
News overview
In Q4 2018, security researchers detected a number of new botnets, which included not only Mirai clones for a change. The fall saw increased activity on the part of the Chalubo bot, whose first attacks were registered in late August. Although the new malware employs snippets of Mirai code and the same persistence techniques as in the Xor.DDoS bot family, Chalubo is mostly a fresh product designed solely for DDoS attacks (for example, one of the detected samples was a SYN flood one). In October, Chalubo began to be seen more often in the wild; researchers detected versions created for different architectures (32- and 64-bit ARM, x86, x86_64, MIPS, MIPSEL, PowerPC), which strongly suggests that the test period is over.
Also in October, details were released of the new Torii botnet, which Avast experts detected a month earlier. The botnet is aimed at a wide range of IoT devices and architectures. Its code differs significantly from Mirai — the malware is better hidden with a higher level of persistence, and thus promises to be far more dangerous. The malware collects and sends detailed information about infected devices to its C&C server, including host name and process ID, but for what purpose remains unclear. No DDoS attacks based on Torii botnets were detected, but experts believe that it’s still early days.
Another bot from last quarter, nicknamed DemonBot, caught the eye for hijacking Hadoop clusters through a vulnerability in the execution of YARN remote commands. This bot is not very complex technically, but dangerous in its choice of target: Hadoop clusters pack a major punch in terms of computing power because they are designed to handle Big Data. What’s more, being cloud-integrated, they can significantly boost DDoS attacks. Radware is currently monitoring 70 active servers that carry out up to 1 million infections per day. DemonBot is compatible not only with Hadoop clusters, but with most IoT devices, which makes it easy to re-aim at more numerous targets.
Last quarter, experts warned not only about new botnets, but new attack mechanisms, too. At the beginning of winter, for instance, it turned out that FragmentSmack was more widely deployable than previously thought. This attack exploits a vulnerability in the IP stack, which enables defective packets to be sent disguised as fragments of a larger message. The resource under attack tries to gather these packets into one, or places them in an endless queue, which takes up all its computational power and renders it incapable of handling legitimate requests. FragmentSmack was believed to be a threat only to Linux systems, but in December researchers from Finland discovered that it works fine with Windows 7, 8.1, 10, Windows Server, and 90 Cisco products.
Another promising attack method uses the CoAP protocol approved for widespread application in 2014. It is designed to facilitate communication between devices with a small amount of memory, making it ideal for the IoT. Since CoAP is based on the UDP protocol, it has inherited all the latter’s defects, which means it can be harnessed to boost DDoS attacks. Until now, this has not been a significant problem; however, experts note that during the November 2017–November 2018 period, the number of devices using CoAP increased almost 100 times, which is a major cause for concern.
Alongside new potential means for staging attacks, late 2018 saw the arrival of a new DDoS launch platform, called 0x-booter. First discovered on October 17, 2018, the service can support attacks with a capacity of up to 420 Gb/s based on just over 16,000 bots infected with Bushido IoT malware, a modified version of Mirai. Borrowing code from this kindred service, the platform is dangerous for its simplicity, low cost, and relative power: For just $20–50, anyone can use the simple interface to launch one of several types of attack against a target. According to the researchers, in the second half of October alone the service was utilized in more than 300 DDoS attacks.
It was with such resources that a powerful DDoS campaign was carried out throughout October against Japanese video game publisher Square Enix. The first wave came at the start of the month, coinciding with an attack on their French colleagues from Ubisoft (seemingly timed for the release of Assassin’s Creed Odyssey on October 4). The second wave hit a couple of weeks later. The attacks cut users off from the service for up to 20 hours.
Other than that, the end of the year was marked less by high-profile DDoS attacks than by attempts to reduce their frequency. Based on a report by cybersecurity researchers, the US Council on Foreign Relations (CFR) called for a global initiative of both public and private organizations to reduce the number of botnets.
Nor are law enforcement agencies asleep at the wheel. In October, US citizen Austin Thompson was found guilty of organizing a number of DDOS attacks in 2013–14. His victims included video game streamers as well as major game developers EA, Sony, Microsoft, and others.
In early December, British teenager George Duke-Cohan, who organized DDoS attacks against IT blogger Brian Krebs, the DEF CON convention, and government organizations in several countries, was sentenced to three years in prison — but not as yet for these incidents, but for making bomb hoax threats to numerous British schools and San Francisco Airport. Further charges could be brought against him in the US.
