
Figures of the year
In 2022:
- 48.63% of all emails around the world and 52.78% of all emails in the Russian segment of the internet were spam
- As much as 29.82% of all spam emails originated in Russia
- Kaspersky Mail Anti-Virus blocked 166,187,118 malicious email attachments
- Our Anti-Phishing system thwarted 507,851,735 attempts to follow phishing links
- 378,496 attempts to follow phishing links were associated with Telegram account hijacking
Phishing in 2022
Last year’s resonant global events
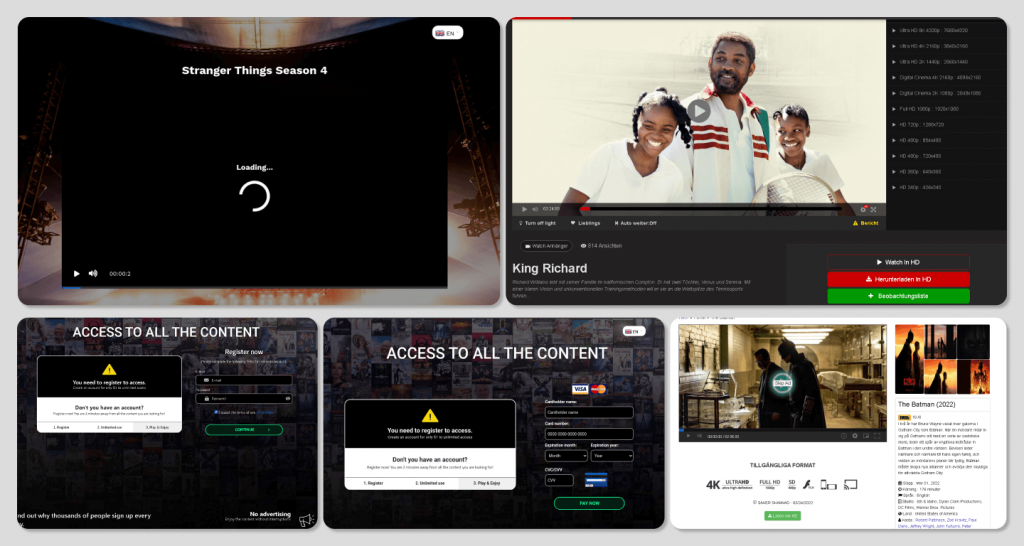
The year 2022 saw cybercrooks try to profit from new film releases and premieres just as they always have. The bait included the most awaited and talked-about releases: the new season of Stranger Things, the new Batman movie, and the Oscar nominees. Short-lived phishing sites often offered to see the premieres before the eagerly awaited movie or television show was scheduled to hit the screen. Those who just could not wait were in for a disappointment and a waste of cash. The promises of completely free access to the new content were never true. By clicking what appeared to be a link to the movie, the visitor got to view the official trailer or a film studio logo. Several seconds into the “preview”, the stream was interrupted by an offer to buy an inexpensive subscription right there on the website to continue watching. If the movie lover entered their bank card details on the fake site, they risked paying more than the displayed amount for content that did not exist and sharing their card details with the scammers.
Some websites that offered soccer fans free broadcasts of the FIFA World Cup in Qatar employed a similar scheme, but the variety of hoaxes aimed at soccer fans proved to be wider than that used by scammers who attacked film lovers. Thus, during the World Cup a brand-new scam appeared: it offered users to win a newly released iPhone 14 for predicting match outcomes. After answering every question, the victim was told that they were almost there, but there was a small commission to be paid before they could get their gadget. Of course, no prize ensued after the fee was paid.
Soccer fans chasing merchandise risked compromising their bank cards or just losing some money. Scammers created websites that offered souvenirs at low prices, including rare items that were out of stock in legitimate online stores. Those who chose to spend their money on a shady website risked never getting what they ordered.
Websites that offered tickets to the finals were another type of soccer-flavored bait. Scammers were betting on the finals typically being the most popular stage of the competition, tickets to which are often hard to get. Unlike legitimate ticket stores, the fake resellers were showing available seats in every sector even when the World Cup was almost closed. Vast selection of available seats should have alarmed visitors: real tickets would have been largely gone.
Fake donation sites started popping up after the Ukraine crisis broke out in 2022, pretending to accept money as aid to Ukraine. These sites referenced public figures and humanitarian groups, offering to accept cash in cryptocurrency, something that should have raised a red flag in itself.
The pandemic
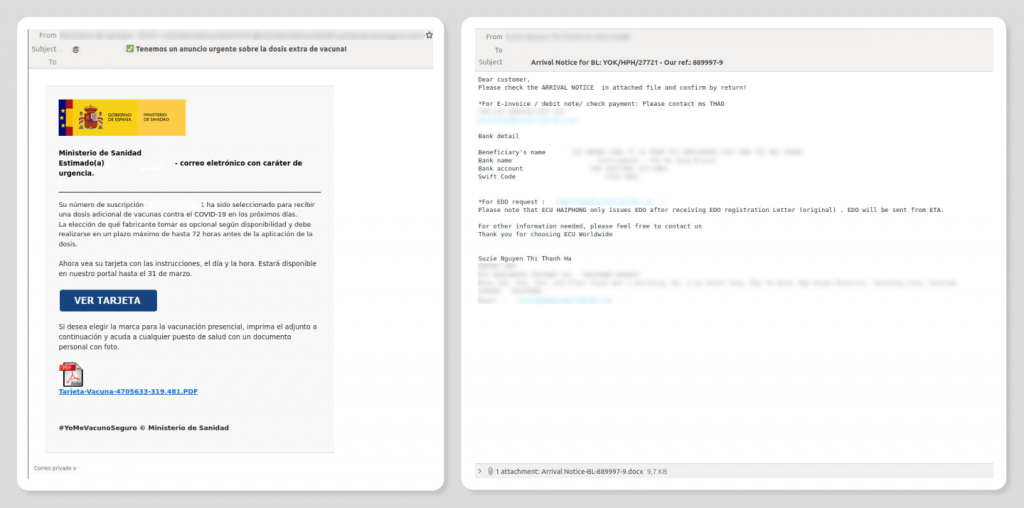
The COVID-19 theme had lost relevance by late 2022 as the pandemic restrictions had been lifted in most countries. At the beginning of that year, we still observed phishing attacks that used the themes of infection and prevention as the bait. For example, one website offered users to obtain a COVID vaccination certificate by entering their British National Health Service (NHS) account credentials. Others offered the coveted Green Pass without vaccination.
