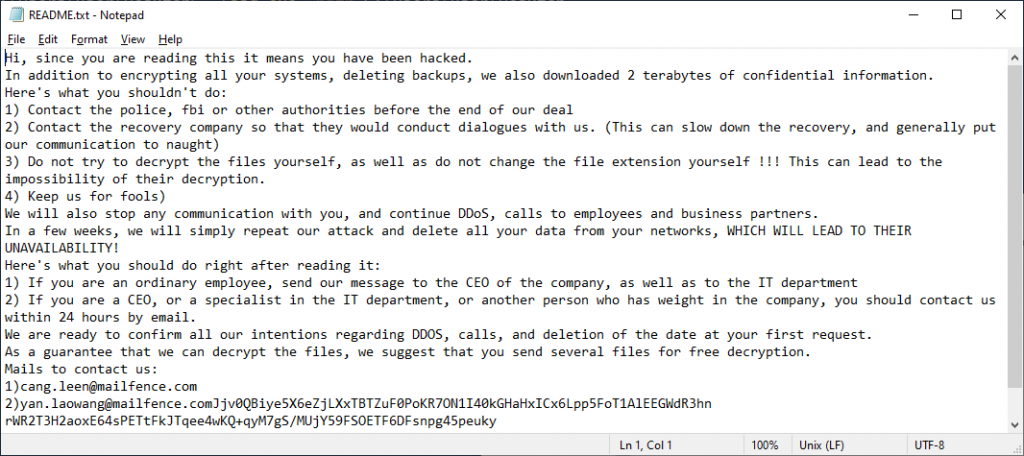
In the ransom note, the cybercriminals demand not to contact law enforcement and not ‘keep them for fools’:
The ransomware program has the functionality to terminate virtual machines, processes and services. This is necessary to make files used by other programs available for encryption. The main parts of stopped services and processes include databases, email services, browsers, programs for working with documents, security solutions, backups and shadow copy services.
 |
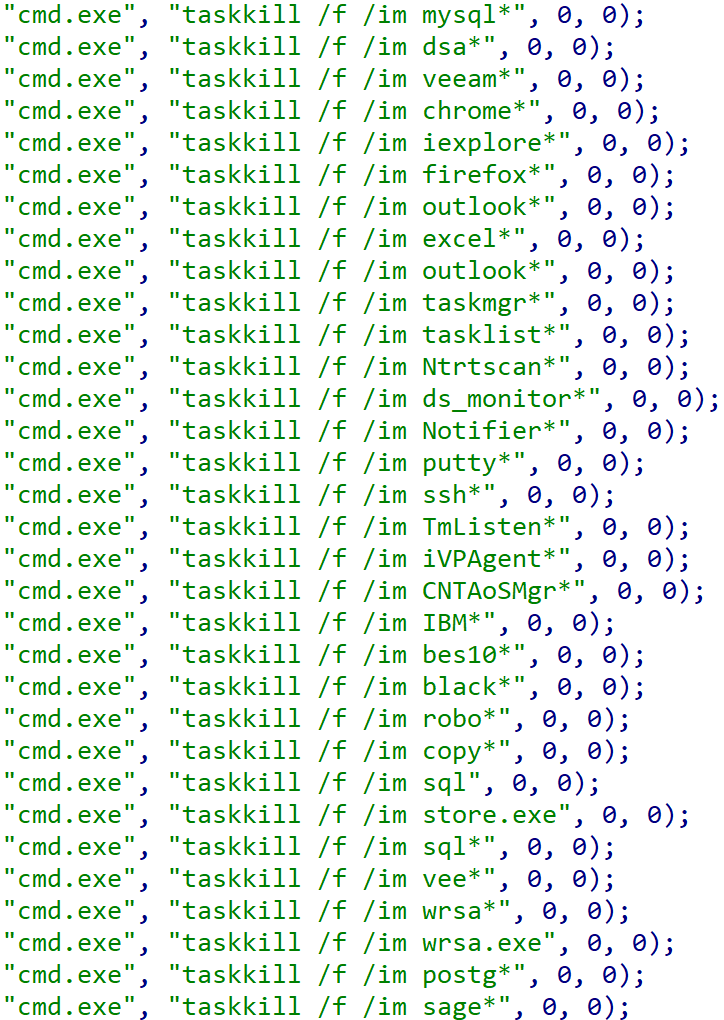 |
Lists of stopped services and processes
According to public information about the ransomware, it is only used in targeted attacks rather than in other RaaS families. Yanluowang itself needs parameters to be executed in the system, meaning it will be executed either manually or through a combination of scripts in the compromised system. The available syntax in the ransomware is:
