
You can read our Full Technical Paper on SPE / miniFlame here.
In May 2012, a Kaspersky Lab investigation detected a new nation-state cyber-espionage malware, which we named “Flame”. Our research also identified some distinguishing features of Flames modules. Based on those features, we discovered that in 2009, the first variant of the Stuxnet worm included a module that was created based on the Flame platform. This confirmed there was some form of collaboration between the groups that developed the Flame and Tilded (Stuxnet/Duqu) platforms.
A more in-depth research conducted in June 2012 resulted in the discovery of another nation state-sponsored and previously unknown malware which we named Gauss. Gauss used a modular structure resembling that of Flame, a similar code base and system for communicating with command-and-control (C&C) servers, as well as numerous other similarities to Flame.
In partnership with Symantec, ITU-IMPACT and CERT-Bund/BSI, we also published our analysis of the Flame Command and Control servers. The analysis showed that the code can understand several communication protocols to talk to different clients or malware:
- OldProtocol
- OldProtocolE
- SignupProtocol
- RedProtocol (mentioned but not implemented)
A close look at these protocol handlers revealed four different types of clients (“malware”) codenamed SP, SPE, FL and IP:
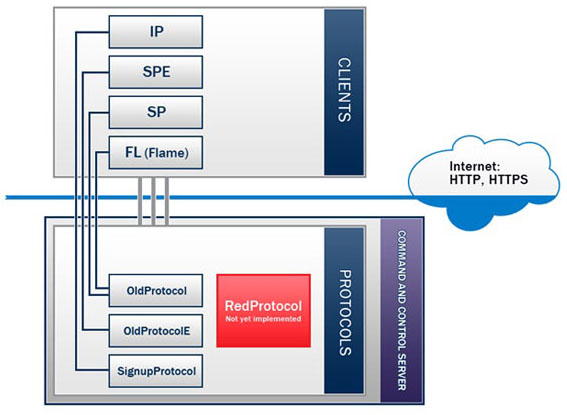
Based on the code logic, we can confirm that the Flame malware was identified as client type “FL”. Obviously, this meant there were at least three other undiscovered cyber-espionage or cyber-sabotage tools created by the same authors: SP, SPE and IP.
Meet SPE, the miniFlame
The SPE malware was uncovered in the course of the ongoing investigation, initiated by International Telecommunication Union and conducted by Kaspersky Lab.
After we analysed the Flame C2, we were surprised to discover this new module appeared to use OldProtocolE for connections, which are used by the mysterious SPE malware. We therefore understood the Flame plugin was in fact a unique, standalone malware: and it was the one known as “SPE” by the Flame C2.
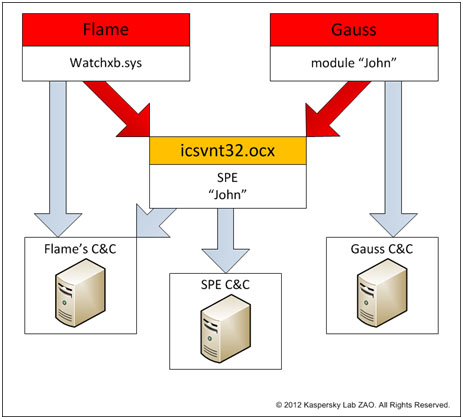
It all started in early July 2012, when we discovered a smaller, interesting Flame module. The module had many similarities with Flame which led us to believe it was an earlier version of it (all known Flame variants are version 2.x). In the months that followed, we not only studied the connection of this malware with Flame, but also came across examples of this module being used concurrently with Gauss and being controlled by the Gauss main module.
miniFlame / SPE details
The SPE malware, which we call “miniFlame”, is a small, fully functional espionage module designed for data theft and direct access to infected systems. If Flame and Gauss were massive spy operations, infecting thousands of users, miniFlame/SPE is a high precision, surgical attack tool.
miniFlame is in fact based on the Flame platform but is implemented as an independent module. It can operate either independently, without the main modules of Flame in the system, or as a component controlled by Flame.
It is also notable that miniFlame can be used in conjunction with another espionage program, namely Gauss. As many readers will remember, it has been assumed that Flame and Gauss were parallel projects that did not have any modules or C&C servers in common. The discovery of miniFlame, which works with both these espionage projects, proves that we were right when we concluded that they had come out of the same cyber-weapon factory.
Apparently, the development of miniFlame began several years ago and continued through 2012. Based on the C&C code, the protocols serving SP and SPE were created before or at the same time as the communication protocol used by FL (Flame), i.e., in 2007 at the least.
