
Keyloggers: Implementing keyloggers in Windows. Part Two
In February 2005, Joe Lopez, a businessman from Florida, filed a suit against Bank of America after unknown hackers stole $90,000 from his Bank of America account. The money had been transferred to Latvia.
An investigation showed that Mr. Lopez’s computer was infected with a malicious program, Backdoor.Coreflood, which records every keystroke and sends this information to malicious users via the Internet. This is how the hackers got hold of Joe Lopez’s user name and password, since Mr. Lopez often used the Internet to manage his Bank of America account.
However the court did not rule in favor of the plaintiff, saying that Mr. Lopez had neglected to take basic precautions when managing his bank account on the Internet: a signature for the malicious code that was found on his system had been added to nearly all antivirus product databases back in 2003.
Joe Lopez’s losses were caused by a combination of overall carelessness and an ordinary keylogging program.
About Keyloggers
The term ‘keylogger’ itself is neutral, and the word describes the program’s function. Most sources define a keylogger as a software program designed to secretly monitor and log all keystrokes. This definition is not altogether correct, since a keylogger doesn’t have to be software – it can also be a device. Keylogging devices are much rarer than keylogging software, but it is important to keep their existence in mind when thinking about information security.
Legitimate programs may have a keylogging function which can be used to call certain program functions using “hotkeys,” or to toggle between keyboard layouts (e.g. Keyboard Ninja). There is a lot of legitimate software which is designed to allow administrators to track what employees do throughout the day, or to allow users to track the activity of third parties on their computers. However, the ethical boundary between justified monitoring and espionage is a fine line. Legitimate software is often used deliberately to steal confidential user information such as passwords.
Most modern keyloggers are considered to be legitimate software or hardware and are sold on the open market. Developers and vendors offer a long list of cases in which it would be legal and appropriate to use keyloggers, including:
- Parental control: parents can track what their children do on the Internet, and can opt to be notified if there are any attempts to access websites containing adult or otherwise inappropriate content;
- Jealous spouses or partners can use a keylogger to track the actions of their better half on the Internet if they suspect them of “virtual cheating”;
- Company security: tracking the use of computers for non-work-related purposes, or the use of workstations after hours;
- Company security: using keyloggers to track the input of key words and phrases associated with commercial information which could damage the company (materially or otherwise) if disclosed;
- Other security (e.g. law enforcement): using keylogger records to analyze and track incidents linked to the use of personal computers;
- Other reasons.
However, the justifications listed above are more subjective than objective; the situations can all be resolved using other methods. Additionally, any legitimate keylogging program can still be used with malicious or criminal intent. Today, keyloggers are mainly used to steal user data relating to various online payment systems, and virus writers are constantly writing new keylogger Trojans for this very purpose.
Furthermore, many keyloggers hide themselves in the system (i.e. they have rootkit functionality), which makes them fully-fledged Trojan programs.
As such programs are extensively used by cyber criminals, detecting them is a priority for antivirus companies. Kaspersky Lab’s malware classification system has a dedicated category for malicious programs with keylogging functionality: Trojan-Spy. Trojan-Spy programs, as the name suggests, track user activity, save the information to the user’s hard disk and then forward it to the author or ‘master’ of the Trojan. The information collected includes keystrokes and screen-shots, used in the theft of banking data to support online fraud.
Why keyloggers are a threat
Unlike other types of malicious program, keyloggers present no threat to the system itself. Nevertheless, they can pose a serious threat to users, as they can be used to intercept passwords and other confidential information entered via the keyboard. As a result, cyber criminals can get PIN codes and account numbers for e-payment systems, passwords to online gaming accounts, email addresses, user names, email passwords etc.
Once a cyber criminal has got hold of confidential user data, s/he can easily transfer money from the user’s account or access the user’s online gaming account. Unfortunately access to confidential data can sometimes have consequences which are far more serious than an individual’s loss of a few dollars. Keyloggers can be used as tools in both industrial and political espionage, accessing data which may include proprietary commercial information and classified government material which could compromise the security of commercial and state-owned organizations (for example, by stealing private encryption keys).
Keyloggers, phishing and social engineering (see ‘Computers, Networks and Theft’) are currently the main methods being used in cyber fraud. Users who are aware of security issues can easily protect themselves against phishing by ignoring phishing emails and by not entering any personal information on suspicious websites. It is more difficult, however, for users to combat keyloggers; the only possible method is to use an appropriate security solution, as it’s usually impossible for a user to tell that a keylogger has been installed on his/ her machine.
