
We always expect a rise in cyber crime in the holiday season. This year, for instance, we have seen a noticeable rise in spam, along with a rise in phishing.
I have even received a phishing email in my Gmail mailbox – the first one in ages. The phish was nothing special; the usual notification about a new payment system for an online bank with a link to the spoofed website.
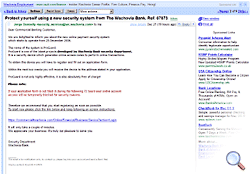
What caught my eye was how Google handled the phish. The Gmail interface added a number of relevant paid advertising links to the email. Take a look at the upper left and lower right corners:
I think that adding such links increase user trust in fraudulent emails. Users see that Google has included keyword-related links, so they are liable to trust the email – and fall victim to the phishing scam.
What do you think? In any case, holidays are unfortunately a busy time for criminals in all spheres, including the Internet. Take care of yourself and safe surfing!






















Google helps phishers