
UPDATE 27.10.2017. Decryption opportunity assessment. File recovery possibility. Verdicts
What happened?
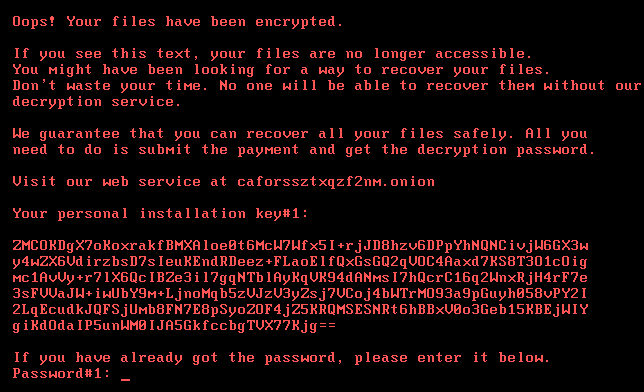
On October 24th we observed notifications of mass attacks with ransomware called Bad Rabbit. It has been targeting organizations and consumers, mostly in Russia but there have also been reports of victims in Ukraine. Here’s what a ransom message looks like for the unlucky victims:
What is Bad Rabbit?
Bad Rabbit is a previously unknown ransomware family.
How is Bad Rabbit distributed?
The ransomware dropper was distributed with the help of drive-by attacks. While the target is visiting a legitimate website, a malware dropper is being downloaded from the threat actor’s infrastructure. No exploits were used, so the victim would have to manually execute the malware dropper, which pretends to be an Adobe Flash installer. However, our analysis confirmed that Bad Rabbit uses the EternalRomance exploit as an infection vector to spread within corporate networks. The same exploit was used in the ExPetr.
We’ve detected a number of compromised websites, all of which were news or media websites.
Whom does it target?
Most of the targets are located in Russia. Similar but fewer attacks have also been seen in other countries – Ukraine, Turkey and Germany. Overall, there are almost 200 targets, according to the KSN statistics.
Since when does Kaspersky Lab detect the threat?
We have been proactively detecting the original vector attack since it began on the morning of October 24. The attack lasted until midday, although ongoing attacks were detected at 19.55 Moscow time. The server from which the Bad rabbit dropper was distributed went down in the evening (Moscow time).
How is it different to ExPetr? Or it is the same malware?
Our observations suggest that this been a targeted attack against corporate networks, using methods similar to those used during the ExPetr attack. What’s more, the code analysis showed a notable similarity between the code of ExPetr and Bad Rabbit binaries.
Technical details
According to our telemetry, the ransomware is spread via a drive-by attack.
The ransomware dropper is distributed from hxxp://1dnscontrol[.]com/flash_install.php
Also according to our telemetry data, victims are redirected to this malware web resource from legitimate news websites.
The downloaded file named install_flash_player.exe needs to be manually launched by the victim. To operate correctly, it needs elevated administrative privileges which it attempts to obtain using the standard UAC prompt. If started, it will save the malicious DLL as C:Windowsinfpub.dat and launch it using rundll32.
Pseudocode of the procedure that installs the malicious DLL
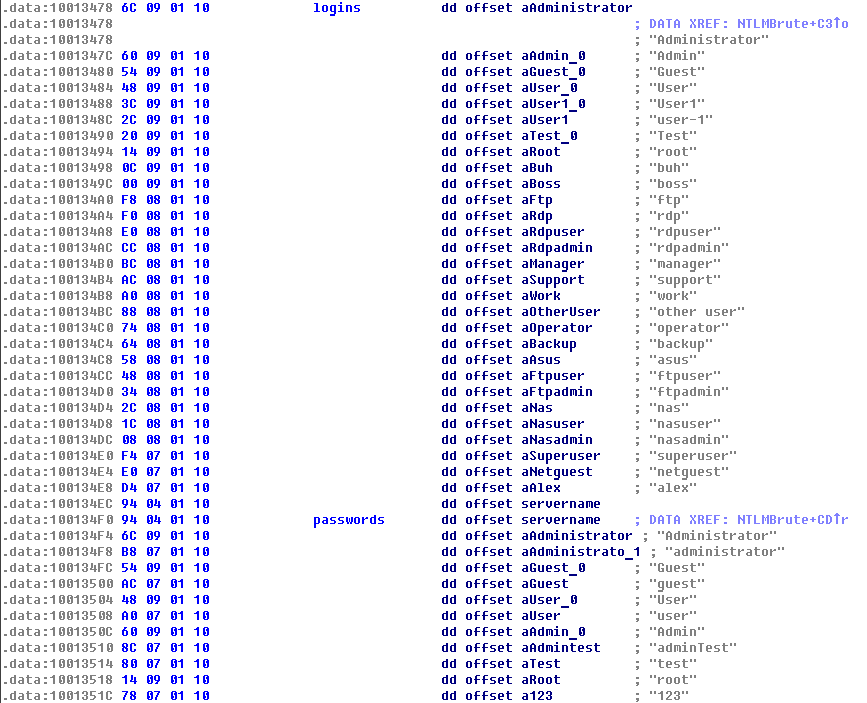
infpub.dat appears to be capable of brute-forcing NTLM login credentials to Windows machines that have pseudo-random IP addresses.