According to Cristine Hoepers, the manager of Brazil’s Computer Emergency Response Team, which works under the aegis of the country’s Internet Steering Committee, keyloggers have pushed phishing out of first place as the most-used method in the theft of confidential information. What’s more, keyloggers are becoming more sophisticated – they track websites visited by the user and only log keystrokes entered on websites of particular interest to the cyber criminal.
In recent years, we have seen a considerable increase in the number of different kinds of malicious programs which have keylogging functionality. No Internet user is immune to cyber criminals, no matter where in the world s/he is located and no matter what organization s/he works for.
How cyber criminals use keyloggers
One of the most publicized keylogging incidents recently was the theft of over $1million from client accounts at the major Scandinavian bank Nordea. In August 2006 Nordea clients started to receive emails, allegedly from the bank, suggesting that they install an antispam product, which was supposedly attached to the message. When a user opened the file and downloaded it to his/ her computer, the machine would be infected with a well known Trojan called Haxdoor. This would be activated when the victim registered at Nordea’s online service, and the Trojan would display an error notification with a request to re-enter the registration information. The keylogger incorporated in the Trojan would record data entered by the bank’s clients, and later send this data to the cyber criminals’ server. This was how cyber criminals were able to access client accounts, and transfer money from them. According to Haxdoor’s author, the Trojan has also been used in attacks against Australian banks and many others.
On January 24, 2004 the notorious Mydoom worm caused a major epidemic. MyDoom broke the record previously set by Sobig, provoking the largest epidemic in Internet history to date. The worm used social engineering methods and organized a DoS attack on www.sco.com; the site was either unreachable or unstable for several months as a consequence. The worm left a Trojan on infected computers which was subsequently used to infect the victim machines with new modifications of the worm. The fact that MyDoom had a keylogging function to harvest credit card numbers was not widely publicized in the media.
In early 2005 the London police prevented a serious attempt to steal banking data. After attacking a banking system, the cyber criminals had planned to steal $423 million from Sumitomo Mitsui’s London-based offices. The main component of the Trojan used, which was created by the 32-year-old Yeron Bolondi, was a keylogger that allowed the criminals to track all the keystrokes entered when victims used the bank’s client interface.
In May 2005 a married couple was arrested in London who were charged with developing malicious programs that were used by some Israeli companies in industrial espionage. The scale of the espionage was shocking: the companies named by the Israeli authorities in investigative reports included cellular providers like Cellcom and Pelephone, and satellite television provider YES. According to reports, the Trojan was used to access information relating to the PR agency Rani Rahav, whose clients included Partner Communications (Israel’s second leading cellular services provider) and the HOT cable television group. The Mayer company, which imports Volvo and Honda cars to Israel, was suspected of committing industrial espionage against Champion Motors, which imports Audi and Volkswagen cars to the country. Ruth Brier-Haephrati, who sold the keylogging Trojan that her husband Michael Haephrati created, was sentenced to four years in jail, and Michael received a two-year sentence.
In February 2006, the Brazilian police arrested 55 people involved in spreading malicious programs which were used to steal user information and passwords to banking systems. The keyloggers were activated when the users visited their banks’ websites, and secretly tracked and subsequently sent all data entered on these pages to cyber criminals. The total amount of money stolen from 200 client accounts at six of the country’s banks totaled $4.7million.
At approximately the same time, a similar criminal grouping made up of young (20 – 30 year old) Russians and Ukrainians was arrested. In late 2004, the group began sending banking clients in France and a number of other countries email messages that contained a malicious program – namely, a keylogger. Furthermore, these spy programs were placed on specially created websites; users were lured to these sites using classic social engineering methods. In the same way as in the cases described above, the program was activated when users visited their banks’ websites, and the keylogger harvested all the information entered by the user and sent it to the cyber criminals. In the course of eleven months over one million dollars was stolen.
There are many more examples of cyber criminals using keyloggers – most financial cybercrime is committed using keyloggers, since these programs are the most comprehensive and reliable tool for tracking electronic information.
Increased use of keyloggers by cyber criminals
The fact that cyber criminals choose to use keyloggers time and again is confirmed by IT security companies.