And around Christmas time, the FBI put a stop to 15 DDoS-as-a-Service sites, charging three suspects with running the platforms. The operation is of interest because many of the domains brought down had long escaped the eyes of the law by masquerading as stress testing sites. As the FBI uncovered, some of the services were complicit in a recent string of attacks on gaming portals.
Quarter and year trends
In 2018, we recorded 13% less DDoS activity than in the previous year. A drop in the number of attacks over this period was observed in each quarter, except the third, which outstripped Q3 2017 due to an anomalously active September. The biggest decrease was seen in Q4, with the number of attacks only 70% of the 2017 figure.
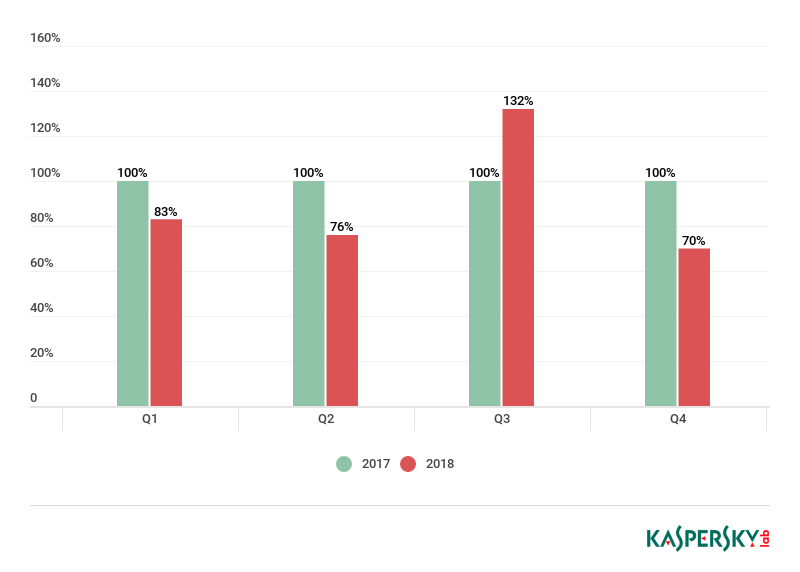
Quarterly comparison of the number of DDoS attacks defeated by Kaspersky DDoS Protection in 2017–2018 (100% = number of attacks in 2017)
The average duration of attacks in H2 grew steadily over the year: from 95 minutes in Q1 to 218 in Q4.
The most common type of attack by a wide margin is UDP flooding, as reflected in our reports for the last few quarters. However, when comparing attacks by their duration, the situation is quite different. First place goes to HTTP floods and mixed attacks with an HTTP element — they account for around 80% of all DDoS attack activity. Conversely, the UDP attacks we observed this year rarely lasted more than 5 minutes.
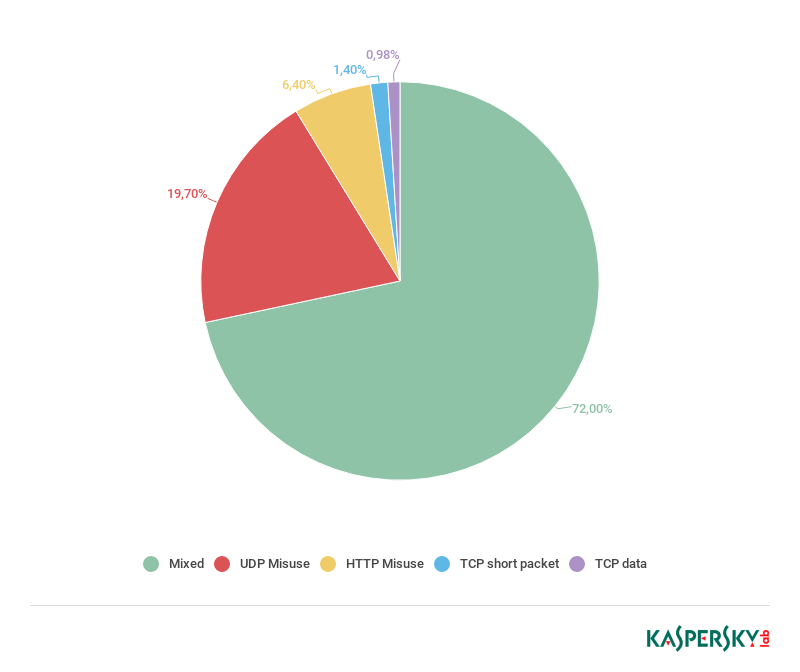
Distribution of attack duration by type, 2018
All this suggests that the market for unsophisticated, easy-to-organize attacks continues to shrink, as we predicted would happen. Standard DDoS attacks have been rendered almost pointless by improved anti-UDP flood protection, plus the fact that the technical resources involved are nearly always more profitably deployed for other purposes, such as cryptocurrency mining.
