
There is no secret that cybercriminals try to intimidate users very often in order to infect their machines. We’ve seen a lot of examples of cybercriminals using black SEO for redirecting users to web pages which emulate AV scanning. And there is no surprise that the results of such ‘scanning’ show that the user’s machine is infected with a lot of dangerous malicious apps and it is very essential to download and install a brand new ‘antivirus program’ which is actually fake AV.
But what about smartphones and mobile phones? Cybercriminals have started to use almost the same techniques in order to force users to download and install malware. But in this case we talk about SMS Trojans with fake AV rudiments. Here are some details.
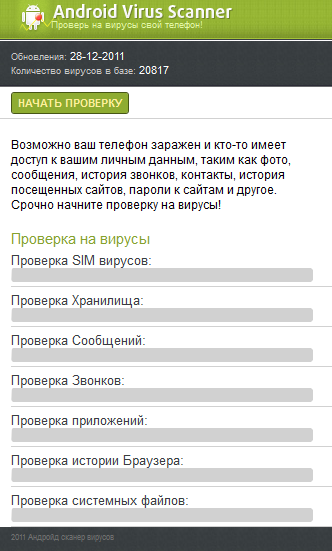
When looking for some popular mobile apps (e.g. Opera Mini) in Google via a smartphone, several search results will redirect users to a web page which may look like this:
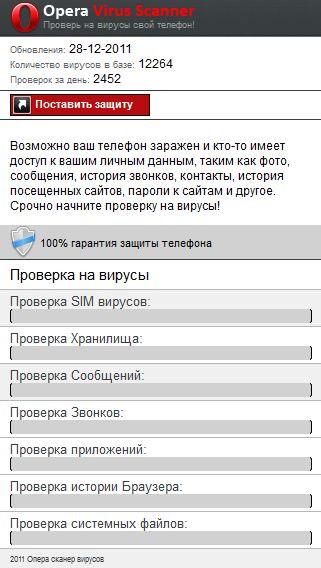
Or this:
Both web pages claim that the user’s device might be infected and that somebody has access to personal data and then will ask the user to check his or her device for malware. If the user clicks on the button, the web page will emulate device scanning with the following ‘hard-coded’ results:
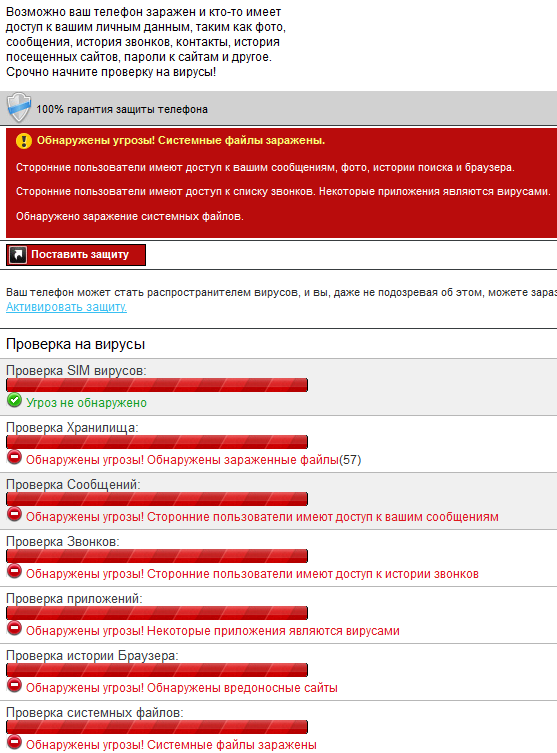
Or:
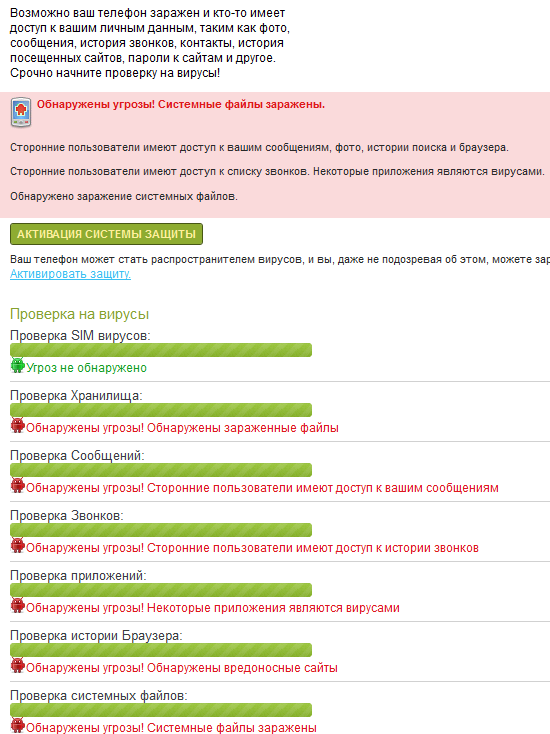
This web page never ‘finds’ malware on a SIM card but messages, calls, apps, browser history, storage and system files have threats, malware and are remotely accessible. Surely it’s fake but it still it might frighten a user and force him to click on the link to ‘activate security system’.
If a user clicks on the link he will be asked to download and install ‘VirusScanner.apk’ file which is actually malicious and detected by us as Trojan-SMS.AndroidOS.Scavir. And yes, in the case of a non-Android device the user will be asked to download ‘VirusScanner.jar’: a file which is detected by us as Trojan-SMS.J2ME.Agent.ij.
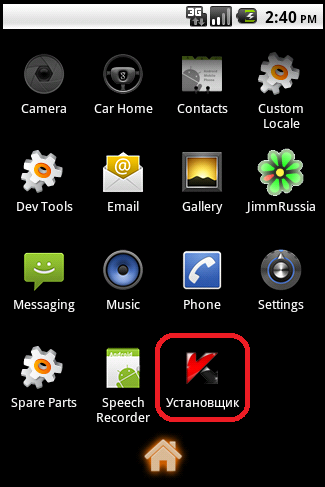
After the installation, an application named ‘Установщик’ (‘Installer’) with the Kaspersky icon appears in the menu:
I’ve mentioned earlier some ‘fake AV rudiments’. The picture below can explain what exactly these rudiments are. That’s what user will see after launching the Scavir malware:
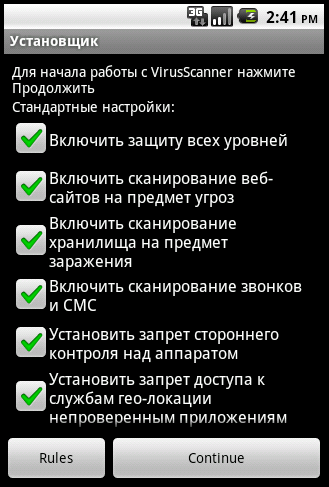
The user is asked to press the ‘Continue’ button if he wants to launch VirusScanner with some options like ‘Turn on multi-level protection’, ‘Disable remote control of a device’ or ‘Turn on web site scanning’. But in fact after pressing ‘Continue’ this app will send SMS messages to expensive premium rate numbers.
It’s not the first time when we’ve seen the adoption of common malware techniques in the mobile malware world. And we will definitely see more examples of such adoption in 2012.





















Android malware: new traps for users