
Today, cybercriminals are quick to exploit vulnerabilities in Adobe Reader, Flash and Java to infect users’ computers. There is a simple reason for this popularity: exploits of vulnerabilities found in these products can infect computers regardless of which operating systems and browsers are used on the attacked machines. We assumed that the threats posed to users were unaffected by their choice of browser and undertook a little research to test this assumption.

Picture courtesy of the PCMAG website
Source of data
KSN, Kaspersky Lab’s cloud service, collects anonymous statistics about any threat detected on the computers of those who agree to have their data collected and transferred. This information is subsequently used to block unknown malicious programs, which is again done via the cloud.
For research purposes, we singled out 10.5 million computers in various locations around the globe. These computers regularly supply KSN (http://ksn.kaspersky.com) with information about malicious code detected on the Internet.
When web-based threats such as malicious scripts, exploits and infected files are detected on a server, etc. by a web browser that is trying to access them, KSN receives information about the name of the browser and its MD5. By analyzing the KSN data, we can obtain statistics about the browsers installed on our client’s computers.
The most popular browser
For starters, here are the figures showing the popularity of different browsers installed on our sample computers:
| Browser | Number of users |
| CHROME | 3 472 506 |
| INTERNET EXPLORER | 3 324 190 |
| FIREFOX | 3 096 316 |
| OPERA | 1 575 880 |
| SAFARI | 7648 |
| Total number of users | 10406291 |
The popularity rating for browsers installed on users’ computers
Google Chrome has the highest number of users. This result is in line with the findings of several other studies (http://en.wikipedia.org/wiki/Usage_share_of_web_browsers).
We also found that:
- Only about 10% of users simultaneously use two or more browsers on the same computer;
- In 50-60% of cases, the latest versions of browsers are installed on computers.
Browser preferences
We looked at which browsers are installed by users according to operating system.
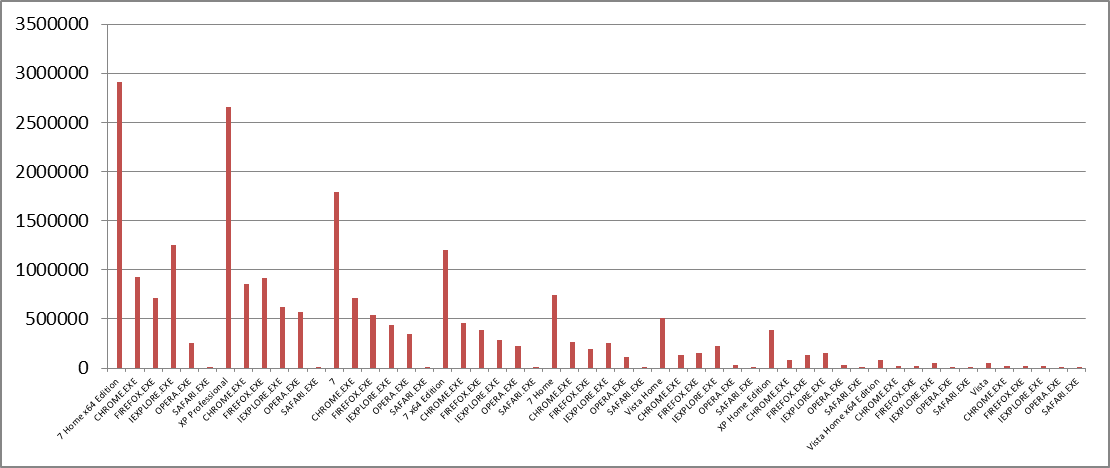
Information about the operating systems and browsers installed on users’ computers
In this diagram, we see that most computers in our selection run home versions of Windows 7 x64. On these computers, Internet Explorer is the leading browser. Internet Explorer also enjoys great popularity with the users of other home versions of Windows 7, Windows Vista and Windows XP.
Firefox most often runs under Windows XP Pro, Chrome typically runs under professional versions of Windows 7.
It should be noted that “home” versions of operating systems are typically used by regular home users. Professional versions of Windows XP and Windows 7 are generally preferred by so-called “advanced” users.
What are the threats?
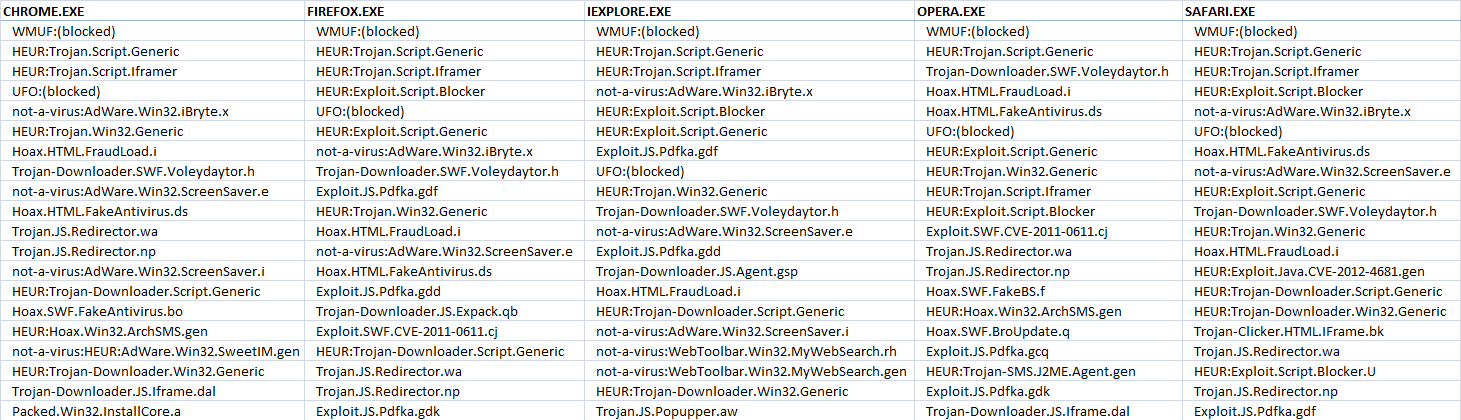
Continuing our research, we compiled ratings for the threats most often encountered by the users of each browser.