Scammers abused legitimate survey services by creating polls in the name of various organization to profit from victims’ personal, including sensitive, data. In another COVID-themed scheme, the con artists introduced themselves as the Direct Relief charity, which helps to improve the quality of life and healthcare in poorer regions. Visitors were offered to fill out a form to be eligible for $750 per week in aid for twenty-six weeks. The survey page said the “charity” found the victim’s telephone number in a database of individuals affected by COVID-19. Those who wished to receive the “aid” were asked to state their full name, contact details, date of birth, social security and driver’s license numbers, gender, and current employer, attaching a scanned copy of their driver’s license. To lend an air of authenticity and to motivate the victim to enter valid information, the swindlers warned that the victim could be prosecuted for providing false information. The scheme likely aimed at identity theft: the illegal use of others’ personal details for deriving profit. The cybercrooks might also use the data to contact their victims later, staging a more convincing swindle.
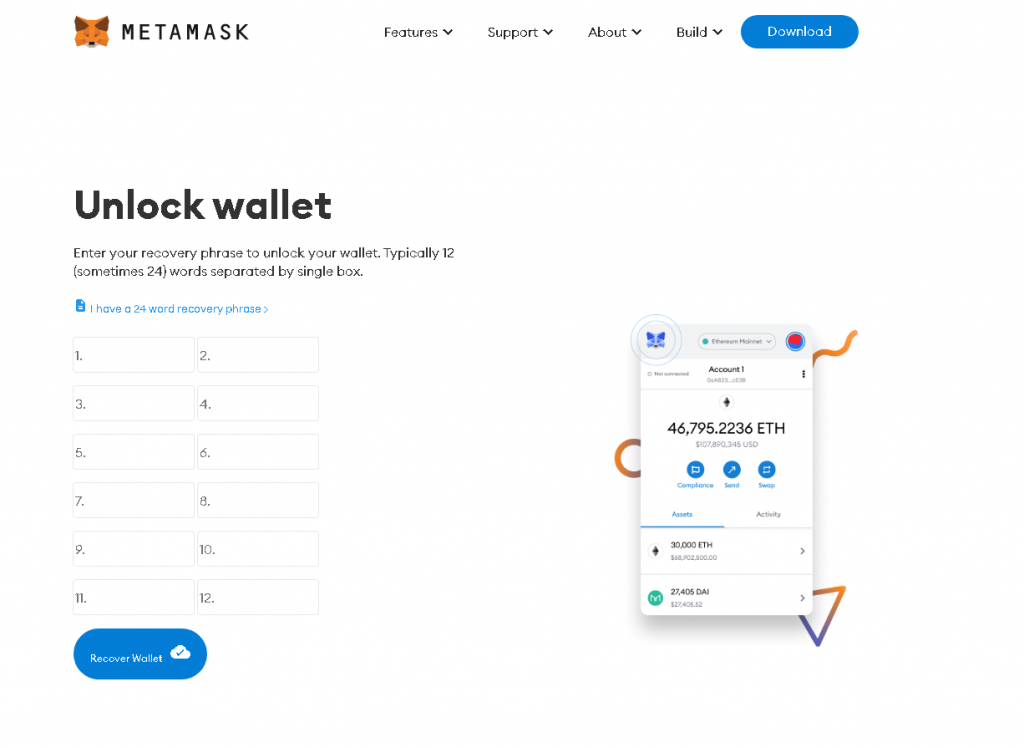
Crypto phishing and crypto scams
The unabated popularity of cryptocurrency saw crypto scammers’ interest in wallet owners’ accounts growing, despite the fact that rates continued to drop throughout the year. Cybercriminals chased seed phrases, used for recovering access to virtual funds. By getting the user’s secret phrase, cybercriminals could get access to their cryptocurrency balance.
In a typical internet hoax manner, crypto scam sites offered visitors to get rich quick by paying a small fee. Unlike common easy-money scams, these websites asked for payments in cryptocurrency — which they promised to give away and which they were trying to steal. The “giveaways” were timed to coincide with events that were directly or indirectly associated with cryptocurrency. Thus, one of the fake sites promised prizes on the occasion of Nvidia thirty-year anniversary (the company is a major vendor of graphics processing units, which are sometimes used for crypto mining). Promotion of cryptocurrency use was another pretext for the “giveaways”. Users were offered to deposit up to 100 cryptocurrency units for a promise to refund two times that amount, purportedly to speed up digital currency adoption. In reality, the scheme worked the way any other internet hoax would: the self-professed altruists went off the radar once they received the deposit.
Compensation, bonus, and paid survey scams
Bonuses and compensations are hard to deny in times of crisis and instability, but it is worth keeping in mind that “financial assistance” is frequently promised by con artists to swindle you out of your money.
“Promotional campaigns by major banks” were a popular bait in 2022. Visitors to a fraudulent web page were offered to receive a one-time payment or to take a service quality survey for a fee. Unlike the prizes offered in the aforementioned crypto schemes, these fees were smaller: an equivalent of $30–40. The cybercriminals used an array of techniques to lull victims’ vigilance: company logos, assurances that the campaigns were legit, as well as detailed, lifelike descriptions of the offer. Similar “campaigns” were staged in the name of other types of organizations, for example, the Polish finance ministry.