One of VeriSign’s recent reports notes that in recent years, the company has seen a rapid growth in the number of malicious programs that have keylogging functionality.
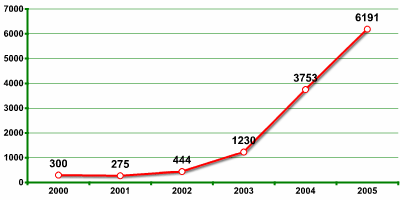
Source: iDefense, a VeriSign Company
One report issued by Symantec shows that almost 50% of malicious programs detected by the company’s analysts during the past year do not pose a direct threat to computers, but instead are used by cyber criminals to harvest personal user data.
According to research conducted by John Bambenek, an analyst at the SANS Institute, approximately 10 million computers in the US alone are currently infected with a malicious program which has a keylogging function. Using these figures, together with the total number of American users of e-payment systems, possible losses are estimated to be $24.3 million.
Kaspersky Lab is constantly detecting new malicious programs which have a keylogging function. One of the first virus alerts on securelist.com, Kaspersky Lab’s dedicated malware information site, was published on 15th June 2001. The warning related to TROJ_LATINUS.SVR, a Trojan with a keylogging function. Since then, there has been a steady stream of new keyloggers and new modifications. Kaspersky antivirus database currently contain records for more than 300 families of keyloggers. This number does not include keyloggers that are part of complex threats (i.e. in which the spy component provides additional functionality).
Most modern malicious programs are hybrids which implement many different technologies. Due to this, any category of malicious program may include programs with keylogger (sub)functionality. The number of spy programs detected by Kaspersky Lab each month is on the increase, and most of these programs use keylogging technology.
Keylogger construction
The main idea behind keyloggers is to get in between any two links in the chain of events between when a key is pressed and when information about that keystroke is displayed on the monitor. This can be achieved using video surveillance, a hardware bug in the keyboard, wiring or the computer itself, intercepting input/ output, substituting the keyboard driver, the filter driver in the keyboard stack, intercepting kernel functions by any means possible (substituting addresses in system tables, splicing function code, etc.), intercepting DLL functions in user mode, and, finally, requesting information from the keyboard using standard documented methods.
Experience shows that the more complex the approach, the less likely it is to be used in common Trojan programs and the more likely it is to be used in specially designed Trojan programs which are designed to steal financial data from a specific company.
Keyloggers can be divided into two categories: keylogging devices and keylogging software. Keyloggers which fall into the first category are usually small devices that can be fixed to the keyboard, or placed within a cable or the computer itself. The keylogging software category is made up of dedicated programs designed to track and log keystrokes.
The most common methods used to construct keylogging software are as follows:
- a system hook which intercepts notification that a key has been pressed (installed using WinAPI SetWindowsHook for messages sent by the window procedure. It is most often written in C);
- a cyclical information keyboard request from the keyboard (using WinAPI Get(Async)KeyState or GetKeyboardState – most often written in Visual Basic, sometimes in Borland Delphi);
- using a filter driver (requires specialized knowledge and is written in C).
We will provide a detailed explanation of the different ways keyloggers are constructed in the second half of this article (to be published in the near future). But first, here are some statistics.
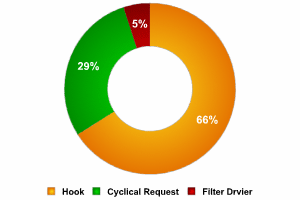
A rough breakdown of the different types of keyloggers is shown in the pie chart below:
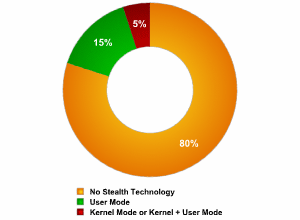
Recently, keyloggers that disguise their files to keep them from being found manually or by an antivirus program have become more numerous. These stealth techniques are called rootkit technologies. There are two main rootkit technologies used by keyloggers:
- masking in user mode;
- masking in kernel mode.