The hard-coded list of credentials
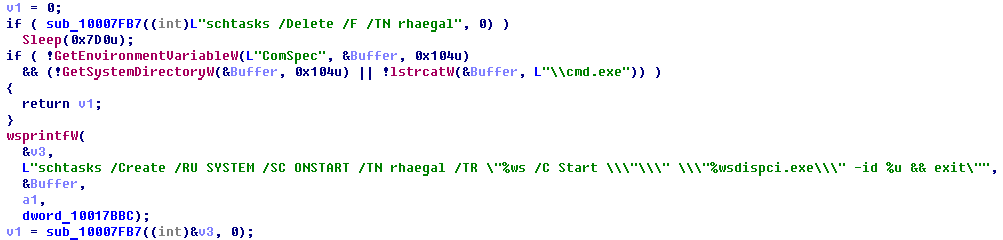
infpub.dat will also install the malicious executable dispci.exe into C:Windows and create a task to launch it.
Pseudocode of the procedure that creates the task which launches the malicious executable
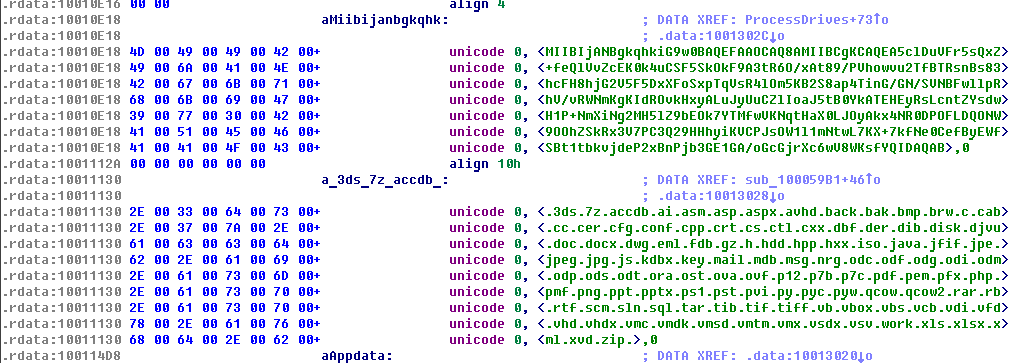
What’s more, infpub.dat acts as a typical file encrypting ransomware: it finds the victim’s data files using an embedded extension list and encrypts them using the criminal’s public RSA-2048 key.
The public key of the criminals and the extension list
The criminal’s public key parameters:
Public-Key: (2048 bit)
Modulus:
00:e5:c9:43:b9:51:6b:e6:c4:31:67:e7:de:42:55:
6f:65:c1:0a:d2:4e:2e:09:21:79:4a:43:a4:17:d0:
37:b5:1e:8e:ff:10:2d:f3:df:cf:56:1a:30:be:ed:
93:7c:14:d1:b2:70:6c:f3:78:5c:14:7f:21:8c:6d:
95:e4:5e:43:c5:71:68:4b:1a:53:a9:5b:11:e2:53:
a6:e4:a0:76:4b:c6:a9:e1:38:a7:1b:f1:8d:fd:25:
4d:04:5c:25:96:94:61:57:fb:d1:58:d9:8a:80:a2:
1d:44:eb:e4:1f:1c:80:2e:e2:72:52:e0:99:94:8a:
1a:27:9b:41:d1:89:00:4c:41:c4:c9:1b:0b:72:7b:
59:62:c7:70:1f:53:fe:36:65:e2:36:0d:8c:1f:99:
59:f5:b1:0e:93:b6:13:31:fc:15:28:da:ad:1d:a5:
f4:2c:93:b2:02:4c:78:35:1d:03:3c:e1:4b:0d:03:
8d:5b:d3:8e:85:94:a4:47:1d:d5:ec:f0:b7:43:6f:
47:1e:1c:a2:29:50:8f:26:c3:96:d6:5d:66:36:dc:
0b:ec:a5:fe:ee:47:cd:7b:40:9e:7c:1c:84:59:f4:
81:b7:5b:5b:92:f8:dd:78:fd:b1:06:73:e3:6f:71:
84:d4:60:3f:a0:67:06:8e:b5:dc:eb:05:7c:58:ab:
1f:61
Exponent: 65537 (0x10001)
The executable dispci.exe appears to be derived from the code base of the legitimate utility DiskCryptor. It acts as the disk encryption module which also installs the modified bootloader and prevents the normal boot-up process of the infected machine.