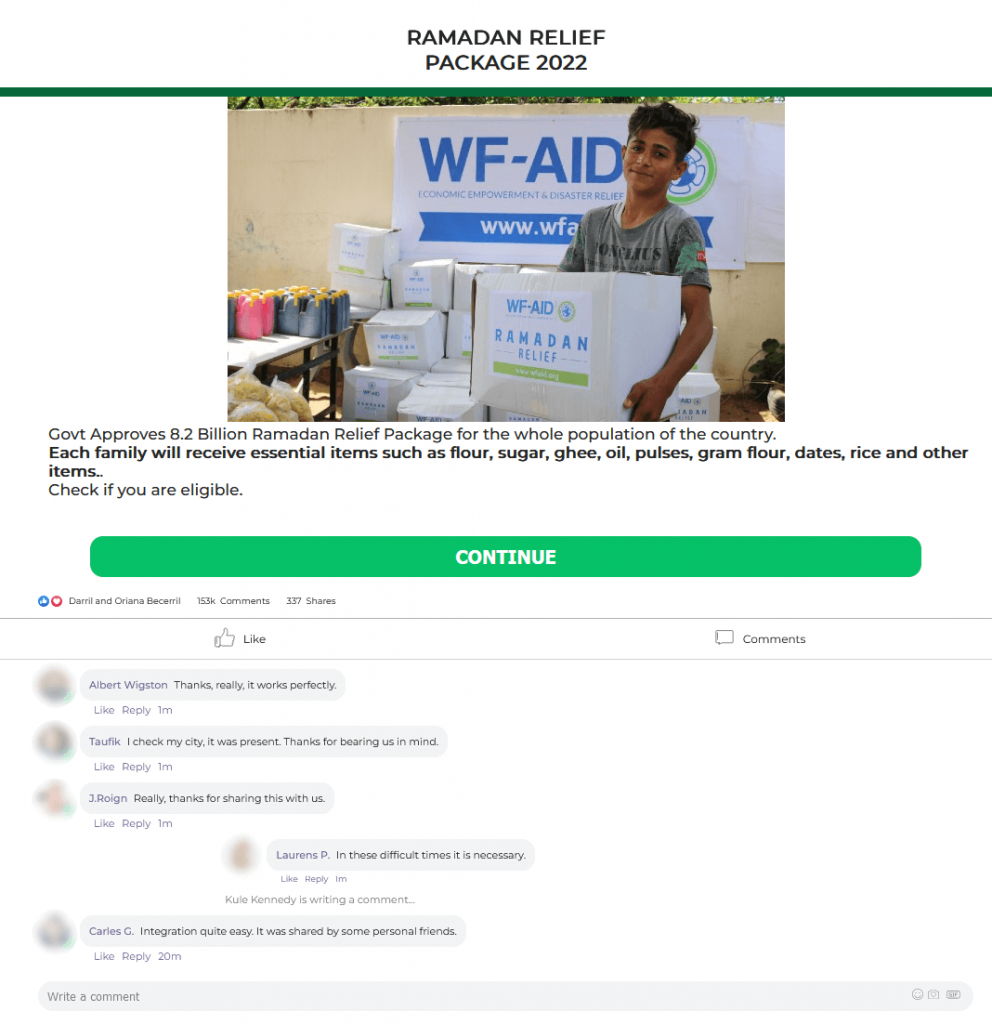
Aid as distributed by various governmental and nongovernmental organizations remained a popular fraud theme in 2022. For example, in Muslim countries, scammers promised to send charity packages, purportedly under a “Ramadan Relief” program that aimed at helping low-income families during the Ramadan fast. The fasting period typically sees higher prices for food and household products, whereas observers buy more than they normally do and may be faced with a shortage of money. Legitimate charities, such as WF-AID, do operate Ramadan relief programs, and judging by the screenshot below, the fraudsters were pretending to represent that organization. An eye-catching picture of the organization’s logo and huge boxes was accompanied by a list of foodstuffs included in the aid package, with positive “recipient feedback” posted below the message. The victim was asked to make sure that their name was on the list of recipients, so they could get a package. This required providing personal data on the website and sending a link to the scam site to instant messaging contacts—nothing extraordinary for hoaxes like this. This way, the scammers both populate their databases and have victims spread links to their malicious resources for them. In addition to that, they might ask the victim to cover the “shipping costs”.
Growing utility rates and an increase in the price of natural resources have prompted several governments to start discussing compensations for the population. Payout notices could arrive by mail, email, or as a text message. Cybercriminals attempted to take advantage of the situation by creating web pages that mimicked government websites, promising cash for covering utility payments or compensation of utility expenses. Visitors were occasionally asked to provide personal details under the pretext of checking that they were eligible, or simply to fill out a questionnaire. In Britain, con artists posing as a government authority promised to compensate electricity costs. The description of the one-time payout was copied from the official website of the authority, which did provide the type of compensation. After completing the questionnaire, the victim was asked to specify the electric utility whose services they were using and enter the details of the bank card linked to their account with the utility. The promise of £400 was supposed to make the victim drop their guard and share their personal information.
In Singapore, scammers offered a refund of water supply costs, purportedly because of double billing. An energy or resource crisis was not used as a pretext in this particular case, but refunds were still offered in the name of the water supply authority.
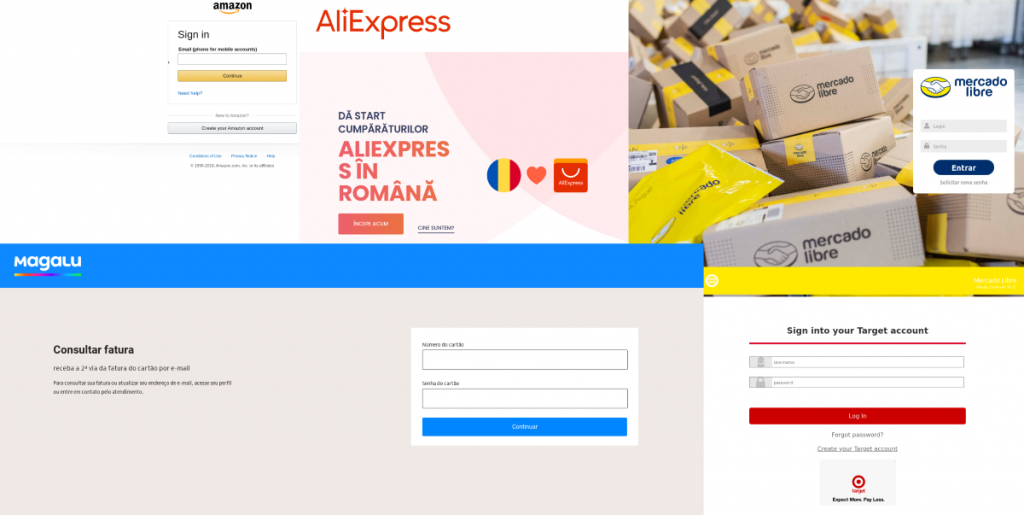
Fake online stores and large vendor phishing
We see fake websites that imitate large online stores and marketplaces year after year, and 2022 was no exception. Phishing attacks targeted both the customers of globally known retailers and regional players. An attack often started with the victim receiving a link to a certain product supposedly offered at an attractive price, by email, in an instant messaging app, or on a social network. Those who fell for the trick could lose access to their accounts, have their bank card details stolen, or waste the money they wanted to spend on the dirt-cheap item.