Many short attacks of this kind can be interpreted as simply testing the water (on the off-chance that the target is not secure). It only takes a few minutes for the cybercriminals to figure out that their tools are ineffective and call off the attack.
At the same time, more complex attacks such as HTTP floods, which require time and effort to arrange, remain popular, and their duration is on an upward curve.
These trends look set to develop further in 2019: the total number of attacks will fall amid growth in the duration, power, and impact of well-targeted offensives. A rise in professionalism is also in the cards. Given that most resources are totally unaffected by primitive attempts to disrupt their operation, DDoS attack organizers will have to raise their technical level, as their clients would seek out more professional implementers.
Statistics
Methodology
Kaspersky Lab has a long history of combating cyber threats, including DDoS attacks of all types and complexity. Company experts monitor botnets using the Kaspersky DDoS Intelligence system.
A part of Kaspersky DDoS Protection, the DDoS Intelligence system intercepts and analyzes commands received by bots from C&C servers. The system is proactive, not reactive, meaning that it does not wait for a user device to get infected or a command to be executed.
This report contains DDoS Intelligence statistics for Q4 2018.
In the context of this report, the incident is counted as a single DDoS-attack only if the interval between botnet activity periods does not exceed 24 hours. For example, if the same web resource was attacked by the same botnet with an interval of 24 hours or more, then this is considered as two attacks. Bot requests originating from different botnets but directed at one resource also count as separate attacks.
The geographical locations of DDoS-attack victims and C&C servers used to send commands are determined by their respective IP addresses. The number of unique targets of DDoS attacks in this report is counted by the number of unique IP addresses in the quarterly statistics.
DDoS Intelligence statistics are limited to botnets detected and analyzed by Kaspersky Lab. Note that botnets are just one of the tools used for DDoS attacks, and that this section does not cover every single DDoS attack that occurred during the review period.
Quarter summary
- China still tops the leaderboard by number of DDoS attacks, but its share fell quite significantly, from 77.67% to 50.43%. The US retained second position (24.90%), and Australia came third (4.5%). The Top 10 waved goodbye to Russia and Singapore, but welcomed Brazil (2.89%) and Saudi Arabia (1.57%).
- By geographical distribution of targets, the leaders remain China (43.26%), the US (29.14%), and Australia (5.91%). That said, China’s share fell significantly, while all other Top 10 countries increased theirs.
- Most of the botnet-based attacks last quarter occurred in October; holiday and pre-holiday periods were calmer. In terms of weekly dynamics, attack activity rose mid-week and decreased towards the end.
- Q4 witnessed the longest attack seen in recent years, lasting almost 16 days (329 hours). In general, the share of short attacks decreased slightly, but the fluctuations were minor.
- The share of UDP floods increased significantly to almost a third (31.1%) of all attacks. However, SYN flooding is still leading (58.2%).
- In connection with the rising number of Mirai C&C servers, the shares of the US (43.48%), Britain (7.88%), and the Netherlands (6.79%) increased.
Attack geography
In the last quarter of 2018, China still accounted for most DDoS attacks. However, its share was down by more than 20 p.p.: from 77.67% to 50.43%.
Meanwhile, the share of the US, which took second place, almost doubled to 24.90%. As in the previous quarter, bronze went to Australia. Its share also practically doubled: from 2.27% to 4.5%. Hong Kong’s share rose only slightly (from 1.74% to 1.84%), causing it to drop to sixth place, ceding fourth position to Brazil. The latter’s indicators had been quite modest up to now, but this quarter its share was 2.89%.
An unexpected newcomer in the ranking was Saudi Arabia, whose share climbed to 1.57%, good enough for seventh spot. This time, the Top 10 had no room for Russia and Singapore. South Korea, having ranked in the Top 3 for several years before dropping to 11th in Q3, not only failed to return to the Top 10, but fell even lower, nosediving to 25th.