An interesting detail that we noticed when analyzing the sample of this threat: it looks like the criminals behind this malware are fans of the famous books & TV show series Game Of Thrones. Some of the strings used throughout the code are the names of different characters from this series.
Dragon names from Game Of Thrones
Character name from Game Of Thrones
Encryption scheme
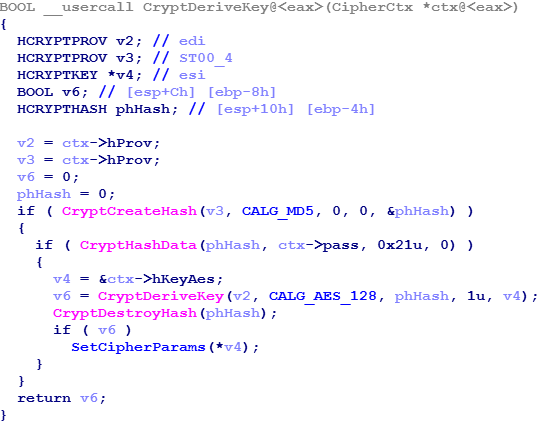
As we mentioned, the Bad Rabbit ransomware encrypts a victim’s files and disk. Files are encrypted with the following algorithms:
- AES-128-CBC
- RSA-2048
It is a default encryption scheme for ransomware.
An interesting fact is that the ransomware enumerates all running processes and compares the hashed name of each process with embedded hash values. It is important to mention that the hashing algorithm is similar to the ExPetr one.
The full list of embedded hashes of process names:
| Hash | Process name |
| 0x4A241C3E | dwwatcher.exe |
| 0x923CA517 | McTray.exe |
| 0x966D0415 | dwarkdaemon.exe |
| 0xAA331620 | dwservice.exe |
| 0xC8F10976 | mfevtps.exe |
| 0xE2517A14 | dwengine.exe |
| 0xE5A05A00 | mcshield.exe |
The partitions on the victim’s disks are encrypted with the help of the DiskCryptor driver dcrypt.sys (which is installed into C:Windowscscc.dat). The ransomware sends the necessary IOCTL codes to this driver. Some functions are taken as is from the sources of DiskCryptor (drv_ioctl.c), others seem to be implemented by the malware developers.
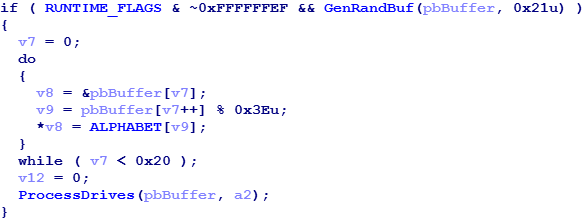
The disk partitions on the infected machine are encrypted by the DiskCryptor driver using the AES cipher in XTS mode. The password is generated by dispci.exe using the WinAPI function CryptGenRandom and has a length of 32 symbols.
Decryption opportunity assessment
Unlike ExPetr, the evidence suggests that Bad Rabbit is not intended as a wiper. Previously, in our article we wrote that the threat actors behind ExPetr were technically unable to decrypt MFT that was encrypted with the GoldenEye component. In the case of Bad Rabbit, however, the malware algorithm suggests that the threat actors have the technical means to decrypt the password necessary for disk decryption.
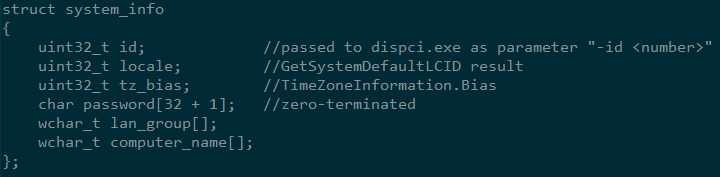
The data shown on the screen of an infected machine as “personal installation key#1” is an encrypted by RSA-2048 and base64-encoded binary structure that contains the following information gathered from the infected system:
The threat actors can use their own private RSA key to decrypt this structure. After decryption they can send this information to the victim.
Please note that, despite what it says in other vendors’ reports, the value of the id field which is passed to dispci.exe is just a 32-bit number used to distinguish different infected machines, and not the AES key which is used for disk encryption.
As part of our analysis, we extracted the password generated by the malware during a debugging session and attempted to enter this password when the system was locked after reboot. The password indeed worked and the boot-up process continued.
Unfortunately, we have to conclude that at this point there’s no way to decrypt disk and victim files without the threat actor’s RSA-2048 private key. The symmetric encryption keys are securely generated on the ransomware side which makes attempts to guess the keys unfeasible in practice.