“Insides” about “private sales” were also used as a lure. Thus, a web page that copied the appearance of a Russian marketplace promised discounts of up to 90% on all items listed on it. The page design did look credible, with the only potential red flags being really low prices and the URL in the address bar not matching the official one.
Many large vendors, notably in the home appliances segment, announced in early spring that they would be pulling out of Russia, which caused a spike in demand. This was reflected in the threat landscape, with fake online stores offering home appliances popping up all over the Russian segment of the internet (also called Runet). Large retailers being out of stock, combined with unbelievably low prices, made these offers especially appealing. The risk associated with making a purchase was to lose a substantial amount of money and never to receive what was ordered.
Hijacking of social media accounts
Users of social media have increasingly focused on privacy lately. That said, curiosity is hard to contain: people want to check out who has been following them, but do so without the other party knowing. Cybercriminals who were after their account credentials offered victims to have their cake and eat it by using some new social media capability. A fake Facebook Messenger page promised to install an update that could change the user’s appearance and voice during video calls, and track who has been viewing their profile, among other features. To get the “update”, the victim was asked to enter their account credentials, which the scammers immediately took over.
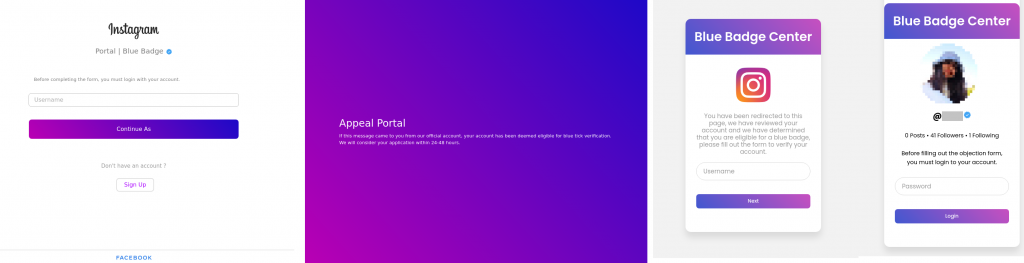
Many Instagram users dream about the Blue Badge, which stands for verified account and is typically reserved for large companies or media personalities. Cybercriminals decided to take advantage of that exclusivity, creating phishing pages that assured visitors their verified status had been approved and all they needed to do was to enter their account logins and passwords.
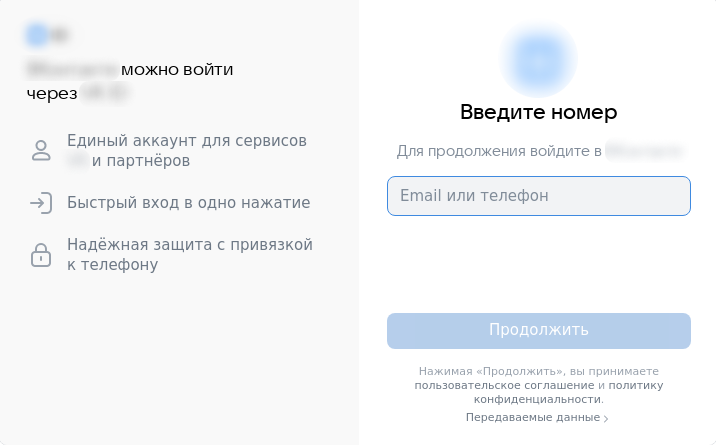
Russia blocked access to both Facebook and Instagram in March 2022, which led to the popularity of Russian social networks and Telegram skyrocketing. This increased usage meant the users’ risk of losing personal data was now higher, too. “Well-wishers” who operated scam sites offered to check if Russian social media contained any embarrassing materials on the victim. The scam operators told the users it was possible to find damaging information about every third user of a social network by running a search. If the user agreed to a search to be done for them, they were told that a certain amount of dirty linen indeed had been found. In reality, there was no search — the scammers simply stole the credentials they requested for the check.
One of the added risks of social media phishing is scammers getting access to both the social media account itself and any linked services.
The Telegram Premium status provides a range of benefits, from an ad-free experience to an ability to block incoming voice messages, but the subscription costs money. Scammers offered to “test” a Premium subscription free of charge or simply promised to give one for free if the victim entered their Telegram user name and password or a verification code sent by the service, which was exactly what the cybercrooks were after.
One more phishing campaign targeting Telegram users was arranged to coincide with the New Year’s celebration. Scammers created a page on the telegra.ph blogging platform that posted a gallery of children’s drawings, encouraging users to vote for their favorites. Scammers sent a link to that page from hacked accounts, asking users to vote for their friends’ kids’ works. Those who took the bait were directed to a fake page with a login form on it. The cybercriminals were betting on the users to go straight to voting, without checking the authenticity of the drawings, which had been copied from various past years’ competition pages, as requests to vote for one’s friends’ kids are common before public holidays.
The Telegram auction platform named Fragment went live in the October of 2022: it was selling unique usernames. You can become a user by linking your Telegram account or TON wallet. Scammers who were after those account details sent out links to fake Fragment pages. A visitor who tried to buy a username from the fake website was requested to log in. If the victim entered their credentials, the scam operators immediately grabbed those.
