
We all know that there are many botnets (or zombie networks) all round the world. Kaspersky Lab not only detects and destroys the malware that is used to build botnets or steal confidential data, but we also look for new botnets and study their lifecycles.
Today we saw a sad, but typical picture: a small botnet with an approximately 8600 zombie machines suddenly exploded and began to grow very quickly. At first it had been growing by 5-10 new computers per day. Today the botnet grew by 4400 new zombies! The average growth rate was about 1 zombie per second!
Probably the owners of this botnet did a mass mailing of links to infected pages. Obviously, it was rather successful from the point of view of cybercriminals who own the botnet.
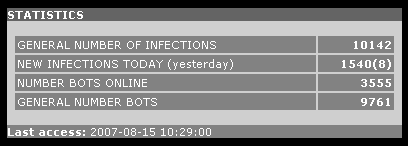
Botnet stats at 14:30 GMT:
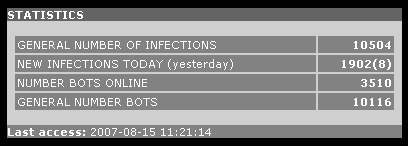
The same botnet one hour later:
Such a growth of number of zombie machines proves that the users must be very attentive while checking new emails: do not open messages from unknown senders, use only plain-text view of messages and never blindly click the links included in email messages.
More on our ongoing botnet research next week.





















A look inside a botnet