
At the end of May, researchers from the nao_sec team reported a new zero-day vulnerability in Microsoft Support Diagnostic Tool (MSDT) that can be exploited using Microsoft Office documents. It allowed attackers to remotely execute code on Windows systems, while the victim could not even open the document containing the exploit, or open it in Protected Mode. The vulnerability, which the researchers dubbed Follina, later received the identifier CVE-2022-30190.
CVE-2022-30190 technical details
Briefly, the exploitation of the CVE-2022-30190 vulnerability can be described as follows. The attacker creates an MS Office document with a link to an external malicious OLE object (word/_rels/document.xml.rels), such as an HTML file located on a remote server. The data used to describe the link is placed in the
When opened, the attacker-created document runs MSDT. The attacker can then pass, through a set of parameters, any command to this tool for execution on the victim’s system with the privileges of the user who opened the document. What is more, the command can be passed even if the document is opened in Protected Mode and macros are disabled.
At the time of posting, two document formats were known to allow CVE-2022-30190 exploitation: Microsoft Word (.docx) and Rich Text Format (.rtf). The latter is more dangerous for the potential victim because it allows execution of a malicious command even without opening the document — just previewing it in Windows Explorer is enough.
Protecting against Follina
Kaspersky is aware of attempts to exploit the CVE-2022-30190 vulnerability through Microsoft Office documents. Our solutions protect against this using the Behavior Detection and Exploit Prevention tools.
The following verdict names are possible:
- PDM:Exploit.Win32.Generic
- HEUR:Exploit.MSOffice.Agent.n
- HEUR:Exploit.MSOffice.Agent.gen
- HEUR:Exploit.MSOffice.CVE-2017-0199.a
- HEUR:Exploit.MSOffice.CVE-2021-40444.a
- HEUR:Exploit.MSOffice.Generic
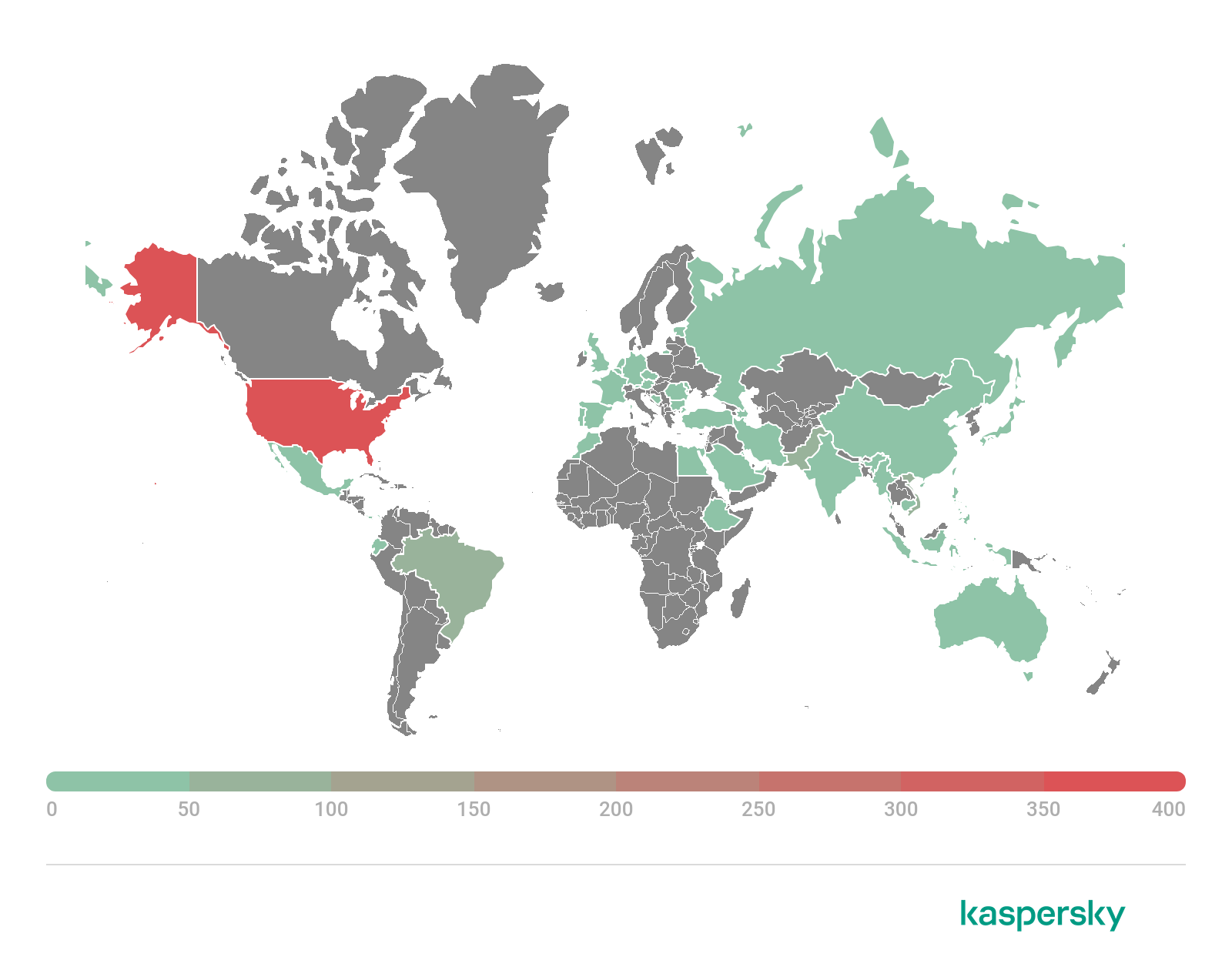
Geography of Follina exploitation attempts with Exploit.MSOffice.CVE-2021-40444.a verdict, May 1 – June 3, 2022 (download)
We expect to see more Follina exploitation attempts to gain access to corporate resources, including for ransomware attacks and data breaches. Therefore, we continue to closely monitor the situation and improve overall vulnerability detection. In addition, as part of the Managed Detection and Response service, our SOC experts can detect vulnerability exploitation, investigate attacks and provide clients with all necessary threat-related information.
To protect against Follina exploitation, we strongly advise that you follow Microsoft’s own guidelines: Guidance for CVE-2022-30190 Microsoft Support Diagnostic Tool Vulnerability. In particular, to prevent exploitation of this vulnerability, you can disable support for the MSDT URL protocol by taking these steps:
- Run Command Prompt as Administrator.
- To back up the registry key, execute the command “reg export HKEY_CLASSES_ROOTms-msdt filename”
- Execute the command “reg delete HKEY_CLASSES_ROOTms-msdt /f”.
CVE-2022-30190 (Follina) vulnerability in MSDT: description and counteraction




















BENJAMIN PACHECO
I understand the detriment these vulnerabilities pose, I do not understand the “basic” steps to preventing the intrusion. Is that left up to Kaspersky to assure, .. Or at the user level are their additional steps to be taken to assist in the effort?
Securelist
Hi Benjamin!
If you are Kaspersky customer, our solutions block attempts to exploit this vulnerability. To ensure that all necessary steps are taken to prevent exploitation, contact your local admin. If you are a home user and do not have other admins on your computer, you most likely do have admin privileges and can try to disable MSDT yourself.