
Yesterday the Iranian CERT made an announcement about a new piece of wiper-like malware.
We detect these files as Trojan.Win32.Maya.a.
This is an extremely simplistic attack. In essence, the attacker wrote some BAT files and then used a BAT2EXE tool to turn them into Windows PE files.
The author seems to have used (a variant of) this particular BAT2EXE tool.
There’s no connection to any of the previous wiper-like attacks we’ve seen. We also don’t have any reports of this malware from the wild.
The destructive payload is very simple. The malware checks if the date matches with a number of pre-defined dates.
If the date matches it will wait for 50 minutes and then try to delete all files from drive D through I. It will also wipe all files from the user’s desktop.
Dates:
2012/12/10-12
2013/01/21-23
2013/05/06-08
2013/07/22-24
2013/11/11-13
2014/02/03-05
2014/05/05-07
2014/08/11-13
2015/02/02-04
Clearly, the attacker was trying to think ahead.
After trying to delete all the files on a particular partition the malware runs chkdsk on said partition.
I assume the attacker is trying to make the loss of all files look like a software or hardware failure.
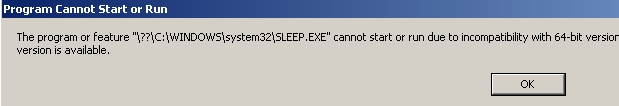
Next to these BAT2EXE files there’s also a 16-bit SLEEP file, which is not malicious. 16-bit files don’t actually run on 64-bit versions of Windows.
This immediately gives away the malware’s presence on a x64 machine.
Other than the geographic region there doesn’t seem to be any commonality with this file-deleting malware and the previous attacks we’ve seen.
Even though the code is extremely simplistic it loooks like the author managed to slip in a mistake, by not deleting a line of old code.
This is as basic as it gets. But if it was effective that doesn’t matter.
If it wasn’t clear already – the era of cyber-sabotage has arrived. Be prepared.





















GrooveMonitor: Another Wiper Copycat?