The shares of the other top-tenners also increased compared with summer and early fall. The same applies to the total share of countries outside the Top 10 — it increased by more than 5 p.p., from 2.83% to 7.90%.

Distribution of DDoS attacks by country, Q3 and Q4 2018
The distribution of targets by country corresponds to the distribution pattern for number of attacks: China still leads, but its share fell by just over 27 p.p., from 70.58% to 43.26%. The US remains second, although its share grew from 17.05% to 29.14%. Third place again belongs to Australia, also with an increased share (5.9%).
Russia and South Korea, until recently considered Top 10 regulars, slipped well down — as in the rating by number of attacks, they finished 17th and 25th, respectively. They were replaced by new entrants Brazil (2.73%) in fourth place and Saudi Arabia (2.23%) in fifth. The shares of all other countries, as in the previous ranking, also rose slightly. Twofold growth was observed in the case of Canada (from 1.09% to 2.21%), whose results in the past few quarters have fluctuated around 1%, never exceeding 1.5%.
The share of the countries outside of Top 10 almost tripled: from 3.64% to 9.32%.
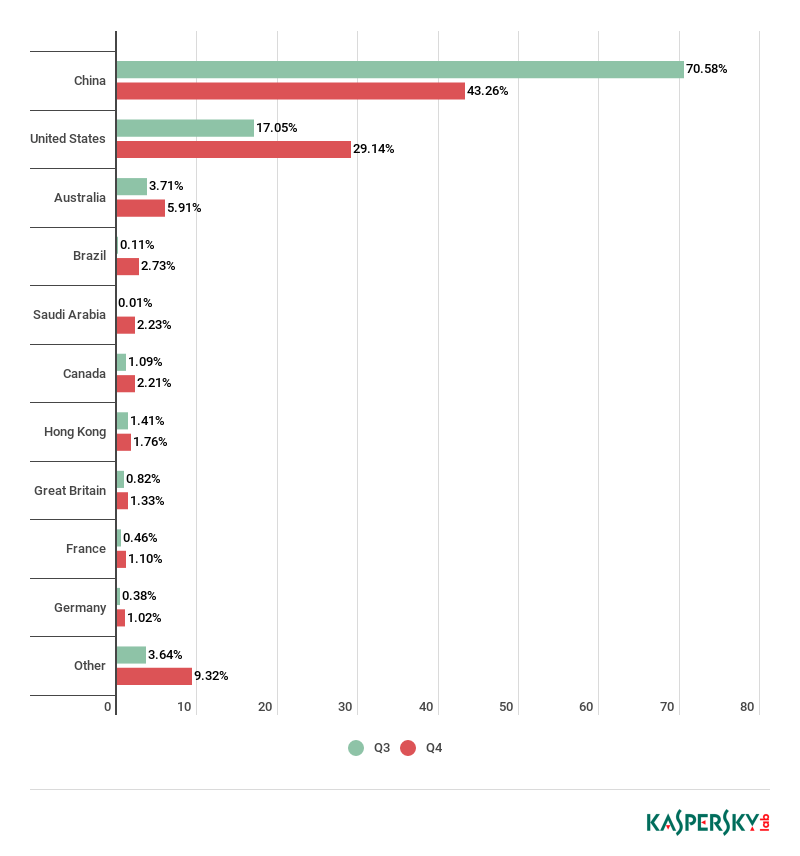
Distribution of unique DDoS-attack targets by country, Q3 and Q4 2018
Dynamics of the number of DDoS attacks
Most of the attack peaks occurred at the start of the quarter (October), with another small surge of activity coming in early December. Unlike last year, there were no clear-cut spikes connected to the autumn and winter holidays, rather the opposite: post-festive periods were quieter. The stormiest days were October 16 and 18, and December 4; the calmest was December 27.