A rough breakdown of the techniques used by keyloggers to mask their activity is shown in the pie chart below:
How keyloggers spread
Keyloggers spread in much the same way that other malicious programs spread. Excluding cases where keyloggers are purchased and installed by a jealous spouse or partner, and the use of keyloggers by security services, keyloggers are mostly spread using the following methods):
- a keylogger can be installed when a user opens a file attached to an email;
- a keylogger can be installed when a file is launched from an open-access directory on a P2P network;
- a keylogger can be installed via a web page script which exploits a browser vulnerability. The program will automatically be launched when a user visits a infected site;
- a keylogger can be installed by another malicious program already present on the victim machine, if the program is capable of downloading and installing other malware to the system.
How to protect yourself from keyloggers
Most antivirus companies have already added known keyloggers to their databases, making protecting against keyloggers no different from protecting against other types of malicious program: install an antivirus product and keep its database up to date. However, since most antivirus products classify keyloggers as potentially malicious, or potentially undesirable programs, users should ensure that their antivirus product will, with default settings, detect this type of malware. If not, then the product should be configured accordingly, to ensure protection against most common keyloggers.
Let’s take a closer look at the methods that can be used to protect against unknown keyloggers or a keylogger designed to target a specific system.
Since the chief purpose of keyloggers is to get confidential data (bank card numbers, passwords, etc.), the most logical ways to protect against unknown keyloggers are as follows:
- using one-time passwords or two-step authentication,
- using a system with proactive protection designed to detect keylogging software,
- using a virtual keyboard.
Using a one-time password can help minimize losses if the password you enter is intercepted, as the password generated can be used one time only, and the period of time during which the password can be used is limited. Even if a one-time password is intercepted, a cyber criminal will not be able to use it in order to obtain access to confidential information.
In order to get one-time passwords, you can use a special device such as:
- a USB key (such as Aladdin eToken NG OTP (page in Russian)):

- a ‘calculator’ (such as RSA SecurID 900 Signing Token):

In order to generate one-time passwords, you can also use mobile phone text messaging systems that are registered with the banking system and receive a PIN-code as a reply. The PIN is then used together with the personal code for authentication.
If either of the above devices is used to generate passwords, the procedure is as described below:
- the user connects to the Internet and opens a dialogue box where personal data should be entered;
- the user then presses a button on the device to generate a one-time password, and a password will appear on the device’s LCD display for 15 seconds;
- the user enters his user name, personal PIN code and the generated one-time password in the dialogue box (usually the PIN code and the key are entered one after the other in a single pass code field);
- the codes that are entered are verified by the server, and a decision is made whether or not the user may access confidential data.
When using a calculator device to generate a password, the user will enter his PIN code on the device ‘keyboard’ and press the “>” button.
One-time password generators are widely used by banking systems in Europe, Asia, the US and Australia. For example, Lloyds TSB, a leading bank, decided to use password generators back in November 2005.
In this case, however, the company has to spend a considerable amount of money as it had to acquire and distribute password generators to its clients, and develop/ purchase the accompanying software.
A more cost efficient solution is proactive protection on the client side, which can warn a user if an attempt is made to install or activate keylogging software.
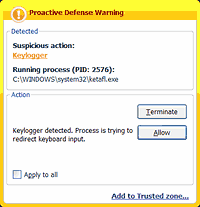
Proactive protection against keyloggers in
Kaspersky Internet Security
The main drawback of this method is that the user is actively involved and has to decide what action should be taken. If a user is not very technically experienced, s/he might make the wrong decision, resulting in a keylogger being allowed to bypass the antivirus solution. However, if developers minimize user involvement, then keyloggers will be able to evade detection due to an insufficiently rigorous security policy. However, if settings are too stringent, then other, useful programs which contain legitimate keylogging functions might also be blocked.
The final method which can be used to protect against both keylogging software and hardware is using a virtual keyboard. A virtual keyboard is a program that shows a keyboard on the screen, and the keys can be ‘pressed’ by using a mouse.
The idea of an on-screen keyboard is nothing new – the Windows operating system has a built-in on-screen keyboard that can be launched as follows: Start > Programs > Accessories > Accessibility > On-Screen Keyboard.
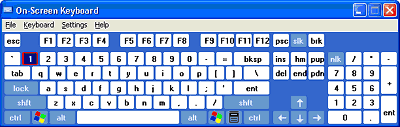
An example of the Windows on-screen keyboard
However, on-screen keyboards aren’t a very popular method of outsmarting keyloggers. They were not designed to protect against cyber threats, but as an accessibility tool for disabled users. Information entered using an on-screen keyboard can easily be intercepted by a malicious program. In order to be used to protect against keyloggers, on-screen keyboards have to be specially designed in order to ensure that information entered or transmitted via the on-screen keyboard cannot be intercepted.
