
Mobile Trojans, which send SMS messages to premium pay numbers; fake antivirus software, which finds ‘infections’ on your computer that you’ll have to pay to have cured; Trojan ransomware, which prevents infected systems from functioning normally and demands money in return for restoring functionality.
All these types of malware get regular coverage and we’re seeing (and writing about them) on an ever more frequent basis.
And now we’ve got a sort of three-in-one, a nasty little program called Trojan.Win32.KillProc.am. So far, we’ve seen three variants of this, and two of them get detected under a different name – Trojan-Ransom.Win32.BHO.a and .b.
This Trojan is a Browser Helper Object which attacks Internet Explorer. If your machine is infected, you’re going to get a less than pleasant surprise. Instead of showing you your favourite sites, your browser will start to load part of Microsoft’s Russian site – the part devoted to antipiracy and legitimate software.Take a look at the two screenshots below. Even non-Russian speakers will be able to see at a glance that they’re different (while Russian speakers can get some language practice in!)
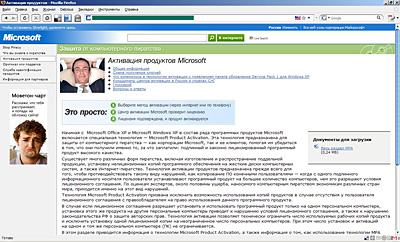
The first screenshot shows a genuine Microsoft page devoted to anti-piracy measures and the company’s Product Activation technology.
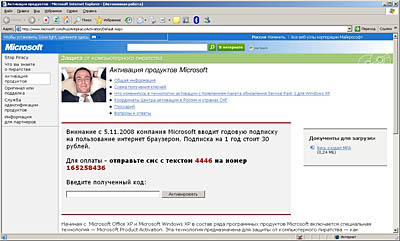
The second page is the fake; the text of this page is contained in the body of the Trojan and of course, it’s giving a very different message. (Incidentally, when the browser displays this fake page, it does display exactly the same URL as the genuine page.)
It’s a sophisticated piece of work; the two pages are extremely similar, and even experienced users could be fooled. The message displayed in the grey box in the middle of the fake page reads as follows:
Attention: from 5.11.2008, Microsoft is introducing a yearly subscription for the use of its Internet browser. A one year subscription costs 30 roubles.
To pay – send an SMS with the text 4446 to 165258436.
Enter the code you receive.
[Translator’s note: The button on the right hand side of the message says ‘Activation’].
So it looks as though the author of this Trojan is a Russian speaker who’s decided to make himself a bit of cash using SMS payments – an approach popular among virus writers at the moment. 30 roubles isn’t a huge amount – around $1.10 – but clearly every little helps in the current economic climate.
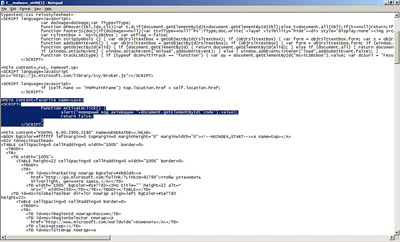
What happens if the user believes the nonsense about an annual subscription, and sends off an SMS to the number shown? Of course, money’s going to be deducted from his/her mobile account. But there’s more to it than that –the browser won’t start working again when s/he enters an activation code. Another message will be displayed, saying ‘Vvedennyii kod neveren’ [The code entered is wrong]. This message is hard coded into the Trojan as the screenshot below shows.
Either this Trojan was written by someone who writes buggy code; or the author’s got a twisted sense of humour; or s/he’s simply out to make as much money as s/he can. After all, s/he might think, if a user’s dumb enough to send one SMS, maybe s/he’ll just assume something went wrong, and send a second SMS…or even a third one in the hope of getting a working activation code…and this’ll put more money in my pockets!
The only way to get things up and running again will be to either clean the infected system with an antivirus product, or switch from Internet Explorer to a different browser.
We’ve contacted the organization sub-leasing the short number being used, and hope that they’ll put a stop to this criminal activity.
In the meantime, if you’ve fallen victim to this, or similar Trojans which send SMS messages, try talking to your mobile operator. They might be willing to reimburse any money you’ve lost.





















Every little helps?