We believe that the developers of miniFlame created dozens of different modifications of the program. At this time, we have “only” found six of these, dated 2010-2011.
In some cases, dedicated C&C servers were used exclusively to control the SPE operation. Concurrently with that, some SPE variants worked with the servers which communicated with Flame.
miniFlame/SPE is different from Flame and Gauss in that the number of infections is significantly smaller. While we estimate the total number of Flame/Gauss victims at no less than 10,000 systems, SPE has been detected in just a few dozen systems in Western Asia. This indicates that SPE is a tool used for highly targeted attacks, and has probably been used only against very specific targets that have the greatest significance and posing the greatest interest to the attackers.
| Name | Incidents (KL stats) | Incidents (approx.) |
| Stuxnet | More than 100 000 | More than 300 000 |
| Gauss | ~ 2500 | ~10 000 |
| Flame (FL) | ~ 700 | ~5000-6000 |
| Duqu | ~20 | ~50-60 |
| miniFlame (SPE) | miniFlame (SPE) | ~50-60 |
Unlike Flame, where the vast majority of incidents were recorded in Iran and Sudan, and unlike Gauss, which was mostly present in Lebanon, SPE does not have a clear geographical bias. However, we believe that the choice of countries depends on the SPE variant. For example, the modification known as 4.50 is mostly found in Lebanon and Palestine. The other variants were reported in other countries, such as Iran, Kuwait and Qatar.
The original SPE distribution vector is unknown. However, since it is known to have worked both as part of Flame and as part of Gauss and since it shares its C&C servers with Flame, we believe that in most cases SPE was installed from C&C servers onto systems that were already infected with Flame or Gauss.
The link with Gauss
The SPE/miniFlame malware is unique in a sense that it can work either as a stand-alone program, as a Flame plugin or as a Gauss plugin. Essentially, it is a link connecting the Flame and Gauss projects tighter, while remaining independent of them. It uses either its own C&C servers or common servers with Flame.
In total, we detected six different versions of SPE. All of them were created over the period from 1 October 2010 to 1 September 2011.
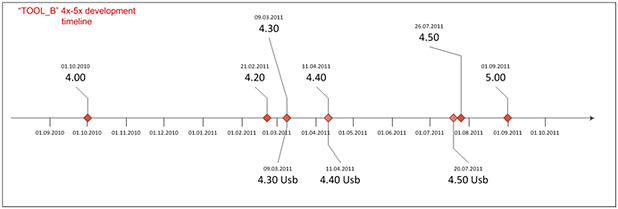
At the time of writing, version 4.50 is the most widespread in the wild.
Sinkhole statistics
During our investigations, we were able to sinkhole several of the Flame C&C domains as well as several miniFlame domains. The statistics below are for miniFlame connections only.
Between 28th of May 2012 and September 30th, we counted close to 14,000 connections in total, coming from about 90 different IPs.
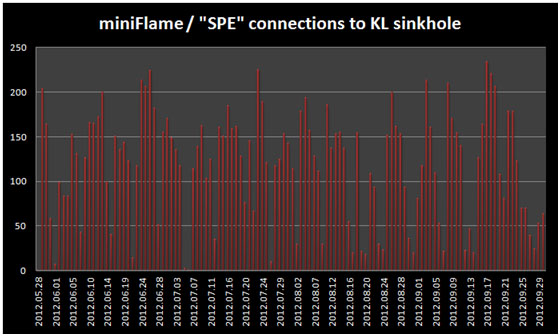
Distribution of IPs of infected victims:
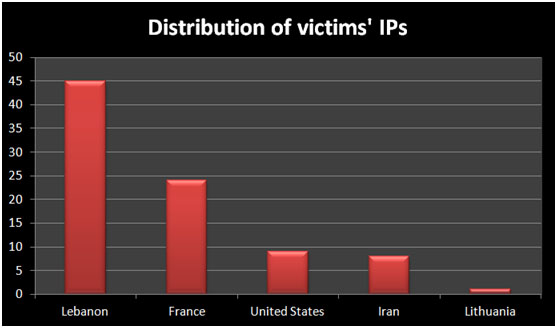
We have traced the IPs in the United States to VPN connections. Similarly, the IP in Lithuania belongs to an ISP which provides satellite internet services in Lebanon. The IPs in France are the most curious ones some do appear to be proxies or VPNs, but others are not so obvious.
