
In January we detected a phishing mailing that was sent on behalf of Apple. The messages contained an offer to purchase a card giving a discount of 150 euros in any European AppStore for only 9 euros. The senders also underlined that only valued customers were eligible to receive the card.
To place an order for the card, Apple fans had to open an attached HTML page and fill in all the fields, such as information about the user’s bank card, including the three-digit security code stated on the reverse of the card.
In exchange, the scammers promised to send a discount card via email within 24 hours. But evidently it was just another scam to trick users. The fraudsters also used the Apple logo and automated subscriptions at the end of the message to confuse victims.
The scammers didn’t just target logins and passwords for personal accounts but also users’ banking information, and in order to achieve their goal they are willing to promise anything. Inexperienced users may find it difficult to see through the fraud, but requests for confidential bank information or data that gives access to personal accounts are a clear sign of a phishing scam.

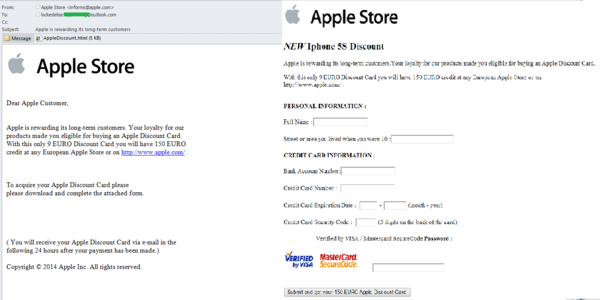





















A ‘gift’ for Apple’s Valued Customers