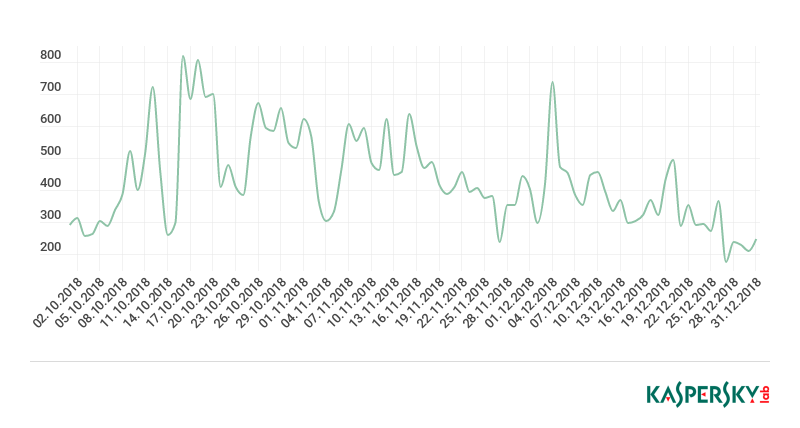
Dynamics of the number of DDoS attacks in Q4 2018
Whereas Q3 attacks were distributed relatively evenly over the days of the week, in Q4 the differences were more pronounced. The quietest day was Sunday (12.02% of attacks), the most active was Thursday: 15.74% of DDoS attacks occurred mid-week. Some correlation can be seen here with the distribution of attacks by date: both weekends and holidays in the previous quarter were calmer.
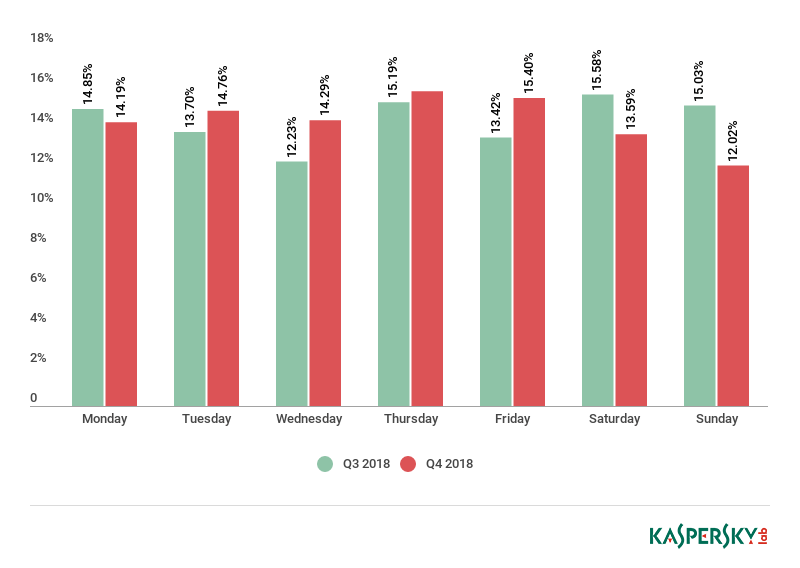
Distribution of DDoS attacks by day of the week, Q3 and Q4 2018
Duration and types of DDoS attacks
The longest Q4 attack we monitored lasted a near record-breaking 329 hours (almost 14 days); for a longer attack, we have to go back to late 2015. That is approximately 1.5 times the duration of the previous quarter’s longest attack of 239 hours (about 10 days).
The total share of attacks longer than 140 hours in the previous quarter increased only slightly (+0.01 p.p.) to 0.11%. The proportion of relatively long attacks (50–139 hours) also increased, from 0.59% to 1.15%. However, the most significant rise was observed in the category of 5–9 hour attacks: from 5.49% to 9.40%.
Accordingly, the share of short attacks less than 4 hours in duration decreased slightly, to 83.34%. For comparison, in Q3 they accounted for 86.94% of all attacks.