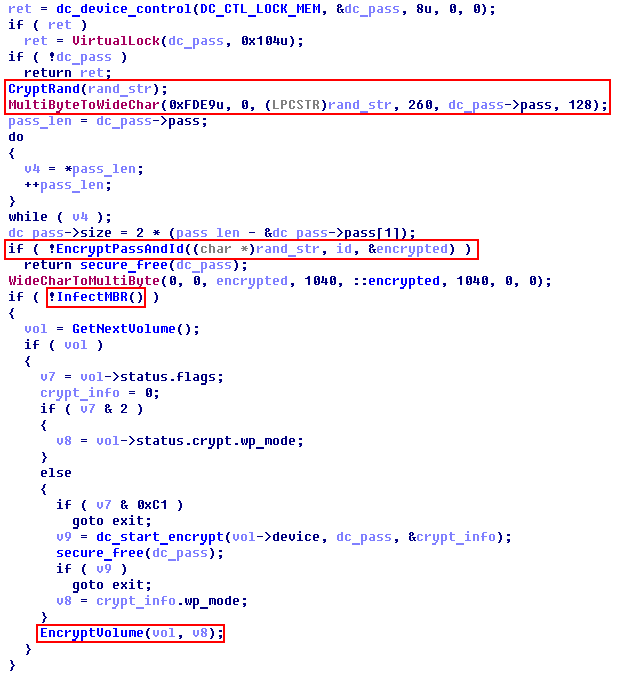
However, we found a flaw in the code of dispci.exe: the malware doesn’t wipe the generated password from the memory, which means that there is a slim chance to extract it before the dispci.exe process terminates. In the picture below, note that while the variable dc_pass (which will be passed to the driver) is securely erased after use, that’s not the case for the variable rand_str which holds the original copy of the password.
File encryption
As we wrote before, the trojan uses a common file encryption scheme. It generates a random 32-bytes-length string and uses it in the key derivation algorithm. Unfortunately, the trojan uses the CryptGenRandom function when generating this string.
The encrypted password, along with information about the infected system is written into Readme file as “personal installation key#2”.
An interesting fact is that the trojan cannot encrypt files which have a Read-only attribute.
File recovery possibility
We have discovered that Bad Rabbit does not delete shadow copies after encrypting the victim’s files. It means that if the shadow copies had been enabled prior to infection and if the full disk encryption did not occur for some reason, then the victim can restore the original versions of the encrypted files by the means of the standard Windows mechanism or 3rd-party utilities.
Recommendations
Kaspersky Lab corporate customers are also advised to:
- make sure that all protection mechanisms are activated as recommended; and that KSN and System Watcher components (which are enabled by default) are not disabled.
- update the antivirus databases immediately.
The abovementioned measures should be sufficient. However, as additional precautions we advise the following:
- restricting execution of files with the paths c:windowsinfpub.dat and C:Windowscscc.dat in Kaspersky Endpoint Security.
- configuring and enabling Default Deny mode in the Application Startup Control component of Kaspersky Endpoint Security to ensure and enforce proactive defense against this and other attacks.
Kaspersky Lab products detect this threat with the following verdicts:
- Trojan-Ransom.Win32.Gen.ftl
- Trojan-Ransom.Win32.BadRabbit
- DangerousObject.Multi.Generic
- PDM:Trojan.Win32.Generic
- Intrusion.Win.CVE-2017-0147.sa.leak
IOCs:
http://1dnscontrol[.]com/
fbbdc39af1139aebba4da004475e8839 – install_flash_player.exe
1d724f95c61f1055f0d02c2154bbccd3 – C:Windowsinfpub.dat
b14d8faf7f0cbcfad051cefe5f39645f – C:Windowsdispci.exe
Bad Rabbit ransomware






























just4u2know
Not sure,
perhaps legit
v4 = “please accept source –> http://www.themathpage.com/alg/negative-exponents-2.htm”
if v4 = accepted source
need to differ 0
else no random string
Kaspersky Lab experts are working on a detailed analysis of multibyte2wide to find possible flaws in its cryptographic routines.
sorry for nag
Fola Bolodeoku
As part of the full list of embedded hashes of process names, I see three McAfee Endpoint Security 10.x processes (0xE5A05A00 mcshield.exe {McAfee Scanner Service}; 0xC8F10976 mfevtps.exe {McAfee Process Validation Service}; 0x923CA517 McTray.exe {McTray Application}), kindly clarify what role they play Runtime flags initialization routine.
FRBA
Ok
Chris
Normally, WMI is subject to UAC-filtering. Is BadRabbit able to spread to another machine when it’s run by a local administrator (not domain user or local “administrator”)?
jays
How can i see the code like that? Use what apps? I want learn to know how analysis file