
Programs for cracking commercial software are, sadly, not unpopular. They have also caught the attention of malware writers, who prepared a couple of surprises for those who don’t mind a free ride every now and then.
A short time ago, we detected a Trojan dropper which passes itself off as a key generator for Kaspersky Lab products. The file’s name is kaspersky.exe.
Once launched, the file displays a key generator window prompting the user to select a product. After one of the options is selected, the program proceeds to generate a key.
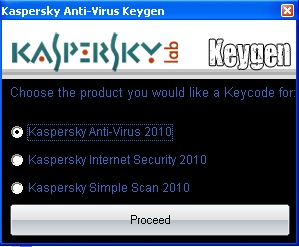
Keygen window
While the freebie lover is waiting for the result, two pieces of malware that were stealthily installed and launched by the dropper make themselves at home on the PC.
One of these is detected by Kaspersky Lab as Trojan.MSIL.Agent.aor. It steals registration data for other programs, as well as passwords, mostly for online games. It rather considerately stores all the stolen data in one file. A fragment of the file is shown on the screenshot below.
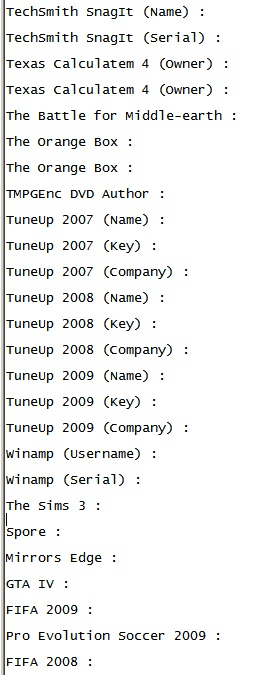
Fragment of a file that is filled in with registration data for the software listed in it
The Trojan also modifies the ‘hosts’ system file to block access to a number of websites. For example, such websites as virustotal.com and virusscan.jotti.org, which offer file scanning by solutions from many antivirus vendors, become inaccessible.
Fragment of a modified hosts file:
##Do not touch this file, changing it will cause SERIOUS damage to your computer
127.0.0.1 virustotal.com
127.0.0.1 www.virustotal.com
127.0.0.1 www.virusscan.jotti.org/
127.0.0.1 www.virusscan.jotti.org/en
127.0.0.1 www.virusscan.jotti.org/en
The second piece of malware installed by the dropper is a typical backdoor which also has keylogger functionality, collecting keystroke data. It is detected as Trojan.Win32.Liac.gfu.
Thus, running a supposed key generator for Kaspersky Internet Security will plant a couple of very real malicious programs on your computer, which KIS will then have to deal with. Provided, of course, that the keys generated by the ‘keygen’ actually work.





















A keygen with a twist