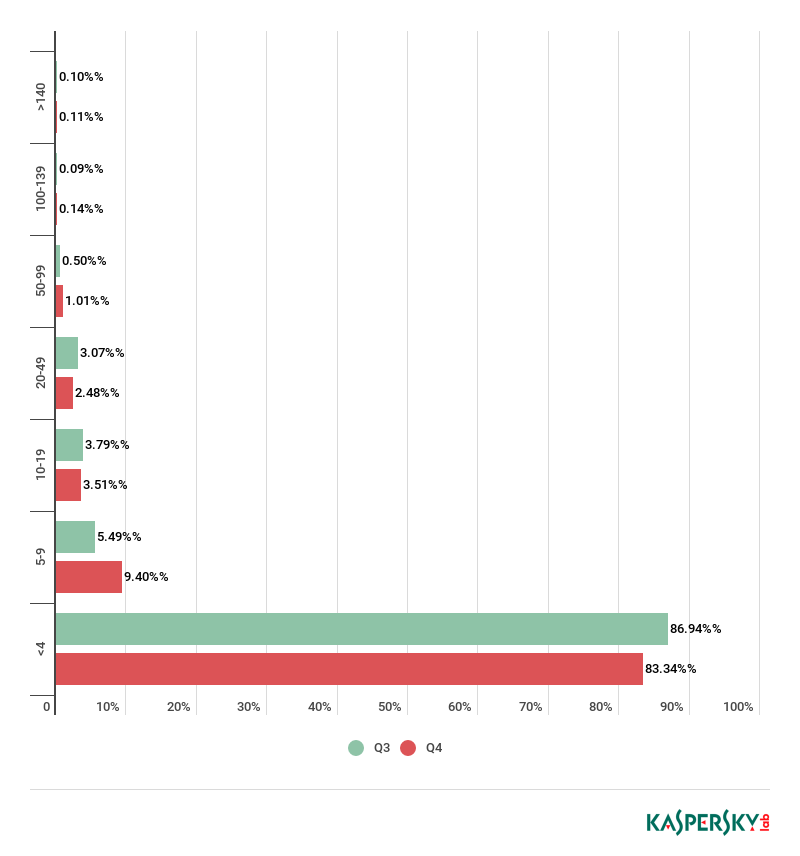
Distribution of DDoS attacks by duration (hours), Q3 and Q4 2018
The distribution of attacks by type in the last quarter underwent a bit of a shakeup. SYN flooding remains the most common, but its share dropped from 83.20% to 58.20%. That allowed UDP flooding to increase its share to almost a third of all types of DDoS attacks (31.10%), up from the more modest 11.90% in Q3.
In third place was TCP flooding, whose share also rose — to 8.40%. The share of attacks via HTTP dropped to 2.20%. In last place again, with its share falling to 0.10%, was ICMP flooding.
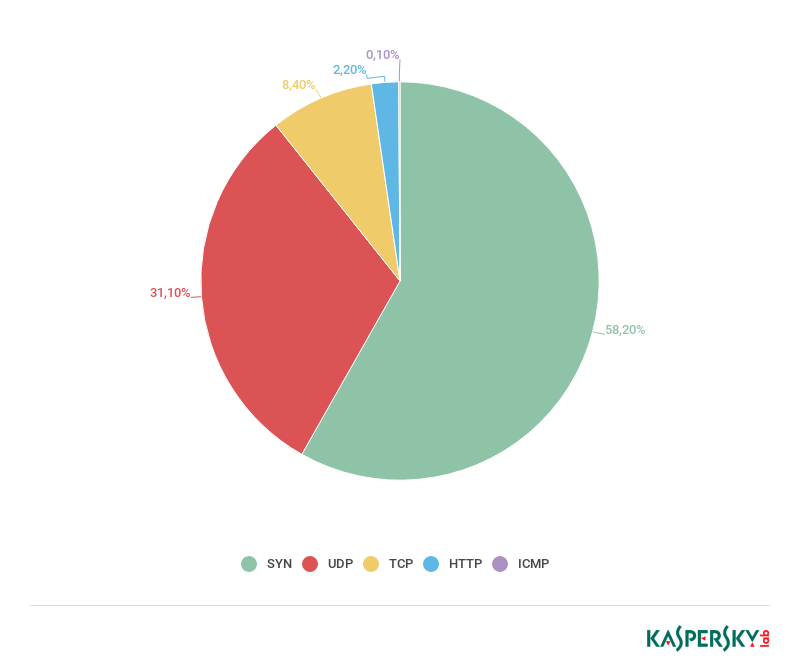
Distribution of DDoS attacks by type, Q4 2018
The ratio of Windows and Linux botnets barely moved against Q3. The share of Linux botnets increased slightly, up to 97.11%. Accordingly, the share of Windows botnets dropped by the same margin (1.25 p.p.) to 2.89%.