|
1 |
encrypt.exe [(-p,-path,--path)<path>] |
The Sosemanuk stream cipher is used to encrypt files, its key then encrypted using the RSA-1024 asymmetric algorithm. The RSA public key itself is embedded in the program but additionally encrypted with the RC4 stream cipher whose key is a string and also embedded in ransomware. Files before and after encryption:
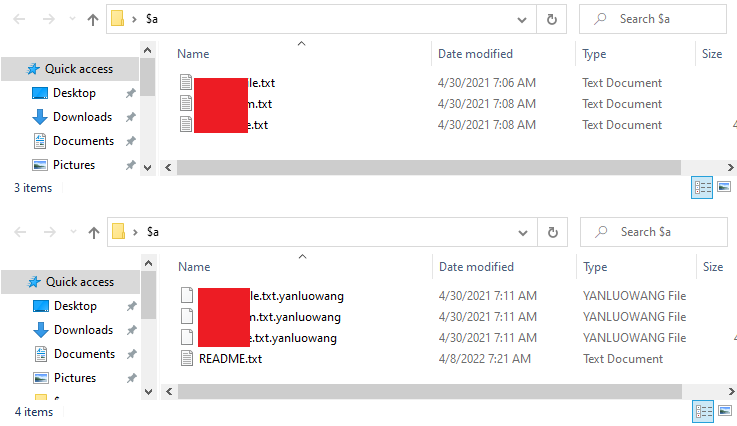
When the encryption process is completed, the file extensions will be changed to .yanluowang
Yanluowang divides files into big and small along a 3 GB threshold. Small files are encrypted completely from beginning to end, big files are encrypted in stripes: 5 megabytes after every 200 megabytes.
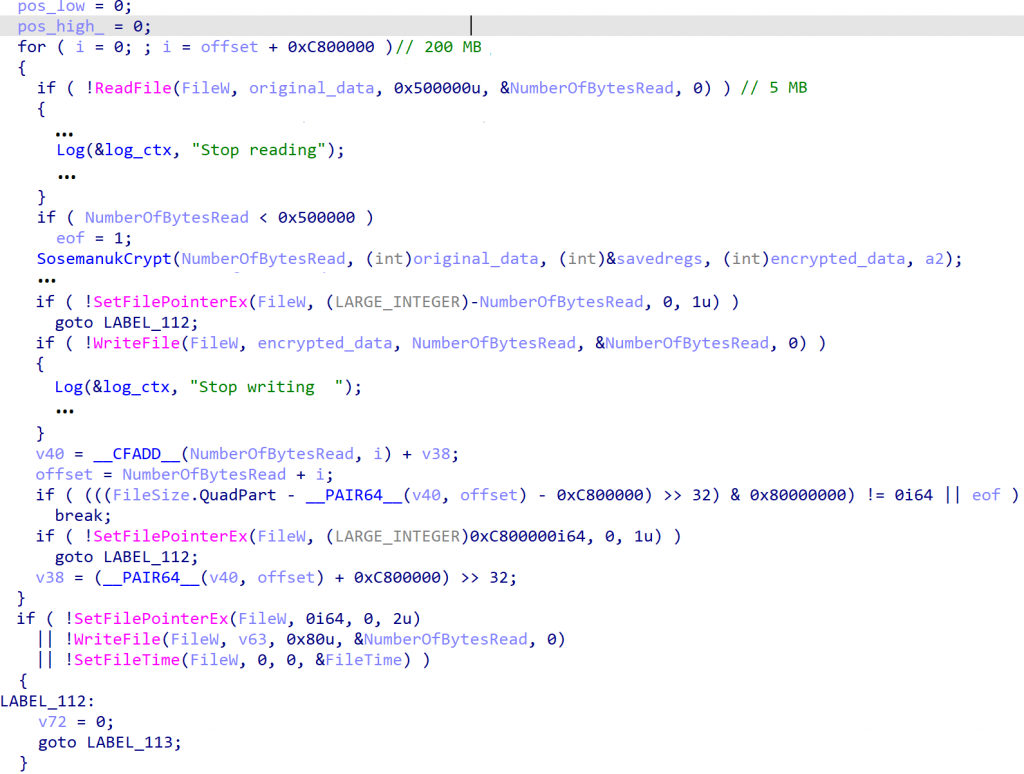
The encryption code for big files
After a file is encrypted, an RSA-encrypted Sosemanuk key is written to the end of it. The encrypted endfile block has a size of 1024 bytes.