Conclusions
This article has provided an overview of how keyloggers – both keylogging software and hardware – function and are used.
- Even though keylogger developers market their products as legitimate software, most keyloggers can be used to steal personal user data and in political and industrial espionage.
- At present, keyloggers – together with phishing and social engineering methods – are one of the most commonly used methods of cyber fraud.
- IT security companies have recorded a steady increase in the number of malicious programs that have keylogging functionality.
- Reports show that there is an increased tendency to use rootkit technologies in keylogging software, to help the keylogger evade manual detection and detection by antivirus solutions.
- Only dedicated protection can detect that a keylogger is being used for spy purposes.
- The following measures can be taken to protect against keyloggers:
- use a standard antivirus that can be adjusted to detect potentially malicious software (default settings for many products);
- proactive protection will protect the system against new ,modifications of existing keyloggers;
- use a virtual keyboard or a system to generate one-time passwords to protect against keylogging software and hardware.
Keyloggers: How they work and how to detect them (Part 1)



















yahoo
My partner and I stumbled over here by a different web address and thought I might as well check things out.
I like what I see so i am just following you. Look forward to
looking over your web page for a second time.
Ernest Racy
I am a wired Ethernet connection and recently, by mistake, and somehow got a wireless connection instead. I live in a small apartment building, saw various connections, and one of them was “FBI_Investigation_2.4”. Am I being investigated or is this some kind of malware? Can the government software be detected on my laptop?
nakedsoul
I don’t think that the FBI would really announce them selves in that manner but hey who is to say that they don’t do it to scare ppl either
The question is should u take caution and the answer is yes.
Isybee
I’ve used a similar name for my wireless access point, “FBI Van3”. I did it to be funny and maybe to keep would be hackers from hacking.
Lea Richard
I was hacked in 2014, they filed my taxes, but not needing $ right away, I chose to wait and let them do there job. After that, I named my routers in this lil town of crazy drug addictions in southwest La. I decided to do what my son in law had done. So main router, FBI SURVIELANCE VAN, notice spelling, lol 2nd TASK FORCE ONE, 3rd TASK FORSE TOO, again, spelling. I moved to a trailer park, bought trailer, and lots of dealers AT FIRST!!!!! But no computers, just their lil phones, lol so it can indeed serve some good, Not haten on all drugs but whatever this crap they do these daze is it is nothing like da old daze and I for one enjoy for once, not being robbed blind constantly. At least in da old daze, you were expected to be able to afford anything you did too much of, and dats still my rule, so to speak. Now I help catch scammers and love it. ALWAYS CHECK BEFORE YOU BUY!!! AND ALWAYS, HAVE A GOOD ONE AND LET NOONE, SCREW IT UP!!!!
CharlieDavis
It’s a ‘silly’ connection name; The real police wouldn’t be obvious at all. They would call theirs something innocent-sounding like “Mary’s Mac” or “Smith Family”. Relax.
Donalds Mac
LOL
Cody
“Legitimate programs may have a keylogging function which can be used to call certain program functions using “hotkeys,” or to toggle between keyboard layouts (e.g. Keyboard Ninja).”
That is not a keylogger itself but instead how a keylogger (well, in general – interrupt, handlers, …) would know a key is pressed (and which one). If that were keylogging then you could argue that pretty much everything software does that involves any interrupt (or has an interrupt service routine) is then a logger. The keyword is logger. Loggers by themselves are legitimate; keyloggers are not. Is this really Kaspersky? …
“There is a lot of legitimate software which is designed to allow administrators to track what employees do throughout the day, or to allow users to track the activity of third parties on their computers. However, the ethical boundary between justified monitoring and espionage is a fine line. Legitimate software is often used deliberately to steal confidential user information such as passwords.”
Maybe you don’t mean it this way but I’m going to include my initial reaction (besides, it should be clarified anyway since logging is a good thing):
Excuse me? If I grant someone access to my server I can do whatever the …. I want to with their account that I CREATED. They don’t own the server; I DO. And not logging would be stupid. A user of their own computer, server, or whatever else, is not spying if they monitor something on their computer (or whatever), never. That is absurd and a blatant misuse of words for a rather serious issue. Not only that, let’s say a public system for file sharing (say an ftp server) wasn’t monitored and then there was illegal content on the server that was discovered by (or reported to) authorities? Guess who is legally responsible? That’s correct.