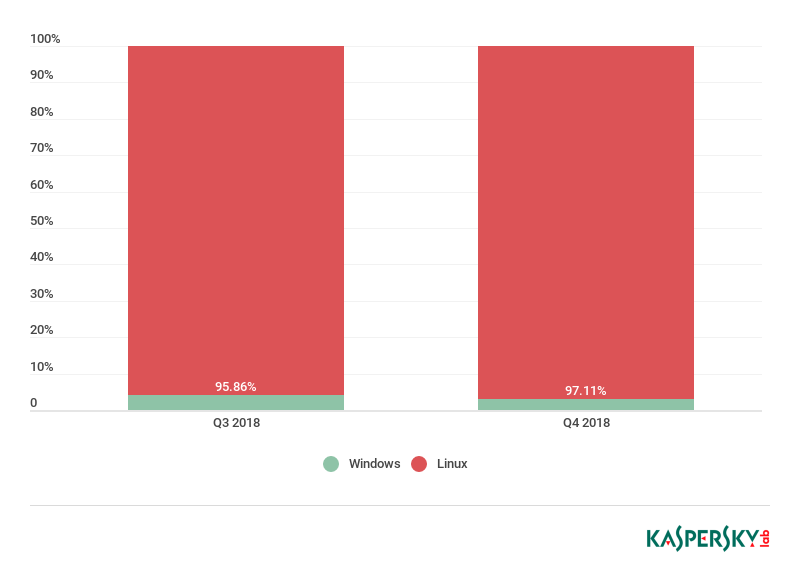
Ratio of Windows/Linux botnet attacks, Q3 and Q4 2018
Botnet distribution geography
The US remains out in front in terms of botnet C&C server hosting, even extending its lead from 37.31% to 43.48%. Slipping to seventh, Russia (4.08%) ceded second place to Britain (7.88%). Bronze went to the Netherlands, whose share increased from 2.24% to 6.79%. Significantly, all this growth is attributable to the rising number of Mirai C&C servers.
Italy and the Czech Republic vacated the Top 10 of botnet-rich countries, while Germany (5.43%) and Romania (3.26%) moved in. China (2.72%) continues to lose ground, clinging on to tenth position in Q4.
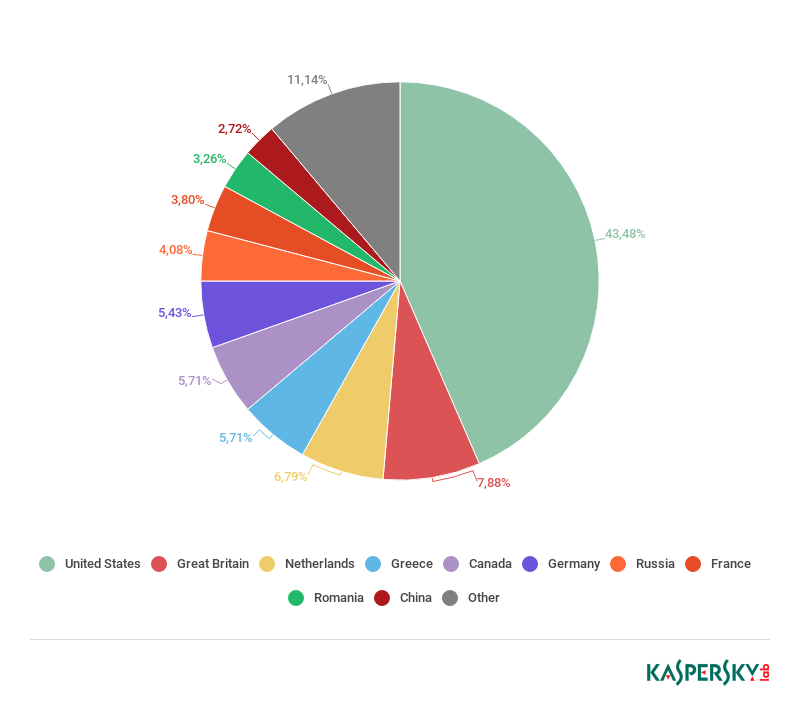
Distribution of botnet C&C servers by country, Q4 2018
Conclusion
For the third quarter in a row, the Top 10 ratings of countries by number of attacks, targets, and botnet C&C servers continue to fluctuate. Growth in DDoS activity is strongest where previously it was relatively low, while the once-dominant countries have seen a decline. This could well be the result of successful law enforcement and other initiatives to combat botnets. Another reason could be the emergence of better communications infrastructure in regions where DDoS attacks used to be infeasible.
If the trend continues, next quarter’s Top 10 will likely feature some more new entries, and in the long run, the shares of different countries could start to even out.
DDoS attacks in Q4 2018


















isabella bull
i like the way the graphs move
GDW
The breakdown of botnets by OS is fascinating. I would have thought it would be the inverse, and Windows machines were more easily able to infect to become zombies than Linux hosts. Are servers with higher bandwidth more targeted than Windows machines running on home connections? Or am I missing something obvious that could explain this?