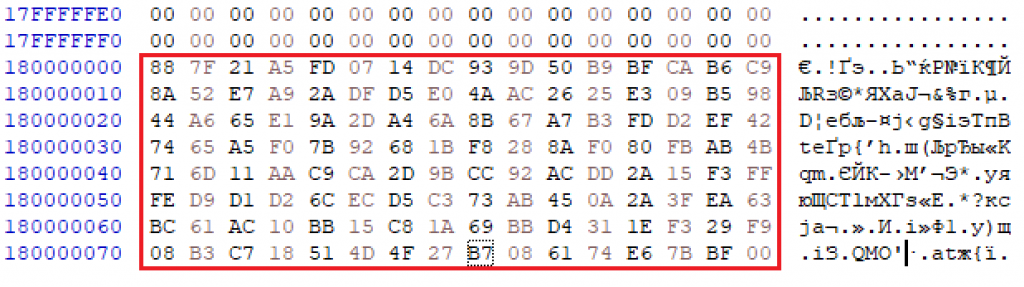
An encrypted block with a Sosemanuk key
Files decryption
Kaspersky experts have analyzed the ransomware and found a vulnerability that allows decrypting files of affected users via a known-plaintext attack. All that was required for this to work was added to the Rannoh decryption tool.
To decrypt a file, you should have at least one original file. As mentioned earlier, the Yanluowang ransomware divides files into big and small files along a 3 gigabyte threshold. This creates a number of conditions that must be met in order to decrypt certain files:
- To decrypt small files (less than or equal to 3 GB), you need a pair of files with a size of 1024 bytes or more. This is enough to decrypt all other small files.
- To decrypt big files (more than 3 GB), you need a pair of files (encrypted and original) no less than 3 GB in size each. This will be enough to decrypt both big and small files.
By virtue of the above points, if the original file is larger than 3 GB, it is possible to decrypt all files on the infected system, both big and small. But if there is an original file smaller than 3 GB, then only small files can be decrypted.
Indicators of Compromise
Kaspersky solutions detect and protect against this ransomware, detecting it as Trojan-Ransom.Win32.Yanluowang with File Threat Protection and proactively as PDM:Trojan.Win32.Generic with Behavior Detection.
MD5
afaf2d4ebb6dc47e79a955df5ad1fc8a
ba95a2f1f1f39a24687ebe3a7a7f7295
Piece of advice
Still, it is important for a company to have a security solution that would enable instant response to such ransomware threats in order to avoid large financial losses. Yanluowang was deployed in targeted human-operated attacks. As usual in such cases, we would like to remind you that a comprehensive cybersecurity strategy is required to protect against this type of threats.
Here are Kaspersky’s recommendations for staying safe from ransomware attacks:
- Do not expose remote desktop services (such as RDP) to public networks unless absolutely necessary, and always use strong passwords.
- Promptly install available patches for commercial VPN solutions that provide access for remote employees and act as gateways to your network.
- Always keep software up to date on all your devices to prevent ransomware from exploiting vulnerabilities.
- Focus your defense strategy on detecting lateral movement and data exfiltration to the Internet. Pay special attention to outgoing traffic to detect cybercriminals’ connections.
- Back up data regularly. Make sure you can quickly access your backups in an emergency.
- To protect the corporate environment, educate your employees. Dedicated training courses can help, such as the ones provided on Kaspersky Automated Security Awareness Platform.
- Use the latest Threat Intelligence information to stay on top of actual TTPs used by threat actors.
- Use solutions like Kaspersky Endpoint Detection and Response and Kaspersky Managed Detection and Response service which help to identify and stop an attack in the early stages, before attackers can achieve their objectives.
- Use a reliable endpoint security solution, such as Kaspersky Endpoint Security for Business, that is powered by exploit prevention, behavior detection and a remediation engine capable of rolling back malicious actions. KESB also has self-defense mechanisms that can prevent its removal by cybercriminals.
How to recover files encrypted by Yanluowang


















Joshua Ajao
I used my dad’s laptop to download some apps. while opening the files I observe files on the computer change to TOHU files. This will be the second time. Few years ago I encountered same problem when my dad’s files were changed into PRQS files, which cannot be recovered to date. My dad warned me, but he traveled for the weekend and I used his laptop and I am in Big trouble now. Please kindly save me. I believe you can!
Securelist
Hi Joshua!
A number of decryption tools are available here: https://noransom.kaspersky.com/. You can use Crypto Sheriff service (https://www.nomoreransom.org/crypto-sheriff.php?lang=en) to find out what malware has encrypted your files, and then check whether the decryptor for this malware already exists.
You can also restore your files from backup if you have any. If you are not sure, it is better to wait till your father is back, and not to make things worse by acting panicky.
Ditiro
Can you plis help with decryption on a zip file.
Securelist
Hi Ditrio!
To check, which ransomware has encrypted your files, use Crypto Sheriff: https://www.nomoreransom.org/crypto-sheriff.php?lang=en.
If you know, which ransomware has encrypted your files, search for a decryptor here: https://noransom.kaspersky.com/ and here: https://www.nomoreransom.org/en/decryption-tools.html.
If you haven’t found the decryptor or it doesn’t work, you may come back later: the tools are updated, and new decryptors are added from time to time. You also can contact Kaspersky tech support, if you are a paid Kaspersky product user: https://support.kaspersky.ru/b2c/ru