Spam in 2022
The pandemic
Unlike phishing, COVID-themed spam is still a thing. Most of that is “Nigerian-type” scams: millionaires dying from COVID bequeathing their money to treatment and prevention efforts, and to improve the lives of those who have recovered, or Mark Zuckerberg running a special COVID lottery where one can win a million euros even if they are not a Facebook user. Recipients are told that they could claim some IMF money left unallocated because of the pandemic. Others are offered hefty amounts under an anti-recession assistance program.
The amount of spam exploiting the coronavirus theme in some way dropped noticeably during 2022: at the beginning of the year, we were blocking a million of these emails per month, but the figure had shrunk by three times by yearend.
Contact form spam
The year 2022 saw cybercriminals abuse contact forms for spam more frequently. In a typical scheme of this kind, scammers find websites that offer registration, contact, or support request forms that do not require the user to be logged in to submit, and do not check the data entered. In some cases, they insert a scam message with a hyperlink in the login or name fields, and in others, add a longer text with images to the message field. Then the attackers add victims’ email addresses to the contact fields and submit. When getting a message via a registration or contact form, most websites reply to the user’s email address that their request was received and is being processed, their account has been created, and so on. As a result, the person gets an automated reply from an official address of a legitimate organization, containing unsolicited advertisements or a scam link.
Most scam messages offer a compensation or prize to the recipient. For example, a spam email targeting Russian users promised an equivalent of $190–4200 in VAT refunds. To get the money, the victim was offered to open the link in the message. This scheme is a classic: a linked web page requests that the user pay a commission of under a dozen dollars, which is insignificant in comparison to the promised refund. We observed many varieties of contact form money scam: from fuel cards to offers to make money on some online platform.
Scammers took advantage of forms on legitimate sites all around the world. Where spam email in Russian typically played on “prizes” or “earning money”, messages in other languages, in addition to offering “prizes”, encouraged users to visit “dating sites” — in fact, populated by bots — where the victims would no doubt be asked to pay for a premium account.
We blocked upward of a million scam emails sent via legitimate forms in 2022.
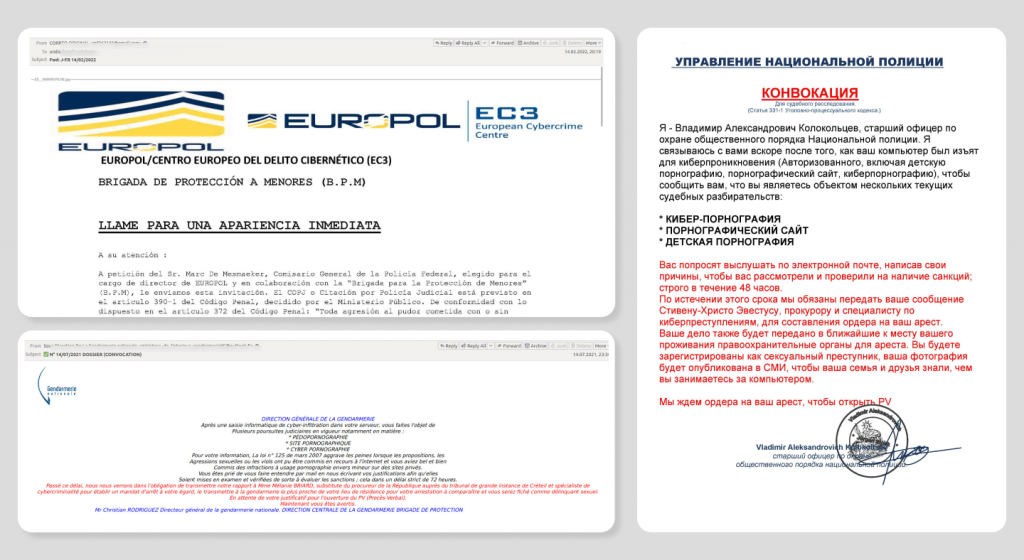
Blackmail in the name of law enforcement agencies
Extortion spam is nothing new. In such emails, attackers usually claim that the recipient has broken the law and demand money. In 2022, these mailings not only continued, but also evolved. For example, there was virtually no text in the messages: the user was either asked to open an attached PDF file to find out more, or they received threats in the form of an image with text. In addition, the geography of mailings widened in 2022.
The essence of the message, as in similar emails sent earlier, was that a criminal case was going to be opened against the recipient due to allegedly visiting sites containing child pornography.
To avoid serious consequences, the attackers urged the victim to respond as soon as possible to the sender and “settle the matter”. Most likely, the scammers would ask for a certain amount of money to be paid in further correspondence for the victim’s name to be removed from the “criminal case”. In 2022, we blocked over 100,000 blackmail emails in various countries and languages, including French, Spanish, English, German, Russian and Serbian.
Exploiting the news
Spammers constantly use major world events in their fraudulent schemes. The 2022 geopolitical crisis was no exception. Throughout the year, we saw mailings aimed at English-speaking users proposing transferring money, usually to a Bitcoin wallet, to help the victims of the conflict in Ukraine. Scammers often demand the transfer of money to Bitcoin wallets, as it is more difficult to trace the recipient through cryptocurrency transactions than through the bank ones. Blackmail demanding payment in cryptocurrency used to prevail in spam. Now, attackers have started collecting Bitcoin for charity.
The news agenda was also used in other scam mailings. For example, in early July, our solutions blocked 300,000 emails where fraudsters were requesting help on behalf of a Russian millionaire, who allegedly wanted to invest money and avoid sanctions. Another mailing said that the European Commission had decided to give away a fund created by Russian oligarchs, and the email recipient might be lucky to get a piece of this pie.
More and more “business offers” are appearing among spam mailings, and they exploit the current information agenda. Due to economic sanctions in 2022, enterprising businessmen offered replacements for goods and services from suppliers who left the Russian market. For example, spammers actively advertised services of a company transporting people to Russia. The email text emphasized the fact that many transport companies refused to provide such services.
There were also spam mailings where various companies offered to replace popular international software with Russian equivalents or solutions developed in third countries. In addition, there were spam propositions for intermediary services to open a company or bank account in neighboring countries, such as Armenia, as well as offers of assistance in accepting payments from foreign partners.
