Having realized that users are getting wise to their scams involving unclaimed inheritances of multi-millionaire African princes, so-called Nigerian scammers have resorted to other outlandish stories from their arsenal of social engineering. We recently caught a few messages in our traps that suggest the scammers are not only unscrupulous and greedy but also engage in self-irony.
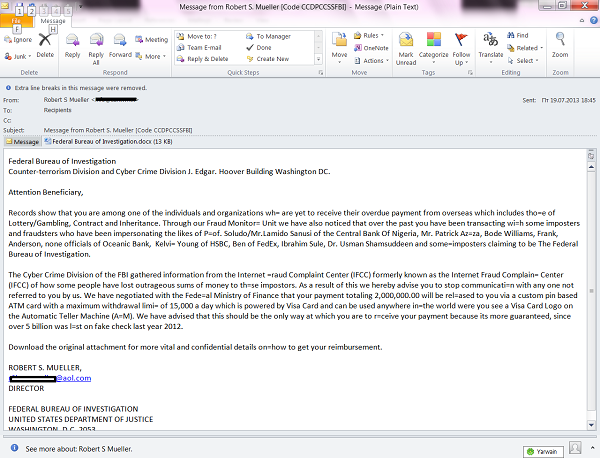
In particular, we detected some mailings supposedly sent by the FBI and its agents. The messages state that in the course of a large-scale investigation they identified users who had fallen victim to spammers, fake “Nigerian brides”, the organizers of non-existent lotteries, and bogus lawyers of deceased millionaires. The recipient of the “FBI” message was listed as a victim, and he/she could now receive compensation for any losses. The next step in the scam is most likely to be a request to send a payment to cover the costs of processing the compensation request, such as filling in all the necessary documentation. In other words, it uses the typical Nigerian scam scenario.
At the very least, this message should set the alarm bells ringing because the mailbox of these supposedly diligent fighters of cybercrime is hosted on a free, publicly available resource and not on an FBI server.
In another mailing the fraudsters go even further. This message is supposedly written by a Reverend Eugene who is writing on behalf of a Mr. Smith Walters, a repentant scammer who is on his deathbed in hospital. Eugene recounts the story of how Smith descended into a life of crime following his mother’s death and his need to look after his young sister. He started making money by sending out scam letters under numerous aliases, and when that didn’t pay enough he started selling drugs.
But the fraudster couldn’t enjoy the proceeds of his criminal life for long – a serious illness has apparently struck him down. With death approaching, Walters Smith decided to repent for his numerous sins, asking an intermediary to write to his victims asking for forgiveness and offering to return what he had supposedly stolen. Eugene asks any potential victims to contact him so they can receive part of Smith’s illegal legacy as a form of compensation. In the ensuing correspondence the “Reverend” is likely to ask for money to pay legal fees or to cover the costs of Smith’s medical care. After that, no more is likely to be heard from either of them.
As you can see, exposed or dying scammers cry, but they cry crocodile tears. And unsuspecting users can end up paying for those tears. So, whatever you do, don’t trust strangers who suddenly write with a tempting offer of millions!























Beware of Scammers’ Crocodile Tears!