For instance, one of the IPs of victims in France belongs to Francois Rabelais University of Tours:
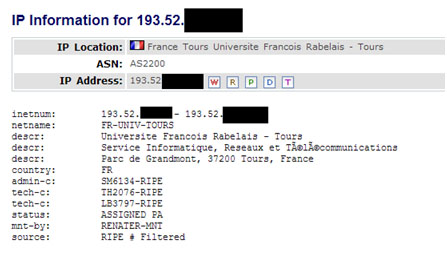
Other IPs in France belong to mobile internet users or free internet users.
Overall, it seems that the two main locations of victims are Lebanon and Iran.
The SPE / miniFlame backdoor:
The main purpose of miniFlame is to act as a backdoor on infected systems, allowing direct control by the attackers.
The following commands are understood by the malware:
| Command name | Description |
| FIONA | Write file from the C&C to the victim machine |
| SONIA | Send a file from the victim machine to the C&C |
| EVE | Load a specified DLL and execute its specified export with no arguments |
| ELVIS | Create a process with given parameters, wait for it |
| DRAKE | Remove StandardTimeBias parameter from registry, signal the event GlobalTRStepEvent (self-destruct) |
| CHARLES | Write a new StandardTimeBias value to the registry |
| SAM | Sleep for a specified amount of time |
| ALEX (Version 5.00) | Get system idle time in milliseconds |
| BARBARA (Version 5.00) | Make a screenshot of the foreground window if it belongs to one of the predefined processes. |
| TIFFANY (Version 5.00) | Switch to the C&C server provided in the parameters of the command |
All the commands are issued through the C&C server and are encrypted with a basic XOR of 10 bytes and an additional layer of Twofish encryption.
Conclusions
During the analysis of the Flame C&C server side code, we identified four different malware files known to the server: SP, SPE, FL and IP. The malware known as FL is Flame. Today, we are announcing the discovery of the malware known as SPE.
Based on our analysis, we have been able to put together several main points of SPE which we also dubbed the “miniFlame”, or “John”, as named by the corresponding Gauss configuration:
- The miniFlame malware is not widespread. It is probably deployed only on a very small number of “high profile” victims.
- Unlike Gauss, SPE/miniFlame implements a full client/server backdoor, which allows the operator direct access the infected system.
- The Flame C&C code weve analysed does not appear to contain specific modules to control SPE clients; we can assume other dedicated SPE C2 servers exist or existed, with its own special codebase.
- The development of SPE was carried out in parallel to Flame and Gauss, during 2010-2011.
- Both Flame and Gauss make use of miniFlame/SPE as a module.
- The most recent variant of SPE is 5.00; the earliest known one is 4.00.
- The exact infection vector for SPE is unknown; it is believed that the malware gets deployed from the Command and Control server during Flame or Gauss infections.
- Version 4.20 of the malware contains a debug path in the binary which points to “C:projectseSP4.2general_vobspReleaseicsvnt32.pdb”. This indicates the author named the malware “SP4.2”, although it uses the “SPE” client type in C2 parlance. It is possible that SP is simply an earlier version of miniFlame/SPE (v1.00 to v3.xx).
- SPE/miniFlame consolidates the theory of a strong link between Flame and Gauss teams. The miniFlame represents a common module used by both.
- All known 4.xx versions of SPE contain a version info section which references code page 3081, ENG_AUS, English (Australia)
If Flame and Gauss were massive spy operations, infecting thousands of users, SPE/miniFlame is a high precision espionage tool. The numbers of its victims is comparable to Duqu.
We can assume this malware was part of the Flame and Gauss operations which took place in multiple waves. First wave: infect as many potentially interesting victims as possible. Secondly, data is collected from the victims, allowing the attackers to profile them and find the most interesting targets. Finally, for these “select” targets, a specialized spy tool such as SPE/miniFlame is deployed to conduct surveillance/monitoring.
Within the Flame C&C code, two other malware files are referenced: SP and IP. If SP probably refers to an older variant of the malware described in this paper, IP is probably different and still remains unknown. According to the C2 source code, IP is also the most recent malware from the pack.
With Flame, Gauss and miniFlame, we have probably only scratched surface of the massive cyber-spy operations ongoing in the Middle East. Their true, full purpose remains obscure and the identity of the victims and attackers remain unknown.
You can read our Full Technical Paper on SPE / miniFlame here.
Kaspersky Lab would like to thank CERT-Bund/BSI for their kind assistance with this investigation.






















miniFlame aka SPE: “Elvis and his friends”