The shortage of printer paper in Russia in March and April 2022 spawned a wave of related ads offering paper at discount prices.
Spammers in 2022 also actively marketed their promotional mailing services as alternative advertising to unavailable promotion via platforms such as Instagram. For example, in April we blocked around a million of such mailings.
Against the backdrop of sanctions and the accompanying disruption of supply chains, there has been an increase in spam offering goods and services from Chinese suppliers. In 2022, our filter blocked more than 3.5 million emails containing such offers, and the number of them was growing, from around 700,000 in the first quarter to more than a million in the fourth.
Spam with malicious attachments
Employees shifting to remote work during the pandemic and the associated growth of online communications spurred the active development of various areas of phishing, both mass and targeted. Attackers have become more active in imitating business correspondence, not only targeting HR-specialists and accountants, as before the pandemic, but also employees in other departments. In 2022, we saw an evolution of malicious emails masquerading as business correspondence. Attackers actively used social engineering techniques in their emails, adding signatures with logos and information from specific organizations, creating a context appropriate to the company’s profile, and applying business language. They also actively exploited off the current news agenda and mentioned real employees from the company supposedly sending the emails. Spammers faked their messages as internal company correspondence, business correspondence between different organizations, and even as notifications from government agencies.
Masking malicious emails as business correspondence has become a major trend in malicious spam in 2022. Attackers tried to convince the recipient that it was a legitimate email, such as a commercial offer, a request for the supply of equipment, or an invoice for the payment of goods. For example, throughout the year, we encountered the following scheme. Attackers gained access to real business correspondence (most likely by stealing correspondence from previously infected computers) and sent malicious files or links to all of its participants in response to the previous email. This trick makes it harder to keep track of malicious emails, and the victim is more likely to fall for it.
In most cases, either the Qbot Trojan or Emotet was loaded when the malicious document was opened. Both can be used to steal user data, collect information about the corporate network, and spread additional malware, such as ransomware. Qbot also allows you to gain access to emails and steal them for further attacks.
Mailings imitating notifications from various ministries and other government organizations have become more frequent in the Runet. Emails were often designed to take into account the specific activities of the organizations they were pretending to be. The sender’s addresses copied the logic of email addresses in the relevant agencies, and the malicious attachment was disguised as some kind of specialized document, such as “key points of the meeting”. For example, malicious code was found in one of these mailings that exploited a vulnerability in the Equation Editor module, the formula editor in Microsoft Office.
The perpetrators did not ignore the news agenda. In particular, the malware was distributed under the guise of call-up “as part of partial mobilization” or as a “new solution” to safeguard against possible threats on the internet “caused by hostile organizations”.
In the second case, the program installed on victim’s computer was in fact a crypto-ransomware Trojan.
Two-stage spear phishing using a known phish kit
In 2022, we saw an increase in spear (or targeted) phishing attacks targeting businesses around the world. In addition to typical campaigns consisting of one stage, there were attacks in several stages. In the first email, scammers in the name of a potential client asked the victim to specify information about its products and services. After the victim responds to this email, the attackers start a phishing attack.
Key facts:
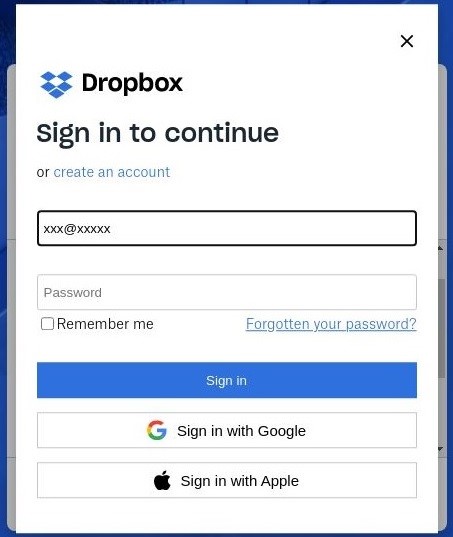
- Attackers use fake Dropbox pages created using a well-known phishing kit
- The campaign targets the sales departments of manufacturers and suppliers of goods and services
- Attackers use SMTP IP addresses and From domains provided by Microsoft Corporation and Google LLC (Gmail)
Statistics
The campaign began in April 2022, with malicious activity peaking in May, and ended by June.
Number of emails related to a two-step targeted campaign detected by Kaspersky solutions (download)
How a phishing campaign unfolds
Attackers send an email in the name of a real trade organization requesting more information about the victim company’s products. The email text looks plausible and has no suspicious elements, such as phishing links or attachments. A sender’s email address from a free domain, like gmail.com, may raise doubts. The email on the screenshot below is sent from an address in this domain, and the company name in the From field is different to its name in the signature.
Example of the first email
It is worth noting that the use of free domains is not typical for spear phishing in the name of organizations, because such domains are rarely used in business. Most often in targeted attacks, attackers either use spoofing of the legitimate domain of the organization they are pretending to be, or register domains similar to the original one. In addition, Google and Microsoft are pretty quick in blocking email addresses spotted sending spam. This is the most likely reason why attackers used different addresses in the From header (where the email came from) and Reply-to header (where the reply will go when clicking “Reply” in your email client). This means the victim responds to another address, which may be located in another free domain, such as outlook.com. The address in the Reply-to header is not used for spam, and correspondence with it is initiated by the victim, so it is less likely to be blocked quickly.
After victims respond to a first email, attackers send a new message, asking them to go to a file-sharing site and view a PDF file with a completed order, which can be found via the link.
An email with a phishing link
By clicking the link, the user is taken to a fake site generated by a well-known phishing kit. It is a fairly simple tool that generates phishing pages to steal credentials from specific resources. Our solutions blocked fake WeTransfer and Dropbox pages created with this kit.
A fake WeTransfer page created using the same phish kit as the target campaign sites
In the phishing campaign described above, the phishing site mimics a Dropbox page with static file images and a download button. After clicking any element of the interface, the user is taken to a fake Dropbox login page that requests valid corporate credentials.
A fake Dropbox page
Login page with a phishing form
When victims attempt to log in, their usernames and passwords are sent to https://pbkvklqksxtdrfqkbkhszgkfjntdrf[.]herokuapp[.]com/send-mail.