Equally, if I am granted access to someone’s computer, THEY can (and should) monitor me. The only time it is not fine is when you are not authorised to do this, which would mean you don’t really care about the law or morals, anyway.
“Jealous spouses or partners can use a keylogger to track the actions of their better half on the Internet if they suspect them of “virtual cheating”; ”
That’s appropriate use, is it? Not only is it not honest, not only is it showing neediness/not trusting, it isn’t really appropriate and certainly not ethical (and depending on who owns the computer there are potentially other issues). It is one thing if you monitor a spouse’s activity on your own computer, in general, but another when you are only monitoring one thing only. If you were to reverse the roles, do you think you would find it appropriate still? Even I know this and I am close to socially inept. I’ll also point out the irony. You suggest “However, the ethical boundary between justified monitoring and espionage is a fine line.” and yet … are these not really the same thing? The monitoring one thing is certainly not justified. Of course, I would argue it isn’t spying, either, but I know what you mean by espionage.
“Furthermore, many keyloggers hide themselves in the system (i.e. they have rootkit functionality), which makes them fully-fledged Trojan programs.”
Interesting definitions there. If the supposed trojan horse is by itself and nothing else, it really isn’t a trojan horse, is it? No, because then it isn’t pretending to do be one thing while it is now doing something (unknown to the user) on the system. And even more odd is the way it comes across as to how you define rootkit functionality. I’ll let that slide… On the other hand, of course a keylogger isn’t going to announce itself, intentionally. Guess why that is? Correct, because it isn’t wanted (most certainly if not placed by the owner).
Shantala
My rejected stalker has installed a keylogger on all my devices, could also be a botnet. He’s been forwarding the keylogger output to emails of media and press.
brighteyerish
Shantala – I’m disappointed that all of the genius that access this thread did not have a response for you. I know just about null when it comes to much above user tasks but I am found also in your situation and how quickly one can learn (or become confused) when you see that you are being violated in very serious way. what’s worse is that law enforcement is not going to look at this personal attack as something worth their time in follow-up.
If you would like to share updates I can be found on Google+ with the same name. Fierce wishes to you and may these ill wired male-bots be served their slice of karma-kake sooner rather than later.
Cody
NoScript blocked (it seems) my original post because of the captcha. So let me try this again:
—
You know brighteyerish… (incidentally, clever name!) I never thought of the post as a question so much as a statement. It probably is because I have been fairly absent minded. Indeed abuse is neglected and I experienced this for many years in my life and I stand up against it wherever I can as long as I can.
Consider this response to you and also Shantala.
You need to then clean your system up; there are many ways and I obviously can’t suggest any specific products because a) I’m actually on an anti-malware corporation’s website and b) I don’t use Windows (or MacOS X). True I know some AVs I like and use but I think there are fine lines here.
Do your backup your system? If not once you clean it up make sure you backup regularly. That means every day (most certainly every day your computer is on). The backups need to be secure, too. This isn’t a simple concept so I’ll not go there except to bring it up.
Are you sure it is a stalker that you rejected? It doesn’t necessarily matter who it is except that if you can get a restraining order it would be of use (this isn’t to say that it will be resolved – stalkers can be very good at working around this type of thing). But bottom line is you need to clean your systems and you need to then properly protect them and that includes following safe computer practises. This I cannot help you with directly for I don’t know your set up but I will remind you that any device that is connected to another whether indirectly or not, whether wired or wireless, is at potential risk of being infected with the same problems.
Good luck on this matter; abuse is unfortunately a huge problem in this world and arguably it is the most severe problem in the world when it comes to mankind. I would say definitely the latter and I know this first hand (but not because of e.g. rejection but something for many many years which has affected my life adversely – and in a way that cannot completely be repaired).
Angie
I was on twitter and I hit a link and my system started screaming telling me someone got in to my computer. Although I unplugged everthing within a 10 seconds, it seems now I get the blue screen with—
: ( Your PC ran into a problem and needs to restart. We’re just collecting some error info, and then we’ll restart for you. (100% Complete) If you like to know more, You can serch online for this error: IRQL NOT LESS THAN EQUAL.