TOP 20 threats facing users of each browser
In the leading positions in the Top 20 we find antivirus verdicts which indicate groups of malicious objects:
WMUF:(blocked) – malicious sites blocked for access.
HEUR:Trojan.Script.Generic – malicious scripts.
HEUR:Trojan.Script.Iframer – scripts that return IFRAMEs to infected sites.
UFO:(blocked) – malicious sites or files to which access was blocked by the cloud.
HEUR:Trojan.Win32.Generic – files exhibiting malicious behavior.
In these ratings, we also see which malicious programs are most often detected on the computers of users who use specific browsers.
On the computers of Firefox users, exploits of vulnerabilities in Adobe software are most often detected: Exploit.JS.Pdfka, Trojan-Downloader.JS.Expack, Exploit.SWF.CVE-2011-0611.
The users of Chrome most often encounter unwanted adware: not-a-virus:AdWare.Win32.iBryte, not-a-virus:AdWare.Win32.ScreenSaver, not-a-virus:HEUR:AdWare.Win32.SweetIM.
The users of Internet Explorer most often encounter the adware browser extension not-a-virus:WebToolbar.Win32.MyWebSearch and the malicious adware Trojan.JS.Popupper.
Opera users are more likely than others to encounter the malicious program Trojan-Downloader.SWF.Voleydaytor.h, which is deployed by cybercriminals on compromised sites.
Nothing in particular stood out when it came to malware statistics for SAFARI users.
The differences in these lists of malware are partly accounted for by browser operation quirks, e.g. in the way browsers handle PDF files or use ‘sandbox’ technology.
The results are also affected by different online behavior exhibited by different categories of users. ‘Advanced’ users, for instance, are more active online compared to home users, and are more likely, therefore, to end up on sites containing exploits.
Number of repelled attacks
Let us compare the number of notifications about repelled attacks in browsers.
| Browser | Number of blocked attacks |
| CHROME.EXE | 73770843 |
| FIREFOX.EXE | 65941246 |
| OPERA.EXE | 52931615 |
| IEXPLORE.EXE | 33892596 |
| SAFARI.EXE | 114526 |
| Total | 226650826 |
Number of threats blocked in browser
Although Internet Explorer is the second most popular, it is second to last in terms of blocked threats.
If we compare the number of attacks that an average user of each browser encountered in September, we get the following picture:
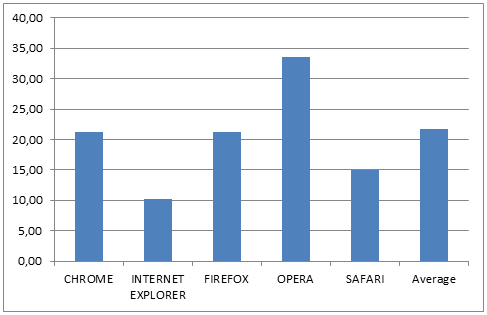
Average number of blocked threats per browser user
As seen in the diagram, the average numbers of attacks repelled on the computers of Chrome and Firefox users are very similar, and almost the same as the average for all browser users.
Internet Explorer users faced the fewest attacks, while Opera users had to deal with the most.
We can presume that home users who prefer Internet Explorer typically visit a limited number of popular sites. Consequently, their computers are less frequently attacked by cybercriminals than the computers of ‘advanced’ users of other browsers who tend to display riskier online behavior.
Conclusions
In conclusion, we would like to make a few important points:
- Chrome is the most popular browser among the users of Kaspersky Lab products included in our selection.
- Users who user home versions of Windows are more likely to use Internet Explorer.
- Opera users, on average, face the highest numbers of repelled attacks.
- There was no evidence of targeted attacks which cybercriminals used against specific browsers. However, there are specific profiles of online threats associated with groups of users of each popular browser. These associations reflect the use of security technologies in respective browsers, and their users’ online characteristics.
Naturally, this research is not complete as there was no analysis of the geographic distribution of browser users; also, the threats lumped together under heuristic and behavior verdicts require further analysis. This may be the subject of future publications. For now, I would like to thank Yuri Namestnikov and Kaspersky Lab’s Database Design and Development Group , whose participation was essential throughout this research!





















KSN: An Analysis of Web Browsers