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 |
<form name="loginform"> <div class="form-group"> <label for="">Email Address</label> <input type="email" id="email" class="form-control" name="email" placeholder="email Address"> <div class="email-error"></div> </div> <div class="form-group"> <label for="">Password</label> <input type="password" id="password" class="form-control" name="password" placeholder="Password"> <div class="password-error"></div> </div> <div class="form-group btn-area"> <button class="download-btn" id="db" type="submit">Download</button> </div> </form> </div> <script src="https://firebasestorage.googleapis.com/v0/b/linktopage-c7fd6.appspot.com/o/obfuscated.js?alt=media&token=1bb73d28-53c8-4a1e-9b82-1e7d62f3826b"></script> |
HTML representation of a phishing form
Victims
We have identified targets for this campaign around the world, including the following countries: Russia, Bosnia and Herzegovina, Singapore, USA, Germany, Egypt, Thailand, Turkey, Serbia, Netherlands, Jordan, Iran, Kazakhstan, Portugal, and Malaysia.
Statistics: spam
Share of spam in mail traffic
In 2022, an average of 48.63% of emails worldwide were spam, representing a 3.07 p.p. increase on 2021. Over the course of the year, however, the share of spam in global email traffic has gradually declined, from 51.02% in the first quarter to 46.16% in the fourth.
Share of spam in global email traffic, 2022 (download)
The most active month in terms of spam was February 2022, with junk traffic accounting for 52.78% of all email correspondence. June was in second place (51.66%). December was the calmest, only 45.20% of emails in this month were spam.
On Runet, the proportion of spam in email traffic is generally higher than worldwide. In 2022, an average of 52.44% of emails were junk mailings. At the same time, the trend for a gradual shift in ratio in favor of legitimate correspondence can also be seen. We saw the largest share of spam in Runet in the first quarter, with 54.72% of all emails, and by the fourth quarter it had dropped to 49.20%.
Proportion of spam in Runet email traffic, 2022 (download)
Even though the second quarter (53.96%) was quieter in terms of spam than the first, the most active month in the Russian segment of the internet was June (60.16%). Most likely, the share of spam in June, both in Russia and globally, was influenced by the surge in mailings with offers from Chinese factories that we observed in that month. And the quietest month in Runet was December (47.18%), the same as globally.
Countries and territories — sources of spam
In 2022, the share of spam from Russia continued to grow, from 24.77% to 29.82%. Germany (5.19%) swapped places with mainland China (14.00%), whose share increased by 5.27 percentage points. Third place is still held by the United States (10.71%).
TOP 20 countries and territories — sources of spam, 2022 (download)
The Netherlands remained in fifth place (3.70%), its share decreased compared to 2021. Sixth and seventh places went to Japan (3.25%) and Brazil (3.18%), whose shares rose by 0.89 and 3.77 p.p., respectively. Next come the UK (2.44%), France (2.27%) and India (1.82%).
Malicious mail attachments
In 2022, our Mail Anti-Virus detected 166,187,118 malicious email attachments. That’s an increase of 18 million from the previous year. This component caused most triggers in March, May, and June 2022.
Number of Mail Anti-Virus hits, January — December 2022 (download)
The most common malicious email attachments in 2022, as in 2021, were Agensla Trojan stealers (7.14%), whose share decreased slightly. Noon spyware (4.89%) moved up to second place, and Badun Trojans (4.61%) spreading as archived electronic documents moved down to third place. The fourth most common malware were vulnerability exploits CVE-2018-0802 (4.33%) in Microsoft Equation Editor. In 2022, attackers used them significantly more often than CVE-2017-11882 exploits in the same component (1.80%). This vulnerability was more widespread in 2021 and has now dropped to tenth place.
TOP 10 malware families spread by email attachments in 2022 (download)
ISO Trojans (3.27%), sent in the form of disk images, moved up to number five, and the sixth most common was the Guloader downloader family (2.65%), which delivers remotely controlled malware to victims’ devices. They are closely followed by the Badur family (2.60%), PDF files containing links to web resources with questionable content, and in eighth place is the infamous Emotet botnet (2.52%). Law enforcement shut this down in early 2021, but by fall, attackers had restored the infrastructure and were actively distributing it in 2022. More recently, Emotet has been used to deliver other malware to victims’ devices, particularly ransomware. The ninth most popular family was Taskun (2.10%), which creates malicious tasks in the task scheduler.
TOP 10 types of malware spread by email attachments in 2022 (download)
The list of the most common malware sent via email usually corresponds to the list of families. As in 2021, attackers mostly distributed the same instances from the TOP 10 families.
Countries and territories targeted by malicious mailings
Spain remains the leader in terms of blocked malicious attachments in 2022 (8.78%), which is a slight decrease compared to 2021 (9.32%). The share of Russia (7.29%), on the other hand, increased slightly. Third place went to Mexico (6.73%), and fourth place to Brazil (4.81%), whose share was virtually unchanged from the previous reporting period.
TOP 20 countries and territories targeted by malicious mailings, 2022 (download)
In Italy, 4.76% of all detected malicious attachments were blocked in 2022. The country is followed by Vietnam (4.43%) and Turkey (4.31%). The percentage of Mail Anti-Virus detections on computers of users from Germany (3.85%) continued to decrease. The share in the United Arab Emirates (3.41%) also decreased slightly, dropping to ninth place, while Malaysia (2.98%) remained in tenth place.
Statistics: phishing
In 2022, the number of phishing attacks increased markedly. Our Anti-Phishing system prevented 507,851,735 attempts to follow a phishing link, roughly double the number in 2021.
Map of phishing attacks
In 2022, the geography of phishing attacks changed dramatically. Attempts to click phishing links were most often blocked on devices from Vietnam (17.03%). In 2021, this country was not among the TOP 10 most attacked countries and territories. Macau is in second place (13.88%), also absent from last year’s ranking. Madagascar is in third place (12.04%), which was seventh in 2021. In addition to Vietnam and Macau, Algeria (11.05%), Malawi (10.91%) and Morocco (10.43%) appeared at the top of the list of most attacked countries and territories. Ecuador (11.05%) moved up to fifth place, while Brunei (10.59%) dropped one place to seventh. Brazil (10.57%) and Portugal (10.33%) moved from first and third places to eighth and tenth, respectively, and France, which was second in 2021, left the TOP 10.