Friendly anon
Was the warning in the browser? If yes, don’t worry it likely was a scam to get you to call the number on screen, a website can’t execute a file on your computer without your permission, unless there already was a malicious program. The bluescreen was likely caused by you forcefully shutting windows down by pulling the plug.
David Perry
Hello,
I thoroughly enjoyed reading this article and would like to be on the SECURELIST for future posts.
Thank you in advance.
Jed A Mills
I enjoyed this article very much. This computer is keylogged. I think by legal opponents. My email has also been hacked for many years by the same group. I recently made my email only accessible from this IP address and changed the password afterwords. But they got it, so I assume it is a keylogger.
My cell phone was also hacked. I replaced it with a new phone. When data was transferred to the new device I instantly, while the sales clerk was transferring data, got notices from google that both my email accounts had just been hacked. (I had also changed the passwords when I bought the new phone). About a week before trial was supposed to occur, my phone called my lawyer at his home at night. I also have been on my email talking to my bank when the bank emailed me a note with the subject of ‘fraud’. Before I could open it a cursor went to it and moved it off screen. I could not find it in deleted or sent items.
What can I do? Are the new anti malware programs effective against sophisticated hackers? I will use the virtual keyboard for new bank and email passwords.
Any advice is appreciated.
Boris Keffler
I have an odd question and I hope I say it right. Hypothetical situation.
Someone purchases a gamer keyboard on Ebay. Installs the keyboard. There are 8 preset buttons, ie: volume -up/down, email, etc.
Is it possible that a person could purchase a keyboard that was programmed to gather keystrokes and send packets out to an undetermined location to be interpreted by a scrupulous party?
Thank you.
Dia
People sometimes use these names for their Wi-fi in a slightly ridiculous attempt to keep other people from trying to hack in and use it themselves. But if somebody has the skill to hack into the wi-fi then they know that it’s not really the police’s wi-fi anyway, making the attempt a bit futile.
Thomas Barrett
Very informative and well written article. But I believe you’ve left out one method for defeating Keyloggers. Advanced Cyber Security, of Bohemia NY has a patent on an Automatic encryption system that encrypts and decrypts automatically from the zero kernel to what ever field or program it being typed into.
Daniel
The “Israeli police” arrested a couple in London?
Adam Domagala
Ich denke, dass Ihr Inhalt großartig ist und wirklich zu mir beiträgt xy
plshelpty
I accidentally installed and shared a zoom screen with a hacker before I realize what was happening? I’ve canceled all my bank information and cards but what can I do to clean my PC? My antivirus detected 8 malwares and quarantined them alraedy. But im not sure if they’re important to the system or virus
Jodi L Paul
Very informative
Parul verma
My Google account hack please recover my Google account
Lukas
I think I have been hacked and I don’t know what it was kaylogger or something bigger
ebe
please can I talk to a professional on this.mine is been detected by antivirus
Austin Scott
Hello my name is Austin and I have a friend who believes that his iCloud and Gmail password have both been compromised via key logging or some other way to acquire passwords. This has become such an issue being that he works in the technology field he has lost his job due to lack of security within his network, he works remotely so his job considered network security essential to be employed there. This is a constantly reoccurring issue for him. Today he thought the problem had been solved because he got a new router as well as a new iPhone device and has changed the password for everything multiple times as well as using two factor identification. The “Geniuses” at apple were of no help. This morning he went to check his Verizon FiOS app to see why his Wi-Fi was running slow and after clicking the app icon he was led directly to an obviously fake login page. As you can imagine this is extremely frustrating for him as well as debilitating. Because he is in the technology field he has too much pride to reach out to professionals so i am doing so for him. Could you please help me help my friend, we are desperate to fix this reoccuring issue. I would like the opportunity to explain in detail the events leading to this and i have some other questions regarding this matter, so i would like a proffessionals opinion and help. Please help us, this is causing him extreme amounts of stress and I refuse to watch and do nothing, but because I don’t know much about this field I am seeking your help. Please contact me at 4104224195 or austinleejohnscott2397@gmail.com.
Thank you so much.
Tabitha Holden
I can’t access my Gmail account and the verification codes are not working to reset password I have social security money linked to the. Email and can’t get ahold of any one over 1 month now. The Gmail account isn’t listed here yet can someone please help me?