
The features of malicious programs for mobile devices continue to expand: the first malicious program for mobile phones has been detected that steals logins and passwords for the Russian-language social networking site VKontakte.
Account credentials for various social networking sites are in high demand on the black market. That’s why criminals are trying to steal as many logins and passwords as possible using phishing pages and a variety of malicious programs. An example of this kind of malware is a new Trojan for mobile devices.
The malicious program Trojan-PSW.J2ME.Vkonpass.a is a 17 KB JAR archive called vkmob.jar which masks itself as an application for accessing the popular VKontakte site from a mobile phone.
If the application vkmobile (the name of the Trojan when installed on phones) is launched, the following will be displayed on the screen:
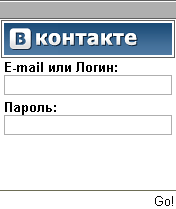
If the user enters his/her login and password and presses “Go!”, the Trojan will attempt to send the data via SMTP to the criminal’s e-mail. If the attempt is unsuccessful a “connection error” message is displayed; if the attempt is successful, “Error 401” appears on the screen.
Users need to be careful when using applications that pass themselves off as clients for various social networks, because in some cases those “clients” turn out to be malicious. Legitimate applications (if they exist) are usually available from the social networking sites themselves.





















Beware – that social network app for your phone may be a Trojan!