TOP 10 countries and territories by share of attacked users:
| Country/territory | Share of attacked users* |
| Vietnam | 17.03% |
| Macau | 13.88% |
| Madagascar | 12.04% |
| Algeria | 11.05% |
| Ecuador | 11.05% |
| Malawi | 10.91% |
| Brunei | 10.59% |
| Brazil | 10.57% |
| Morocco | 10.43% |
| Portugal | 10.33% |
* Share of users encountering phishing out of the total number of Kaspersky users in that country/territory, 2022
Top-level domains
As in previous years, the majority of phishing pages were hosted in the COM domain zone, but its share almost halved, from 31.55% to 17.69%. Zone XYZ remained in second place (8.79%), whose share also decreased. The third most popular domain among attackers was FUN (7.85%), which had not previously received their attention. The domain is associated with entertainment content, which is perhaps what attracted fraudsters to it.
Most frequent top-level domains for phishing pages in 2022 (download)
Domains ORG (3.89%) and TOP (1.80%) swapped places relative to 2021 but remained in fourth and fifth places. In addition to this, the top ten domain zones in most demand among cybercriminals included: RU (1.52%), COM.BR (1.13), DE (0.98%), CO.UK (0.98%) and SE (0.92%).
Organizations under phishing attacks
The rating of organizations targeted by phishers is based on the triggering of the deterministic component in the Anti-Phishing system on user computers. The component detects all pages with phishing content that the user has tried to open by following a link in an email message or on the web, as long as links to these pages are present in the Kaspersky database.
In 2022, pages impersonating delivery services had the highest percentage of clicks on phishing links blocked by our solutions (27.38%). Online stores (15.56%), which were popular with attackers during the pandemic, occupied second place. Payment systems (10.39%) and banks (10.39%) ranked third and fourth, respectively.
Distribution of organizations targeted by phishers, by category, 2022 (download)
The share of global internet portals (8.97%) almost halved, with almost as many phishing resources targeting users of smaller web services (8.24%). Social networks (6.83%), online games (2.84%), messengers (2.02%) and financial services (1.94%) round complete the TOP 10 categories of sites of interest to criminals.
Hijacking Telegram accounts
In 2022, our solutions stopped 378,496 phishing links aimed at hijacking Telegram accounts. Apart from a spike in phishing activity throughout June, when the number of blocked links exceeded 37,000, the first three quarters were relatively quiet. However, by the end of the year, the number of phishing attacks on the messenger’s users increased dramatically to 44,700 in October, 83,100 in November and 125,000 in December. This increase is most likely due to several large-scale Telegram account hijacking campaigns that we observed in late 2022 (article in Russian).
Number of clicks on phishing links aimed at hijacking a Telegram account worldwide, and in Russia specifically, January — December 2022 (download)
It is of note that the majority of phishing attacks were aimed at users from Russia. While in the first months of 2022 their share was approximately half of the total number of attacks worldwide, since March 70–90% of all attempts to follow phishing links by Telegram users were made by Russian users.
Phishing in messengers
Statistics on messenger-based phishing are based on anonymized data from the Safe Messaging component of Kaspersky Internet Security for Android, voluntarily provided by users of this solution. Safe Messaging scans incoming messages and blocks attempts to follow any phishing or otherwise malicious links in them.
In 2022, our mobile solution blocked 360,185 attempts to click on phishing links from messengers. Of these, 82.71% came from WhatsApp, 14.12% from Telegram and another 3.17% from Viber.
Distribution of links blocked by the Safe Messaging component, by messenger, 2022 (download)
Phishing activity on WhatsApp is down slightly since 2021. On average, the Safe Messaging component blocked 816 clicks on fraudulent links per day. The first half of the year was the most turbulent, and by the third quarter, phishing activity in the messenger had dropped sharply.
Dynamics of phishing activity on WhatsApp in 2022 (weekly number of detected links shown)
The largest number of phishing attempts on WhatsApp, approximately 76,000, was recorded in Brazil. Russia is in second place, where over the year, the Chat Protection component prevented 69,000 attempts to go to fraudulent resources from the messenger.
TOP 7 countries and territories where users most often clicked phishing links in WhatsApp (download)
Unlike WhatsApp, the number of phishing attacks on Telegram almost tripled in 2022 compared to the previous reporting period. On average, our solutions blocked 140 attempts to follow phishing links in this messenger per day. The peak of activity came at the end of June and beginning of July, when the number of blocked clicks could have exceeded 1,500 per week. Phishing activity on Telegram also increased sharply at the end of the year.
Dynamics of phishing activity on Telegram in 2022 (weekly number of detected links shown)
In Russia, we recorded the largest number (21,000) of attempts to click a link to fraudulent resources from Telegram. Second place went to Brazil, where 3,800 clicks were blocked.
TOP 7 countries and territories where users most frequently clicked phishing links from Telegram (download)
Conclusion
Times of crisis create the preconditions for crime to flourish, including online. Scams promising compensation and payouts from government agencies, large corporations and banks are likely to remain popular among cybercriminals next year. The unpredictability of the currency market and departure of individual companies from specific countries’ markets will likely affect the number of scams associated with online shopping. At the same time, the COVID-19 topic, popular with cybercriminals in 2020 and 2021, but already beginning to wane in 2022, will finally cease to be relevant and will be replaced by more pressing global issues.
Recently, we’ve seen an increase in targeted phishing attacks where scammers don’t immediately move on to the phishing attack itself, but only after several introductory emails where there is active correspondence with the victim. This trend is likely to continue. New tricks are also likely to emerge in the corporate sector in 2023, with attacks generating significant profits for attackers.
Spam and phishing in 2022





















































Ana Bento
I believe i’ve receaved several emails of these kind. They just keep coming!!!