
We have just detected a third FakePlayer SMS Trojan for Android phones – it’s been a month since we saw the second one. What’s new in this one?
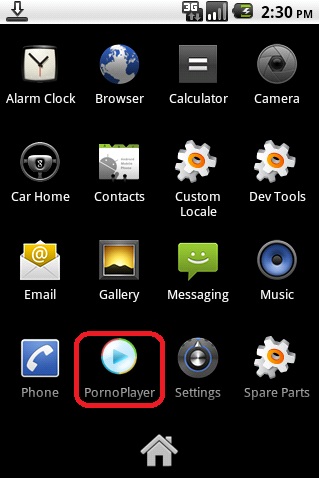
First of all, the ‘porno player’ icon from the first variant has returned.
In the second place, this variant sends for-fee SMS/text messages to two short numbers now – 7132 as in the previous version and also 4161 – new for this version.
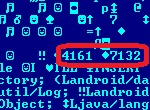
The cost for every SMS/text message remains 6 USD (about 170 Russian rubles).
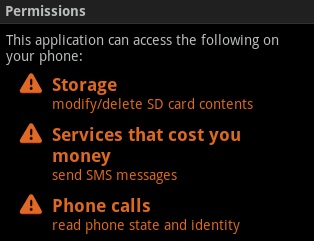
There are no other changes. The same archive – pornplayer.apk, the same infection vector – via the Internet using SEO tricks and the same queries upon installation:
So no real changes – just a new variant to earn additional money… But the trend for regular updates is a concern.
PS Everyone with a phone which supports J2ME should also beware: if you go to a website which is spreading Trojan-SMS.AndroidOS.FakePlayer.c using a mobile web browser, such as Opera Mini for instance, you will be offered a link to download a J2ME application – which happens to be a Trojan we detect as Trojan.SMS.J2ME.Small.r.






















FakePlayer: take 3