
Introduction
Although ransomware is still a hot topic on which we will keep on publishing, we also investigate and publish about other threats. Recently we explored the topic of infection methods, including malvertising and malicious downloads. In this blog post, we provide excerpts from the recent reports that focus on uncommon infection methods and describe the associated malware.
For questions or more information on our crimeware reporting service, please contact crimewareintel@kaspersky.com.
RapperBot: “intelligent brute forcing”
RapperBot, based on Mirai (but with a different C2 command protocol), is a worm infecting IoT devices with the ultimate goal to launch DDoS attacks against non-HTTP targets. We observed the first sample in June 2022, when it was targeting SSH and not Telnet services. The latest version, however, removed the SSH functionality part and now focuses exclusively on Telnet—and with quite some success. In Q4 2022, we noticed 112k RapperBot infection attempts coming from over 2k unique IP addresses.
What sets RapperBot apart from other worms is its “intelligent” way of brute forcing: it checks the prompt and, based on the prompt, it selects the appropriate credentials. This method speeds up the brute forcing process significantly because it doesn’t have to go over a huge list of credentials.
RapperBot then determines the processor architecture and infects the device. The downloading of the actual malware is done via a variety of possible commands (for example, wget, curl, tftp and ftpget). If for some reason these methods don’t work, then a malware downloader is uploaded to the device via the shell “echo” commands.
Rhadamanthys: malvertising on websites and in search engines
Rhadamanthys is a new information stealer first presented on a Russian-speaking cyber criminal forum in September 2022 and offered as a MaaS platform. According to the author, the malware:
- Is written in C/C++, while the C2 is written in Golang.
- Is able to do a “stealthy” infection.
- Is able to steal/gather information on CPU type, screen resolution, supported wallets, and so on.
- Evades EDR/AV.
- Has encrypted communication with the C2.
Despite the malware being advertised already in September 2022, we started to detect the first samples at the beginning of 2023. Although Rhadamanthys was using phishing and spam initially as the infection vector, the most recent method is malvertising.
Online advertising platforms offer advertisers the possibility to bid in order to display brief ads in search engines, such as Google, but also websites, mobile apps and more. Both search engine and website-based ad platforms are leveraged by Rhadamanthys. The trick they pull is to display ads representing legitimate applications but in fact containing links to phishing websites. These phishing websites contain fake installers, luring users into downloading and installing the malware.
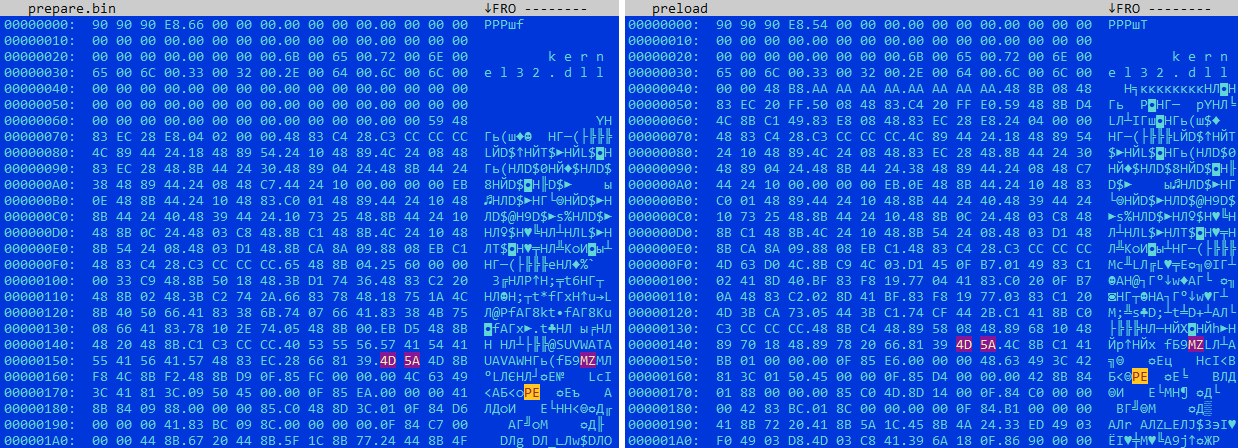
While analyzing Rhadamanthys, we noticed a strong connection with Hidden Bee miner. Both samples use images to hide the payload inside and both have similar shellcodes for bootstrapping. Additionally, both use “in-memory virtual file systems” and utilize Lua to load plugins and modules.
Comparison between Rhandamanthys’s “prepare.bin” and Hidden Bee’s “preload” modules
CUEMiner: distribution through BitTorrent and OneDrive
In August 2021, a project was started on GitHub called SilentCryptoMiner, hosting the miner consisting of a downloader and the payload, bot source and the compiled builder, as well as additional software, such as a system watcher. It has been constantly updated, with the latest update going back to October 31 2022. The repository is popular with cybercriminals, as illustrated by the huge number of samples we detected that featured many small changes and were combined with the different URLs and TTPs, making it clear that the malware is used by multiple groups in various ways concurrently.
During our investigation, we noticed two methods of spreading the malware. The first is via trojanized cracked software downloaded via BitTorrent. The other method is via trojanized cracked software that is downloaded from OneDrive sharing networks. How victims are lured into downloading these cracked packages is speculation, because we couldn’t find any direct links. Nevertheless, many crack sites these days do not immediately provide downloads. Instead, they point to Discord server channels for further discussion. This suggests some form of human interaction and social engineering.
The downloader is written in .NET and called CUEMiner. Despite being written in .NET, it is wrapped by a C++ based dropper and it connects to a set of URLs, which is varying from sample to sample, to download the miner and configuration settings. It also performs several checks in order to ensure it is running on bare metal systems, and not on a virtual machine. In case all checks are passed, the malware:
- Reconfigures Windows Defender to exclude the user profile path and the entire system drive from scanning.
- Fetches configuration details from a hardcoded URL and saves it at different places (for example, c:\logs.uce, %localappdata%\logs.uce).
- Creates empty files and subdirectories in %ProgramData%\HostData to make the directory look benign.
- Downloads the miner and watcher.
- Does a number of other things. The full list you can find in our private report.
The watcher, as the name suggests, monitors the system. If it doesn’t detect any processes that consume lots of system power (for example, games), the miner software is launched. When a heavy process, such as a game, is started, the miner is stopped and only started again when the aforementioned process stops. This is done in order to stay undetected on the system longer.
Conclusion
Open source malware is often used by less skilled cybercriminals. They often lack the required skills and contacts to conduct massive campaigns. Nevertheless, they can be still quite active and effective, as is shown by the huge number of CUEMiner samples we detected. If along their cybercriminal career they gain more skills, such as programming and understanding security better, they often reuse and improve crucial source code parts from open source malware.
Code reuse and rebranding is also used quite often by cybercriminals. There are many ransomware variants that change names over time while mostly containing the same code base. In other cases, cybercriminals re-use parts of the code in new campaigns. For example, Rhadamantys stealer features some code overlaps with the Hidden Bee malware. This suggests involvement of at least one individual in the Rhadamantys campaign who had also been involved in the development of Hidden Bee.
To protect yourself against these threats, intelligence reports can help. If you want to stay up to date on the latest TTPs used by criminals or have questions about our private reports, please contact crimewareintel@kaspersky.com.






















Uncommon infection methods—part 2