
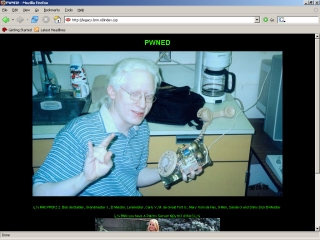
It came to our attention today that the website of one of the Dutch TV broadcasters had been defaced. So we contacted them and informed them in case they weren’t aware of the issue yet.
I was told on the phone that the station wasn’t aware of the issue and that they would look into ASAP. However, after 15 minutes or so, the site still hadn’t been taken down – I started to think that it might be a hoax.
This channel is well known for its attention grabbing tricks, and it occurred to me that this would fit their image nicely. And indeed, the ‘defacement’ turned out to be a (viral) marketing stunt.
As I clearly identified myself as being from a security company, I don’t think they were right to withhold this information from me. There are two reasons for this – firstly, I’m well aware of confidentiality issues, and secondly, I could have spent the time researching other, genuine, virus related issues.




















Defacement or hoax?